HIPAA Compliance in 3 Months: A Real MSP Case Study
Why MSPs Need HIPAA Compliance
Jones IT started in 2002 when Evan Jones set up shop in a garage with a simple mission to help Bay Area companies navigate the complexities of technology. Over two decades, we've grown into one of the region's most trusted IT services firms, serving all types of companies, from scrappy 20-person startups to established enterprises with thousands of employees.
Our client roster reads like a cross-section of San Francisco's tech ecosystem: fintech companies, AI startups, biotech firms, engineering teams, and nonprofits. We'd built our reputation on being the IT partner you could count on when the stakes were high and the technical challenges were complex.
But we noticed something shifting in our prospect conversations. More and more prospective clients were asking about healthcare data. The lines between "tech company" and "healthcare company" were blurring fast, and suddenly almost everyone was asking if we were HIPAA.
Although we’re already SOC 2 compliant and ISO 27001 certified, we knew these were not going to be enough. We wanted to demonstrate our commitment to our healthcare clients and prospects through solid evidence, not just reassurances. Hence, we decided to get HIPAA attestation from a certified auditor.
| SOC 2 | ISO 27001 | HIPAA | |
|---|---|---|---|
| Primary Focus | Service organization controls & trust | Information security management | Protected health information |
| Key Requirements | Trust Service Criteria (security, availability, confidentiality) | 114 controls across 14 domains | Security, Privacy & Breach Notification Rules |
| Audit Type | Independent CPA audit | Accredited certification body | Optional third-party attestation |
| Typical Timeline | 6-12 months | 9-18 months | 3-6 months (with foundation) |
| Industry Focus | SaaS, Cloud, Service Providers | All industries globally | Healthcare (US requirement) |
| Unique Aspects | Observation period (Type 2) | Risk-based approach, context-driven | Business Associate Agreements (BAAs) |
HIPAA Compliance Requirements: Challenges Beyond SOC 2 and ISO 27001
“How hard can it be? HIPAA is just another security framework, right?"
While, HIPAA is, in fact, a security framework, it's fundamentally different from SOC 2 or ISO 27001 in ways that became clear only when we started digging into the specifics. We learned that HIPAA wasn't just about securing data; it was about securing Protected Health Information(PHI) with very specific rules about who could access it, how it could be used, when breaches needed to be reported, and what responsibilities we had as a business associate.
While SOC 2 had taught us about confidentiality and availability, and ISO 27001 had instilled rigorous information security management practices, HIPAA introduced concepts like "minimum necessary access" and "Business Associate Agreements" that required entirely new policies, processes, and legal frameworks.
Our GRC (Governance, Risk, and Compliance) engineer spent a week mapping our existing controls against HIPAA requirements. The good news was that about 78% of security controls we already had satisfied HIPAA's technical safeguards. Our encryption was solid, our access controls were robust, and our incident response procedures were well-documented.
Still, the concerning news was that the remaining 22% represented significant work. We needed HIPAA-specific risk analyses, breach notification procedures that met federal timelines, and audit every vendor relationship, determining whether Business Associate Agreements were required. Additionally, we needed training programs that went beyond general security awareness to cover specific HIPAA privacy rules.
And we decided to get it all done in six months.
We had a pipeline of healthcare prospects representing significant revenue, and every month we delayed was another month of competitive disadvantage against IT providers who'd gotten ahead of this trend. Although the timeline was aggressive, we felt confident since we'd navigated complex compliance projects before. Moreover, we knew we couldn't afford to treat this as a leisurely two-year initiative, because Healthcare was moving too fast.
How We Overcame The HIPAA Compliance Challenges
Instead of treating HIPAA as an isolated compliance project, we implemented a strategic, integrated approach, combining the three key elements, : expert healthcare auditing, compliance automation, and intelligent control alignment.
Choosing a HIPAA Audit Partner: Why Healthcare Expertise Matters
Over the years, we've maintained a strong partnership with Boulay. They've consistently delivered efficient audits with high-quality reports for both our SOC 2 and ISO 27001 certifications. So, we were confident that their deep expertise in healthcare regulatory frameworks would prove invaluable when interpreting the nuances of HIPAA Security and Privacy Rules, particularly around Protected Health Information (PHI) handling and breach protocols.
While third-party audits aren't strictly required for HIPAA compliance, we recognized that formal attestation from a certified auditing body would provide assurance to both current and future clients. This external validation became a key differentiator in our sales process, immediately eliminating buyer concerns around our compliance posture.
Through a collaborative audit readiness process, Boulay helped us identify areas of overlap with SOC 2 and ISO 27001 controls: elements like access control, data encryption, and incident response that satisfied multiple frameworks. They also advised on HIPAA-specific additions, including risk analyses tailored to PHI environments, employee HIPAA awareness training programs, and the creation of formal Business Associate Agreements (BAA) with downstream vendors.
