Blog
Explore our insights on IT solutions and business growth.
Discover valuable information and stay informed on the latest industry developments.
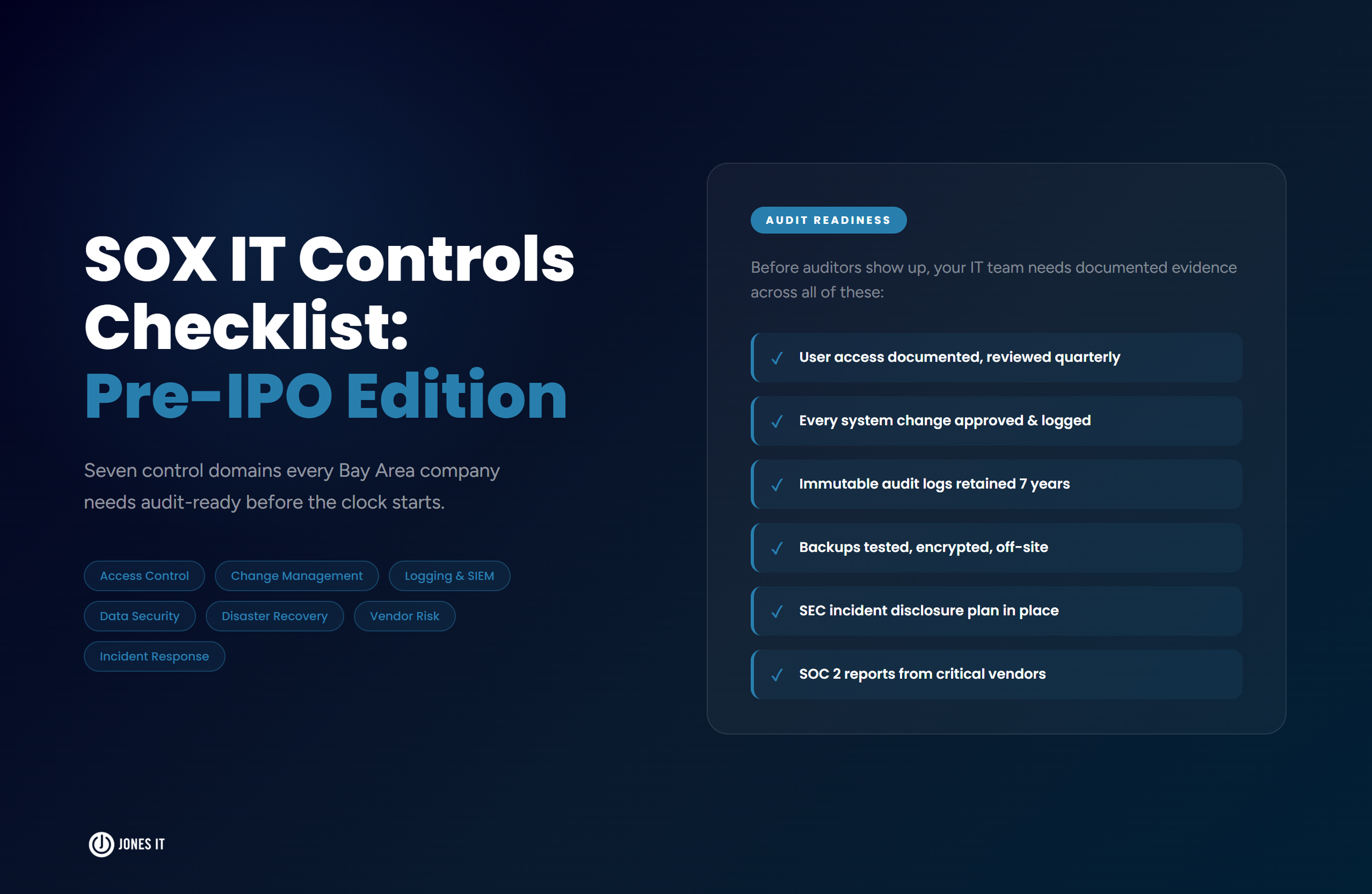
SOX IT Controls Checklist: What Every Pre-IPO Company Needs
The SOX IT controls checklist covers seven domains: access management, change management, logging, data security, disaster recovery, vendor risk, and incident response. Built for pre-IPO Bay Area companies getting audit-ready.
