ISO 27001 in 6 Months: How We Achieved Enterprise-Grade Security Compliance
When prospective clients ask about our security credentials, we don't just talk about best practices; we show them our ISO 27001 certification. It's the international gold standard for information security management, and achieving it transformed not just our security posture, but our entire approach to risk management and operational excellence.
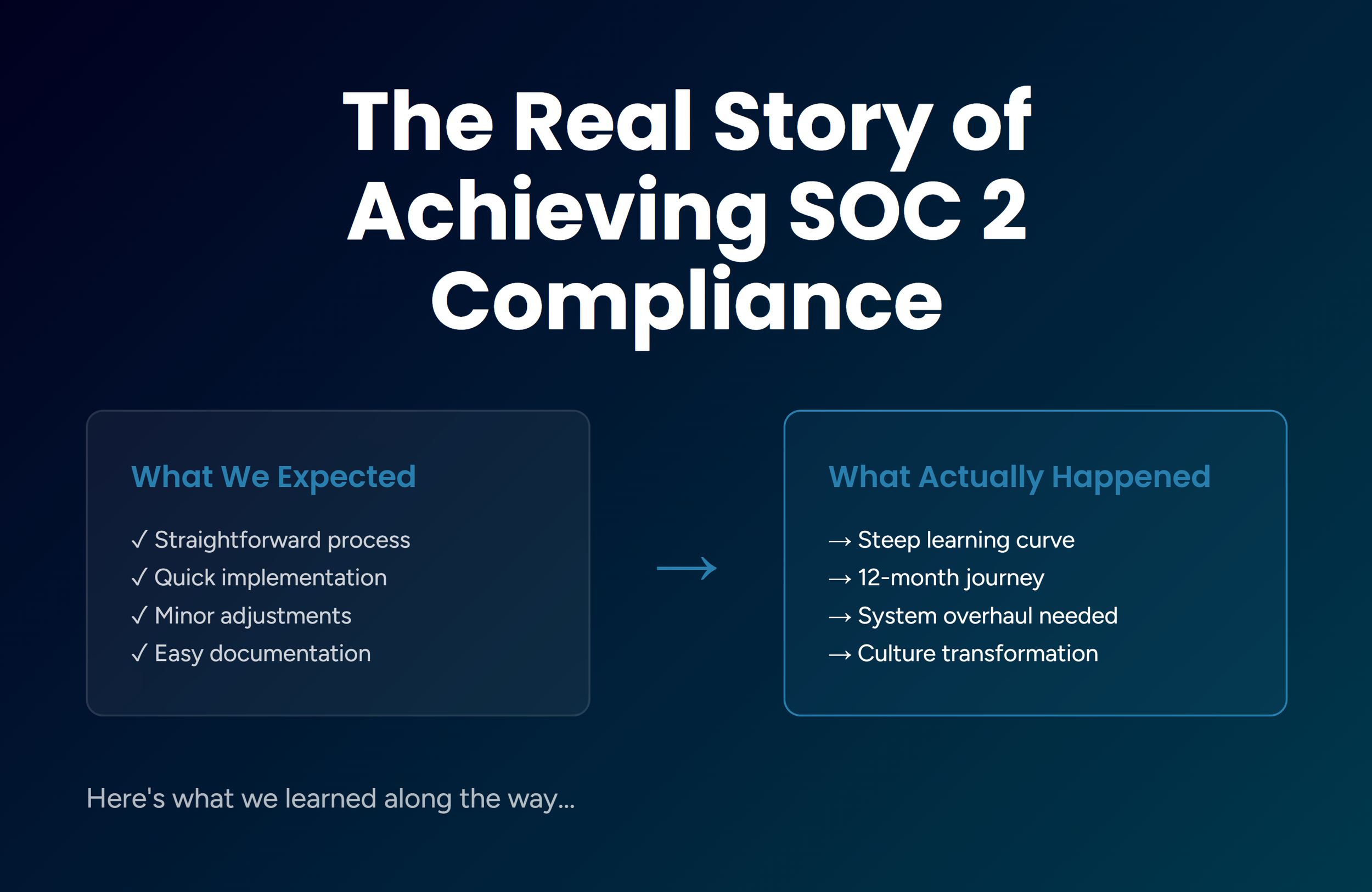
After we achieved SOC 2 compliance, we further strengthened our security, and this led us to ISO 27001. But here's what most compliance guides didn't tell us: the journey from SOC 2 Type 2 to ISO 27001 wasn't just about checking boxes. It was about fundamentally maturing our organization's security practices while building trust, which helped open doors to enterprise clients and regulated industries.
In this post, we'll walk you through exactly how we achieved ISO 27001:2022 certification in just six months, half the typical timeline, and why this matters for any growing business that takes security seriously.
Why ISO 27001 Matters More Than Ever
If you're serving clients in finance, healthcare, or any regulated industry, you've probably encountered the ISO 27001 question. It's no longer just a nice-to-have and is increasingly becoming table stakes for enterprise deals.