HIPAA Compliance Automation: How We Cut Our Timeline in Half
To reduce manual workload and increase audit efficiency, we implemented Drata's HIPAA framework into our existing tenant. We were already using Drata for SOC 2 and ISO 27001, which meant we could leverage the same platform rather than introducing new tools and training overhead.
Drata's automation capabilities enabled us to automate evidence collection for more than 80 controls, including password policies, system configurations, and access logs. The platform monitored HIPAA controls in real-time, surfacing non-compliant items proactively before they could become audit issues. All documentation was centralized in a unified compliance dashboard accessible to both leadership and auditors, and employee onboarding and policy acknowledgment were streamlined using pre-built workflows and tracking tools.
Within just weeks, we had automated much of what would otherwise have been time-consuming audit preparation work. The real breakthrough came from how Drata mapped our existing SOC 2 and ISO 27001 controls to HIPAA requirements, allowing us to see exactly where we had coverage and where gaps existed.
Mapping and Enhancing Controls Strategically
With guidance from Boulay and automation from Drata, our internal compliance team focused on mapping existing controls to HIPAA requirements. This exercise revealed that 78% of our controls mapped directly or with minor modifications, meaning we had a significant head start that would have been impossible without our prior compliance investments.
The remaining 22% required new documentation or additional technical measures. These HIPAA-specific requirements included periodic risk assessments tailored to PHI environments, role-based access models ensuring minimum necessary data exposure, enhanced incident response protocols with timelines for HIPAA breach notification, and logging and monitoring improvements to meet audit trail requirements.
Where gaps were identified, we swiftly implemented process changes. For instance, we moved from quarterly to monthly access reviews for systems handling PHI, recognizing that HIPAA's risk-based approach demanded more frequent oversight. We also strengthened our vendor management policies to require BAAs and security due diligence for any partner that might handle protected health information.
The Five-Phase Implementation Process
Our path to HIPAA compliance followed a structured five-phase approach that balanced speed with thoroughness. Each phase built on the previous one, creating momentum while ensuring nothing critical was overlooked.
Phase 1: Assessment and Control Mapping
We began with a comprehensive gap assessment using Drata's HIPAA framework module. The system automatically mapped our existing SOC 2 and ISO 27001 controls to HIPAA's Security, Privacy, and Breach Notification Rules, identifying overlaps and highlighting missing elements.
This phase revealed that 78% of existing controls mapped directly or with minor modifications, while 22% required new documentation or additional technical measures. Boulay provided a customized HIPAA control checklist aligned to our specific services and infrastructure, which became our roadmap for the remaining phases.
We also conducted a risk analysis workshop where we identified PHI data flows, assessed vulnerabilities, and documented mitigation strategies. This satisfied HIPAA's core risk analysis requirements while providing a clear picture of where additional safeguards were needed.
Phase 2: Policy Development and Internal Enablement
Next, our compliance and operations teams collaborated to develop and refine HIPAA-specific policies and procedures. We used Drata's policy library as a starting point for creating our Breach Notification Policy and Business Associate Policy, customizing them to reflect our actual operational practices rather than generic templates.
We integrated KnowBe4, a learning management platform, with Drata to assign and track HIPAA training completion for all staff. Within three weeks, 100% of employees had completed mandatory training, and all formalized policies were signed and acknowledged via Drata's policy workflow tool.
This phase also introduced a new vendor onboarding checklist to ensure BAA compliance. Every vendor relationship was reviewed to determine whether a BAA was required, and we began the process of securing signed agreements with all partners who handled or had access to PHI.
Phase 3: Technical Safeguards Implementation
With policies in place and staff trained, we focused on the technical safeguards required by HIPAA. We enforced TLS encryption on all incoming and outgoing email communications, adjusted our existing Data Loss Prevention (DLP) category detection rules to scope in PHI, and verified that our audit logging and alerting for administrative access and PHI system usage were adequate and stored in immutable log storage for retention requirements.
These technical implementations were relatively straightforward because our underlying security infrastructure was already robust from SOC 2 and ISO 27001. We weren't rebuilding systems, just refining configurations and adding PHI-specific monitoring.
Phase 4: Internal Audit Review
Before engaging in formal external audit activities, our compliance team conducted an informal internal audit to identify any remaining gaps. We simulated evidence submission for HIPAA controls using Drata's interface, conducted an internal review of vendors to verify BAA coverage, and performed policy and system walkthroughs to verify audit trail completeness and role-based access configurations.
This internal review surfaced a few minor issues, primarily documentation gaps rather than control failures, which we addressed before the formal audit began. This preparation proved invaluable during the actual audit, as we encountered no surprises.