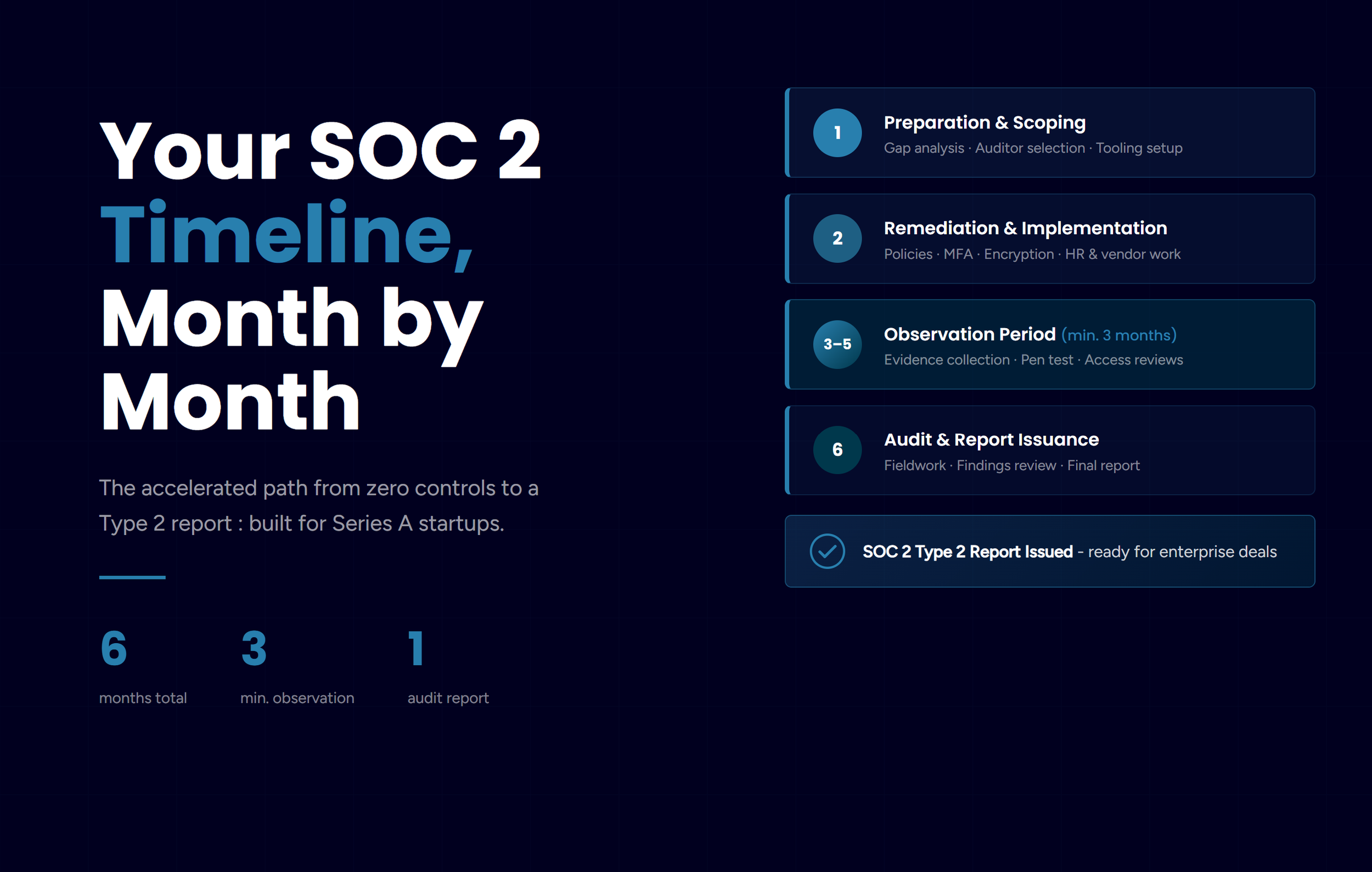
SOC 2 Compliance Timeline: Month-by-Month Roadmap for Series A Startups
A realistic month-by-month SOC 2 Type 2 roadmap for Series A startups, covering scoping, remediation, the observation period, and audit. Includes budget estimates and the pitfalls to avoid.