ISO 27001 demonstrates your commitment to managing information security risks through:
Establishing a comprehensive Information Security Management System (ISMS) that governs how you handle sensitive data;
Becoming genuinely risk-aware rather than just reactive to security incidents;
Proactively identifying and addressing weaknesses before they become breaches;
Taking a holistic approach to information security across your entire organization.
For Jones IT, pursuing ISO 27001 after achieving SOC 2 Type 2 compliance was a strategic business decision driven by three factors:
1. Client Demand for Security Assurance
Our clients in fintech, healthcare, and SaaS increasingly required vendors to demonstrate robust security management systems. While SOC 2 Type 2 addressed many concerns, ISO 27001's international recognition and comprehensive scope provided the elevated assurance that enterprise clients demanded.
2. Competitive Differentiation
Achieving ISO 27001 certification requires significant investment in time, resources, and organizational commitment. As one of the few Managed IT Services Providers holding both ISO 27001 and SOC 2 certifications, we gained a powerful differentiator in a crowded market where security claims are easy to make but hard to verify.
3. Building Client Trust
Beyond any single client requirement, ISO 27001 certification demonstrates a commitment to security risk management that builds customer trust. For businesses in highly regulated industries, this commitment isn't just appreciated but essential for partnership.
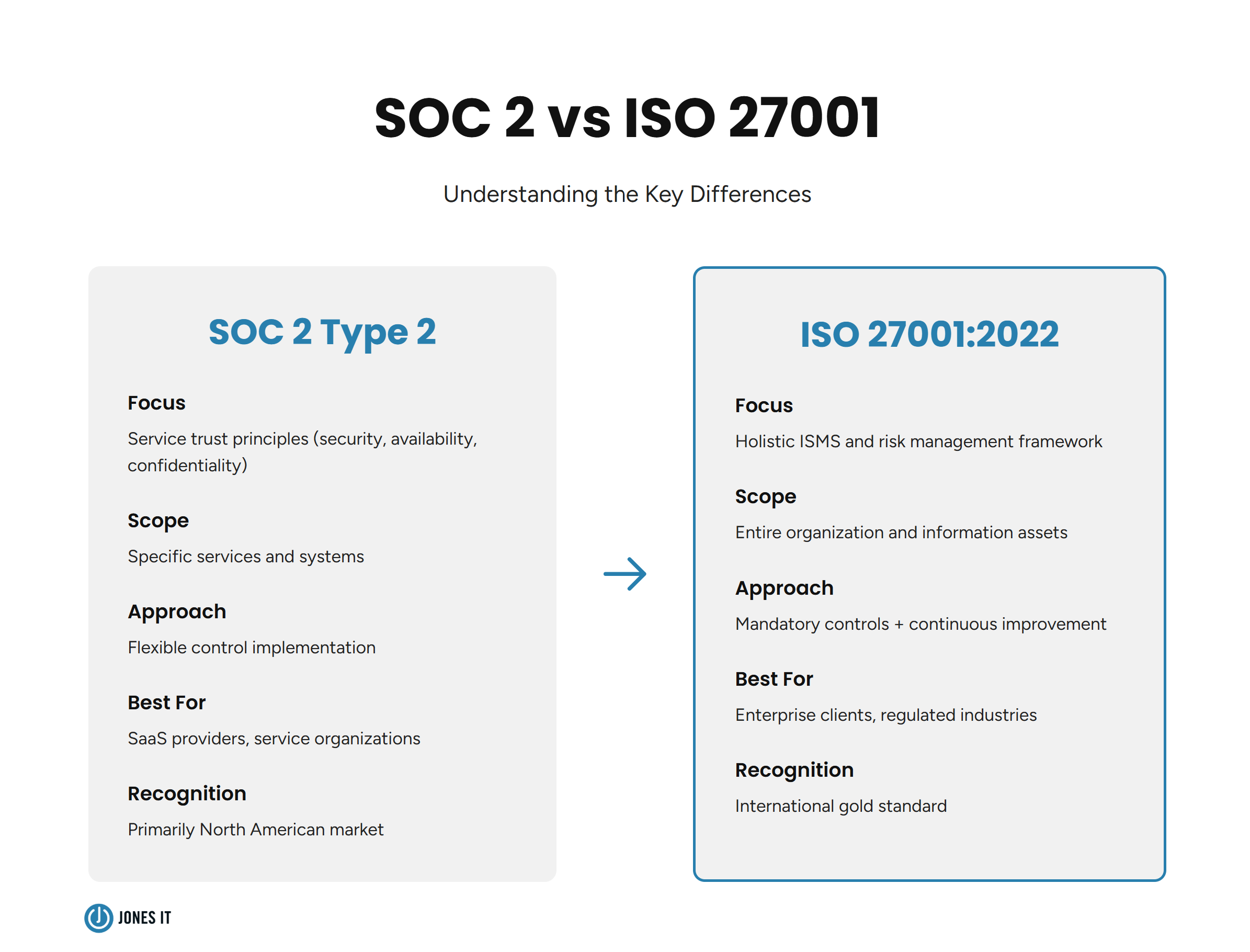
The SOC 2 Foundation
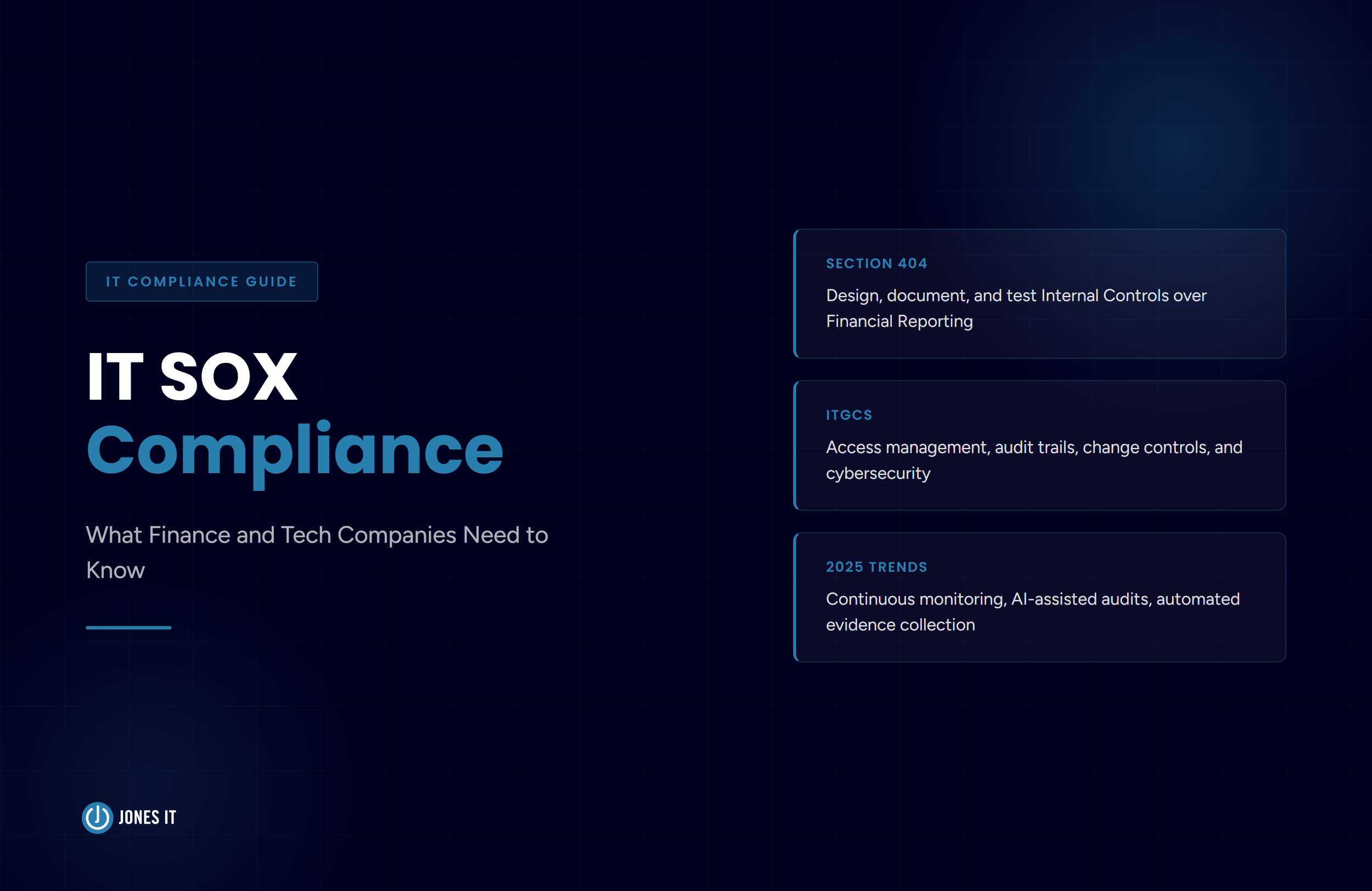