Phase 5: Formal Audit and Attestation
Finally, we underwent a formal HIPAA compliance assessment with Boulay. Thanks to our preparatory work and the real-time visibility offered by Drata, the audit process was efficient and stress-free. We completed the full audit in under one week, submitted 100% of control evidence digitally via Drata, and received our attestation with zero exceptions noted.
The successful attestation was delivered well within schedule, allowing us to meet our business objectives and immediately showcase HIPAA compliance in marketing materials and sales conversations.
Is HIPAA Compliance Worth It? Calculating Real ROI
Audit Success
Completing HIPAA compliance delivered tangible business and operational gains that extended well beyond the certification itself.
From an audit perspective, we achieved 100% control coverage with zero exceptions noted by Boulay, and over 80% of the required evidence was automatically collected through Drata, dramatically reducing manual documentation effort. What we initially estimated as a six-month project was completed in just three months, allowing us to enter the healthcare market sooner than anticipated.
Expanded Market Access And Revenue Growth
The business impact was equally significant. We closed two new healthcare client contracts within 60 days of achieving HIPAA compliance, and shortened sales cycles by 30% for healthcare prospects, as HIPAA attestation eliminated the most common buyer objection around regulatory risk. The HIPAA compliance badge became a differentiator in a highly competitive market, helping us win business over less-regulated competitors who couldn't provide the same assurances.
Enhanced Security Posture and Risk Reduction
Our security posture strengthened measurably as well. We cut the average incident response time from four hours to 1.5 hours through revised protocols and automated monitoring. We completed our first formal HIPAA risk analysis, identifying and implementing treatment plans for two previously unrecognized risks. And we reinforced our vendor management framework, ensuring all partners handling PHI have signed BAAs and meet minimum security requirements.
Culture of Compliance
Perhaps most importantly, we transformed compliance from a periodic task into a continuous business enabler. We achieved 100% employee HIPAA training completion across departments within three weeks, instituted a quarterly internal control review cadence to maintain compliance year-round, and integrated HIPAA practices into day-to-day operations, reinforcing a compliance-first mindset throughout the organization.
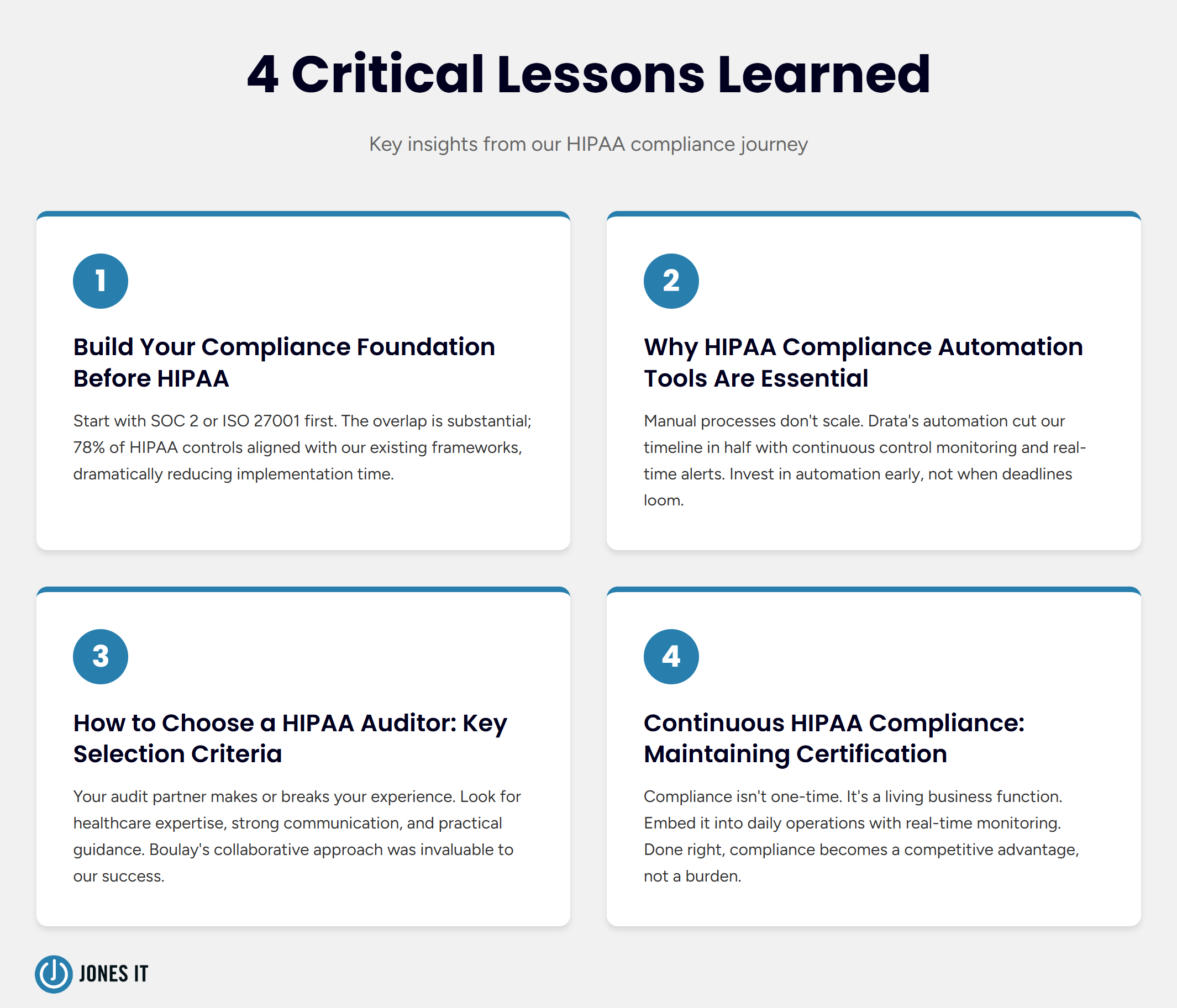
What We Actually Learned From Our HIPAA Journey
Our journey toward HIPAA compliance reshaped how we approached risk, governance, and operational excellence. Four key lessons emerged that can benefit any organization pursuing similar goals.