SOC 2 Type 1 vs Type 2: Which Does Your Startup Actually Need?
SOC 2 Type 1 vs Type 2: Jones IT explains the key differences, when each type makes sense for startups, and how to choose the right path for enterprise sales.
HIPAA Compliance in 3 Months: A Real MSP Case Study
Real story of achieving HIPAA compliance in 90 days using automation and smart strategy. A practical guide to certification, automation, and avoiding costly mistakes.
ISO 27001 in 6 Months: How We Achieved Enterprise-Grade Security Compliance
ISO 27001 in 6 months: Our complete roadmap from SOC 2 to ISO 27001 certification. Tools, timeline, budget insights, and lessons for SME compliance.
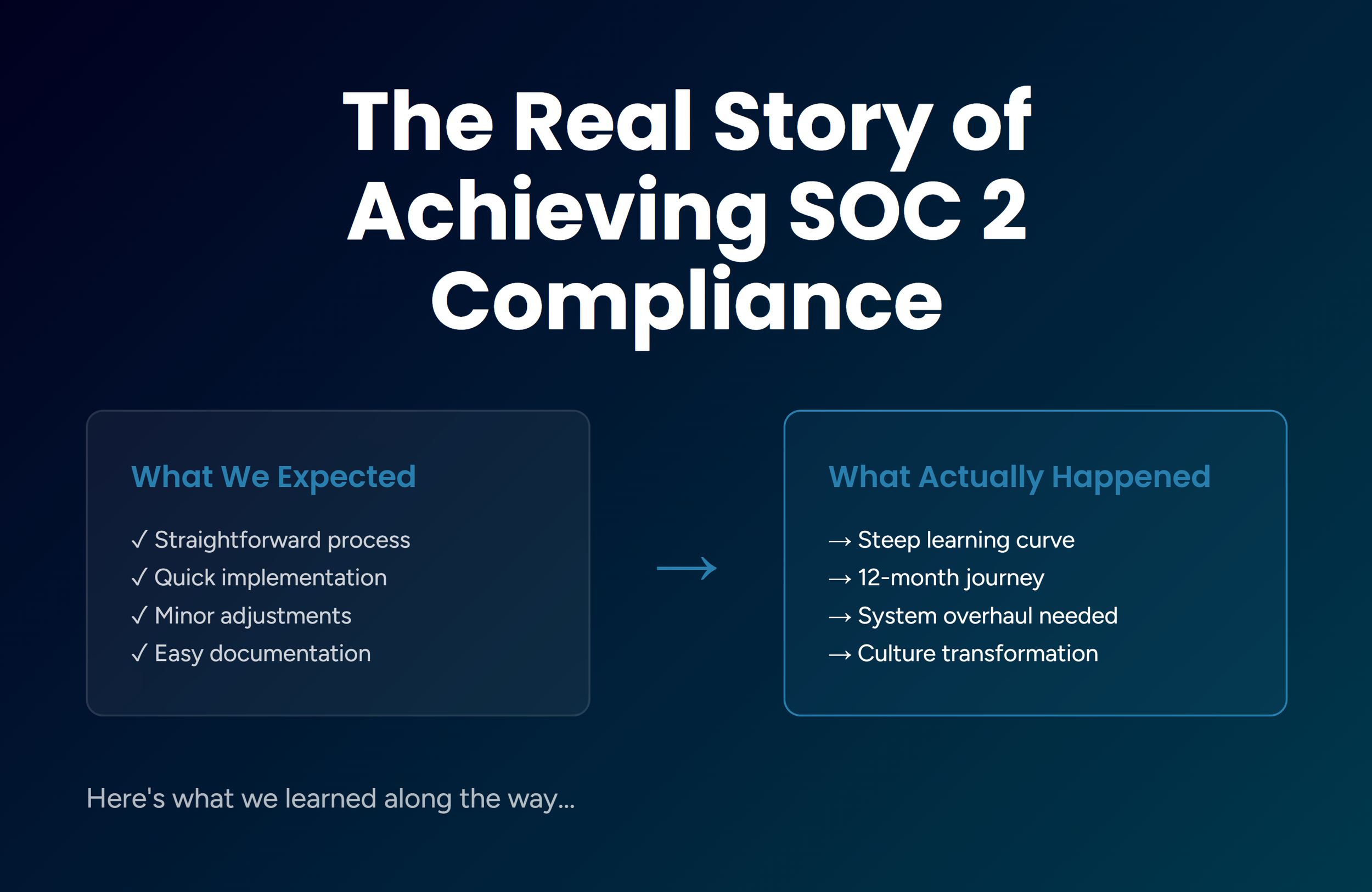
The Real Story of Achieving SOC 2 Compliance: What We'd Do Differently
The real story of achieving SOC 2 Type 2 compliance: 4 major obstacles, tools that worked, and 5 lessons that could save your startup months of effort.
How Jones IT Ensures Security and Compliance for Our Clients
This blog post discusses how our security and compliance services help businesses balance security and compliance while focusing on resilience and scalability.
Common IT Security Standards, Regulations, And Frameworks
This blog post provides an overview of common IT security standards, regulations, and frameworks along with an introduction to the most common IT security standards, regulations, and frameworks.
How Does Being Fully Remote Impact SOC 2 Compliance?
In this blog post, we take a look at how being fully remote can impact your organization’s SOC 2 compliance process and what you can do to make the process easier.
Challenges Of Growing A Business And How To Overcome Them
In this blog post, we look at the most common challenges to business growth and how to effectively tackle them.
PCI Compliance Guide For Small Businesses