Before diving into our ISO 27001 journey, let’s take a moment to understand why we first pursued SOC 2 Type 2 compliance. SOC 2 focuses on service trust principles, namely, security, availability, processing integrity, confidentiality, and privacy. Hence, it's particularly well-suited for service organizations and SaaS providers.
The SOC 2 certification gave us:
A solid foundation in security controls and documentation,
Experience with external audits and evidence collection,
Established policies for access control and incident response, and
Automated compliance monitoring through our GRC (Governance, Risk, and Compliance) platform.
This foundation proved invaluable as without SOC 2 as our starting point, achieving ISO 27001 in six months would have been nearly impossible.
Our 4-Step Roadmap
Here's the strategic approach we took to transition from SOC 2 Type 2 to ISO 27001:2022 certification:
Step 1: Conducting a Comprehensive Gap Assessment
The first step was understanding exactly what separated our SOC 2 compliance from ISO 27001 requirements. While both frameworks share substantial control overlap, they differ significantly in scope and approach.
While SOC 2 focuses on service trust principles with flexibility in implementation, ISO 27001 emphasizes a holistic Information Security Management System with mandatory controls, continuous improvement, and broader organizational scope.
During our gap assessment, we documented key areas of alignment as well as divergence. For SOC 2 compliance, we had strictly adhered only to SOC 2's Security criteria while loosely following the rest (Availability, Processing Integrity, Confidentiality, and Privacy), therefore, we discovered significant work ahead.