1. Build Your Compliance Foundation Before HIPAA Compliance
One of our biggest advantages was prior investment in SOC 2 Type II and ISO 27001 compliance. These frameworks had already instilled a culture of security and accountability, meaning teams were familiar with evidence collection, policy management, and audit preparation. This foundational maturity greatly reduced the effort required for HIPAA. If you're considering HIPAA in the future, start with SOC 2 or ISO 27001 first, because the overlap is substantial, and you'll build critical organizational capabilities.
2. Why HIPAA Compliance Automation Tools Are Essential
Manual compliance processes don't scale well and don't inspire auditor confidence. Drata's automation enabled continuous control monitoring, alerting our team to compliance drift in real-time. Without automation, this project could easily have taken twice as long. Invest in a modern compliance automation platform early in your journey, not just when a certification deadline looms.
3. How to Choose a HIPAA Auditor: Key Selection Criteria
Your audit partner can make or break your compliance experience. Boulay's deep understanding of HIPAA, strong communication practices, and practical recommendations tailored to our environment proved invaluable. They provided HIPAA-specific readiness checklists based on real-world audit experience and understood the nuances of multi-tenant environments and third-party vendors. A collaborative and knowledgeable auditor isn't just a checkbox, but a partner in your success.
4. Continuous HIPAA Compliance: Maintaining Certification
Perhaps the most enduring lesson is that compliance isn't a one-time effort; it's a living function of the business. By embedding compliance into daily operations and leveraging real-time monitoring, we ensured ongoing control effectiveness, faster response to policy changes or client requests, and long-term resilience in a highly competitive landscape. Compliance done right becomes a competitive advantage, not a burden.
This blog post is an excerpt from our comprehensive case study on our HIPAA Compliance Journey. Get access to the full case study documenting the processes, tools, timelines, and more...
Taking the First Step Toward HIPAA Compliance
Achieving HIPAA compliance isn't just about checking regulatory boxes; it's about making your organization a stronger, more trustworthy technology partner. With the right strategy, partners, and tools, compliance becomes a driver of growth, trust, and operational excellence.
If you're considering HIPAA compliance for your organization, start by assessing your current security posture. Do you have foundational frameworks like SOC 2 or ISO 27001 in place? Are you collecting and storing evidence in a structured way? Have you identified which systems and data flows involve protected health information?
The journey may seem daunting, but organizations with existing compliance programs can leverage that foundation to accelerate HIPAA readiness significantly. Focus on control mapping first to understand your gaps, invest in automation to reduce manual burden, and partner with auditors who understand your industry and business model.
At Jones IT, our HIPAA compliance journey wasn't just about passing an audit. It was about making us a stronger, more trustworthy IT partner for healthcare businesses. The certification opened doors to new markets, shortened sales cycles, and strengthened our internal security practices in ways that benefit all our clients, not just those in healthcare.
Whether you're navigating HIPAA requirements for the first time or looking to enhance your existing security posture, the path forward begins with strategic planning, the right partners, and a commitment to treating compliance as a business enabler rather than a burden. The healthcare market isn't getting any less regulated, and the organizations that get ahead of these requirements will be the ones that thrive.
Ready to strengthen your IT compliance and security? Jones IT offers comprehensive compliance support and fully managed IT services designed to meet the highest standards of privacy, security, and operational excellence. From secure infrastructure design and policy development to continuous compliance monitoring and audit readiness, we can guide you through every step of your HIPAA journey. Contact us today to schedule a consultation.