This article is a quick-start guide to PCI DSS compliance, its requirements, security controls, processes, and steps to prepare your IT systems for compliance.
What Is The ISO/IEC 27001 Information Security Management Standard
This blog post talks about the ISO/IEC 27001 standard, how it works, the benefits of getting the certification, and how to start the ISO 27001 certification process.
What Is The NIST Cybersecurity Framework And How To Get Started
This blog post talks about the NIST Cybersecurity Framework, its components, elements, compliance requirements, and a step-by-step process for implementing it.
How To Perform A Cybersecurity Risk Assessment
Cybersecurity risk assessments help you reach an acceptable level of information security risk without blowing up your budget. An ideal assessment helps improve your IT security cost-effectively and without impacting your productivity and effectiveness of operations. Here’s how you can get started.
What Is HIPAA Compliance? Requirements, Risk Assessment, and How to Get Started
HIPAA compliance requires covered entities and business associates to protect patient health information through documented safeguards, risk assessments, and annual audits. Here’s what the law requires and how to get started in the Bay Area.
What Is SOC 2 Compliance? A Complete Guide for Startups
Complete SOC 2 guide for startups: what it is, Type 1 vs Type 2, real costs ($75K-$200K), 12-month timeline, and step-by-step roadmap from a company that's done it.
How To Become California Consumer Protection Act (CCPA) Compliant
The California Consumer Privacy Act (CCPA) empowers consumers by giving them ownership of their data. More importantly, it puts a greater onus on companies for the security of their consumers’ data. Let’s evaluate the key compliance challenges and how to overcome them.
Get In Touch
Schedule a Call with our experts
Get a free consultation and see how Jones IT can tailor solutions to your specific business needs.