Key controls we needed to address included:
Web filtering enforcement using tools like Harmony Browse or DNSFilter to protect against malicious websites.
Formal breach response and notification processes that met ISO 27001's incident management requirements.
Data deletion request procedures to handle privacy rights requests systematically.
This assessment became our roadmap, identifying exactly which policies, controls, and processes required updates.
Step 2: Budgeting for Tools, Upgrades, and Team Time
ISO 27001 certification demands investment in three areas: technology, tools, and human resources.
Technology investments included:
Risk assessment and management platforms,
Incident management systems,
Governance software for ISMS management,
Endpoint security enhancements, and
Web filtering solutions.
These security tools aren't cheap. So, in our planning, we had to account for new tool acquisitions, upgrades to existing systems, and critically, our Compliance Team's time and effort in managing the transition.
Our cost-saving strategies:
Leveraged partnerships to secure favorable pricing on new tools.
Expanded usage of existing platforms rather than buying new solutions where possible.
Prioritized tools with dual benefits that served both compliance and operational efficiency.
Our clear financial forecasting ensured that we didn't overlook critical components and kept the project on track without budget surprises.
Step 3: Developing Processes and Documentation
ISO 27001 requires extensive documentation to demonstrate compliance. This includes:
Core ISMS Documentation:
Information Security Management System (ISMS) framework.
Regular risk assessment procedures.
Risk treatment plans with clear ownership.
Statement of Applicability (SoA) mapping controls to requirements.
Comprehensive asset inventory.
Mandatory controls implementation evidence.
Although our existing SOC 2 documentation provided a foundation, we still needed significant expansion to address ISO 27001's specific requirements.
New processes formalized:
Annual Management Review Meeting - Leadership engagement in reviewing ISMS effectiveness, security metrics, and strategic security objectives.
Formal Internal Audit Program - Structured approach to self-assessment before engaging external auditors, including annual internal audits to identify gaps early.
All in all, we completely revamped 25 security policies. Thankfully, our GRC platform's templates and guidance ensured that they accurately reflected our current practices and aligned with our long-term security vision.
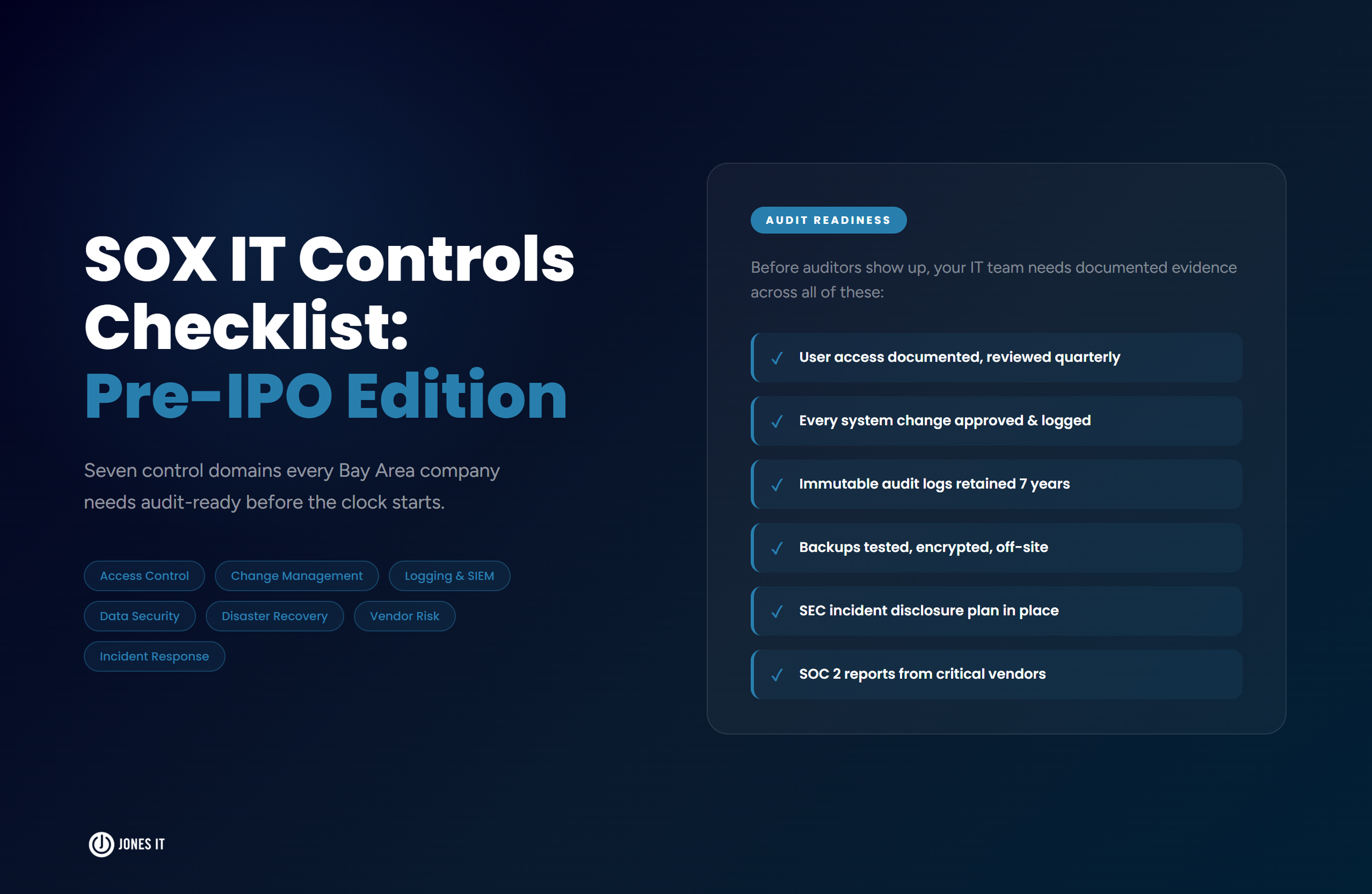
Step 4: Tackling the Audit Process
ISO 27001 certification involves more rigorous auditing than SOC 2. The process includes two distinct stages:
Stage 1 Audit: Documentation Review
Auditors evaluate your ISMS documentation, policies, and procedures to assess readiness. This stage identifies gaps before the more intensive implementation review.
Stage 2 Audit: Implementation Assessment
Auditors assess whether controls are actually implemented and operating effectively. They examine evidence, interview staff, and test control effectiveness.
Our ISO 27001 audits spanned 10 days with at least 3 hours of meetings daily to review evidence. The SOC 2 audits, on the other hand, were typically much faster and simpler.
Our audit strategy:
Conducted multiple mock audits internally before the formal assessment.
Performed pre-audit reviews to identify and rectify potential gaps.
Worked closely with Boulay, our auditor, who delivered high-quality reports and collaborative scoping.
We highly recommend Boulay for their thorough yet constructive approach to ISO 27001 audits. They don't just identify problems, but help you understand proper scoping and evidence requirements.
The Technology Stack That Made It Possible
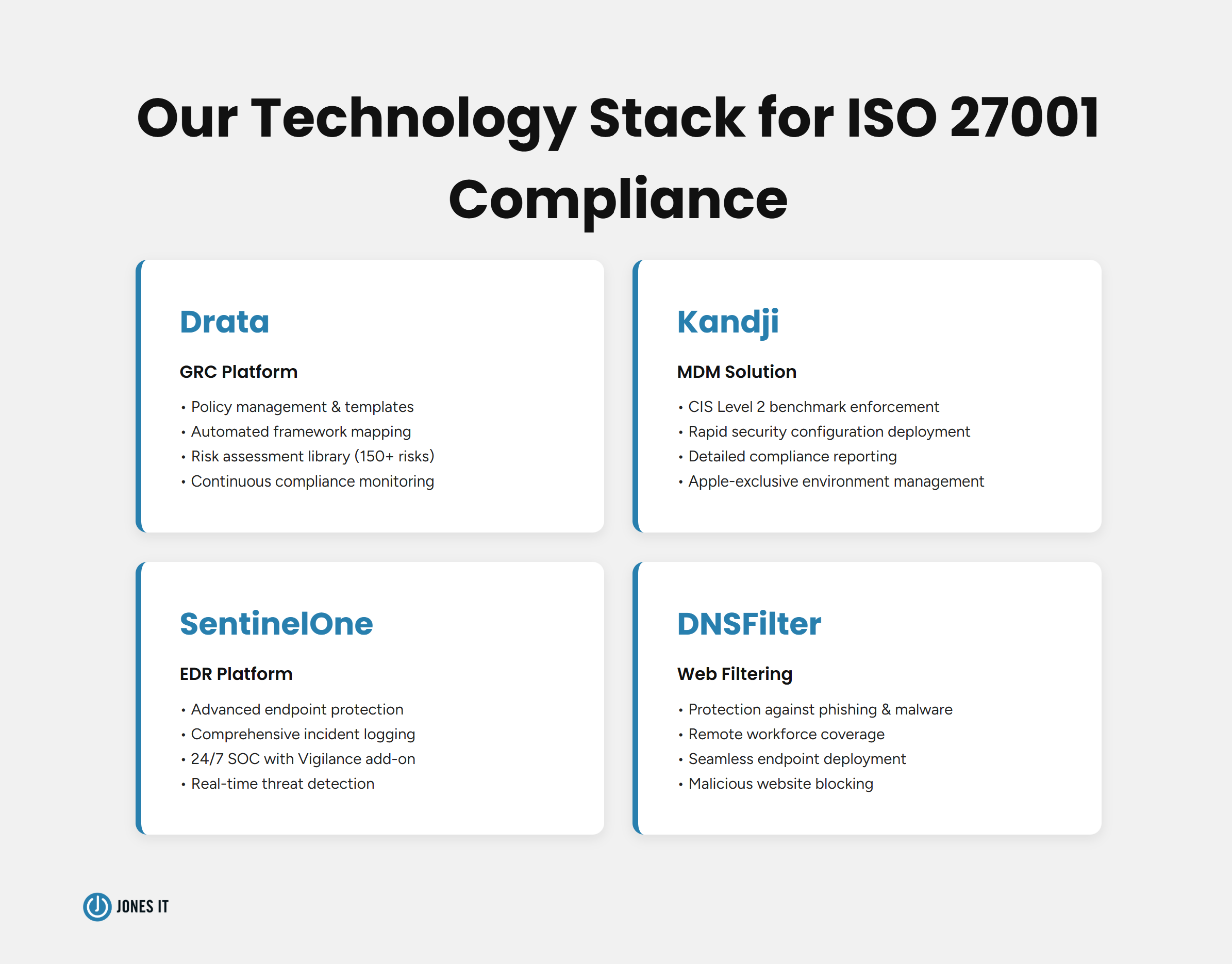
A successful ISO 27001 implementation is built on more than just robust processes; it crucially depends on having the correct technological infrastructure in place. Here's what we used and why:
Our GRC Platform Foundation
Drata played a pivotal role in developing our ISMS and overall compliance strategy. As our chosen Governance, Risk, and Compliance platform, it provided:
Policy Management Benefits:
Library of customizable templates aligned with ISO 27001 requirements,
Comprehensive guidance for policy development,
Version control and approval workflows, and
Automated policy review reminders.
We used Drata to completely revamp 25 security policies, ensuring they accurately reflected our current practices and aligned with our vision for long-term security growth.
Framework Mapping Automation:
The game-changer was Drata's ability to automatically map controls between SOC 2 and ISO 27001 frameworks. This significantly streamlined our gap assessment, reducing manual effort and ensuring we identified all missing controls.
Without this automation, the gap assessment alone could have added months to our timeline.
Transforming Our Risk Assessment Approach
Our annual risk assessment process underwent a complete transformation. Previously, we used a qualitative approach that categorized risks as "high," "medium," or "low" based on subjective judgment.
The new quantitative approach:
Using Drata's Risk Management module, we accessed a library of over 150 risks based on industry standards, including:
NIST SP 800-30,
ISO 27005, and
OCR Security Risk Assessment (SRA).
This helped us identify and address previously overlooked scenarios.
Each identified risk now receives:
Impact score - Potential business consequences if the risk materializes.
Likelihood score - Probability of occurrence based on current controls.
Severity categorization - Low, medium, high, or critical.
Clear ownership - Specific team member responsible for mitigation.
Prioritized action plans - Data-driven approach to remediation.
This shift from qualitative to quantitative risk assessment enabled us to focus first on high-severity risks with clear, measurable progress tracking.
Endpoint Compliance
Ensuring endpoint compliance was critical for ISO 27001. We enhanced our security stack with three key tools:
DNSFilter: Web Filtering for Remote Work
While our Meraki network settings provided on-premises web filtering, DNSFilter extended this protection to remote employees. It safeguards against phishing and malware attacks via suspicious websites with seamless deployment across all endpoints.
The main highlight here was that we could deploy DNSFilter to all endpoints within one hour using Kandji, our MDM platform.
Kandji: Apple-Focused MDM
Since we are an Apple-exclusive environment, Kandji served as our trusted Mobile Device Management solution. It enabled us to:
Enforce CIS Level 2 benchmarks across all Mac devices,
Deploy security configurations rapidly and consistently,
Provide auditors with detailed reports on device configurations, and
Demonstrate clear evidence of security baseline compliance.
Moreover, Kandji's clear compliance reporting proved invaluable during audits, showing exactly how our endpoints met security requirements.
SentinelOne: Advanced Endpoint Protection
SentinelOne EDR (Endpoint Detection and Response) platform provided robust malware prevention and incident response capabilities. Moreover, it served our compliance ambitions well because its comprehensive logging offered auditors clear proof of proactive security measures.
We also integrated SentinelOne's Vigilance service, adding a 24/7 Security Operations Center team. This ensured continuous monitoring of endpoints for potential intrusions, which was particularly critical during after-hours when our internal team isn't actively monitoring systems.
Together, these tools not only enhanced our compliance readiness, streamlined the audit process, but also bolstered our overall security posture beyond ISO 27001 requirements.
The Timeline: Six Months to Certification
Here's exactly how we achieved ISO 27001 certification in half the typical timeframe:
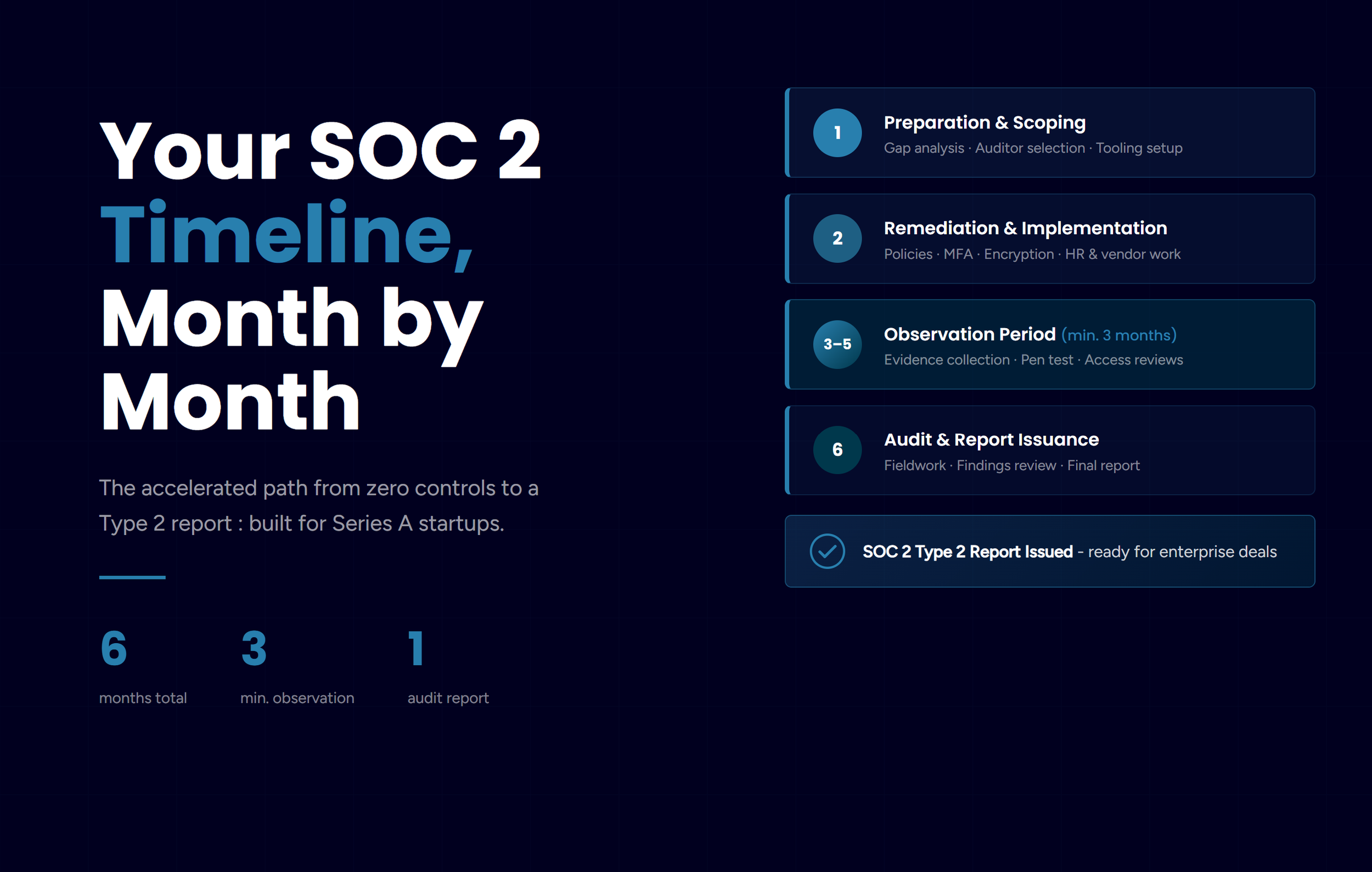
September 2023: Secured leadership approval and buy-in, ensuring alignment on resources and commitment to compliance goals.
October 2023 - January 2024: Conducted a comprehensive gap assessment and controls mapping to identify deficiencies and establish our roadmap.
February 2024: Successfully completed Stage 1 audit, identifying areas for improvement while affirming our readiness for Stage 2.
February - March 2024: Addressed feedback and implemented remediations to strengthen areas identified during Stage 1.
March 2024: Completed Stage 2 audit with flying colors, receiving validation of our compliance efforts.
April 2024: Celebrated achieving ISO 27001 certification, which was a significant milestone in our compliance journey.
Key success factors:
Building on our existing SOC 2 foundation.
Strong leadership support throughout.
Clear project planning with defined milestones.
Investment in the right tools early.
Experienced audit partner in Boulay.
Looking back, it is safe to say that without our SOC 2 foundation, this timeline would likely have extended to 12+ months.
The Real Business Impact
ISO 27001 certification delivered tangible benefits that extended far beyond checking a compliance box:
Enhanced Security Posture
The certification process drove substantial improvements across our security operations:
New capabilities implemented:
24/7 Security Operations Center - Continuous endpoint monitoring with real-time threat detection and response.
Web filtering protection - DNS filtering against phishing and malware, extending to remote employees.
Comprehensive data deletion process - Formalized secure data disposal aligned with compliance standards.
Revamped policies - 25 updated information security policies reflecting current best practices.
Improved risk assessment - Quantitative model enabling accurate prioritization and mitigation.
Leadership engagement benefit:
Collaborating closely with management throughout the process strengthened organizational alignment and fostered a deeper appreciation for ongoing compliance maintenance. Consequently, security became a shared responsibility, not just an IT concern.
Expanded Market Opportunities
ISO 27001 certification opened new doors for our organization:
Increased client confidence: Existing and prospective clients see our ISO 27001 certification as a testament to elevated security standards that far exceed SOC 2 baseline requirements.
Broader service capabilities: Our firsthand experience in achieving ISO 27001 empowered us to expand service offerings, allowing us to guide clients through their own compliance journeys with confidence and expertise.
Competitive positioning: As one of the few Managed IT Services Providers holding both ISO 27001 and SOC 2 certifications, we've gained a powerful differentiator for enterprise deals and regulated industry clients.
Process Maturity and Culture Shift
Perhaps the most valuable outcome was the maturation of our security culture. The true impact of ISO 27001 goes beyond security controls, fostering a culture of continuous improvement where:
Security considerations inform business decisions,
Risk management is proactive rather than reactive,
Everyone understands their role in protecting information, and
Processes are documented, tested, and regularly reviewed.
It is key to note that this cultural shift has a lasting impact beyond compliance cycles.
Key Lessons for Your ISO 27001 Journey
If you're considering ISO 27001 certification, here are the critical lessons from our experience:
1. Leadership Buy-In Is Non-Negotiable
Management support must extend beyond approving the project. Leadership needs to:
Actively engage with objectives and understand their importance,
Recognize the value of specific controls for your organization,
Foster a culture of accountability and collaboration, and
Provide resources and remove organizational barriers.
Without this, you'll struggle to implement controls effectively or maintain them long-term.
2. Build on Existing Foundations
If you have SOC 2 Type 2 compliance, you're already 60-70% of the way to ISO 27001. Leverage:
Existing documentation and policies,
Established audit processes,
Implemented security controls, and
Automated compliance monitoring.
Starting from scratch makes ISO 27001 a 12-18 month journey. Building on SOC 2 can reduce this to 6-9 months.
3. Invest in the Right Tools Early
The right GRC platform and security tools make an enormous difference. Look for:
Automated framework mapping capabilities,
Comprehensive risk management features,
Clear audit reporting and evidence collection, and
Integration with your existing security stack.
We chose Drata, but you should evaluate options based on your specific needs and existing infrastructure.
4. Don't Skip the Gap Assessment
Understanding exactly what you need to do is half the battle. A thorough gap assessment:
Identifies all missing controls clearly,
Helps with accurate budget and timeline planning,
Prevents surprises during the audit, and
Focuses effort on areas that truly need work.
Rush through this, and you'll pay for it later with delays and rework.
5. Choose Your Auditor Carefully
Not all ISO 27001 auditors are created equal. Look for auditors who:
Have extensive experience in your industry,
Take a collaborative rather than adversarial approach,
Provide clear guidance on evidence requirements, and
Deliver high-quality, actionable reports.
We highly recommend Boulay for their thorough yet constructive approach.
Is ISO 27001 Right for Your Organization?
ISO 27001 makes sense if:
You serve clients in regulated industries (finance, healthcare, government),
Enterprise clients require formal security certifications,
You handle sensitive customer data at scale,
You want to differentiate in a competitive market, or
You're committed to security excellence, not just compliance.
ISO 27001 may be premature if:
You're an early-stage startup without SOC 2 yet,
Your client base doesn't require formal certifications,
You lack basic security controls and processes, and
You can't dedicate resources to ongoing maintenance.
For most growing B2B companies serving enterprise clients, the question isn't "if" but "when" to pursue ISO 27001.
Next Steps: Your Path to ISO 27001
If you're ready to pursue ISO 27001 certification, here's your action plan:
1. Assess Your Current State
Document existing security controls,
Review current policies and procedures, and
Identify gaps against ISO 27001 requirements.
2. Secure Leadership Commitment
Present the business case for certification,
Get budget approval for tools and resources, and
Establish executive sponsorship.
3. Build Your Foundation
If you don't have SOC 2, consider starting there,
Implement a GRC platform for automation, and
Formalize your risk management process.
4. Engage Expertise
Select an experienced auditor early,
Consider compliance consultants if you lack internal expertise, and
Join industry groups and forums for peer learning.
5. Execute Systematically
Follow a structured roadmap like ours,
Set clear milestones and track progress, and
Conduct regular mock audits before the formal assessment.
Final Thoughts: Beyond the Certificate
Achieving ISO 27001 certification in six months was a significant accomplishment for Jones IT, but the real value lies in what we built along the way: a mature security program that protects our organization, serves our clients better, and positions us for continued growth.
The certificate isn't the destination, but validation that you've built something meaningful. The processes, tools, and culture you develop during the journey create lasting value that extends far beyond the audit cycle.
For organizations serious about security, ISO 27001 represents not just compliance, but a declaration of your commitment to protecting what matters most in today's digital business landscape.
Ready to Pursue ISO 27001 Certification?
At Jones IT, we've walked this path and understand both the challenges and opportunities. Whether you're just starting to consider ISO 27001 or you're in the middle of your compliance journey, we can help.
Our team provides expert guidance on:
Gap assessments and readiness evaluation,
Tool selection and implementation,
Policy development and documentation,
Audit preparation and evidence collection, and
Ongoing compliance maintenance.
Contact us today to discuss your compliance goals and explore how we can support your journey to ISO 27001 certification.
This post draws from Jones IT's firsthand experience achieving ISO 27001:2022 certification while maintaining SOC 2 Type 2 compliance. For a more comprehensive breakdown of our roadmap, tools and technologies, and results, download the full casen study here: