What Is SOC 2 Compliance? A Complete Guide for Startups
Updated: January 29, 2026
If you're a founder or CTO at a Series A startup, you've probably heard about SOC 2 compliance; likely from a prospect who's asking for your report, or an investor who wants to see operational maturity before they write a check.
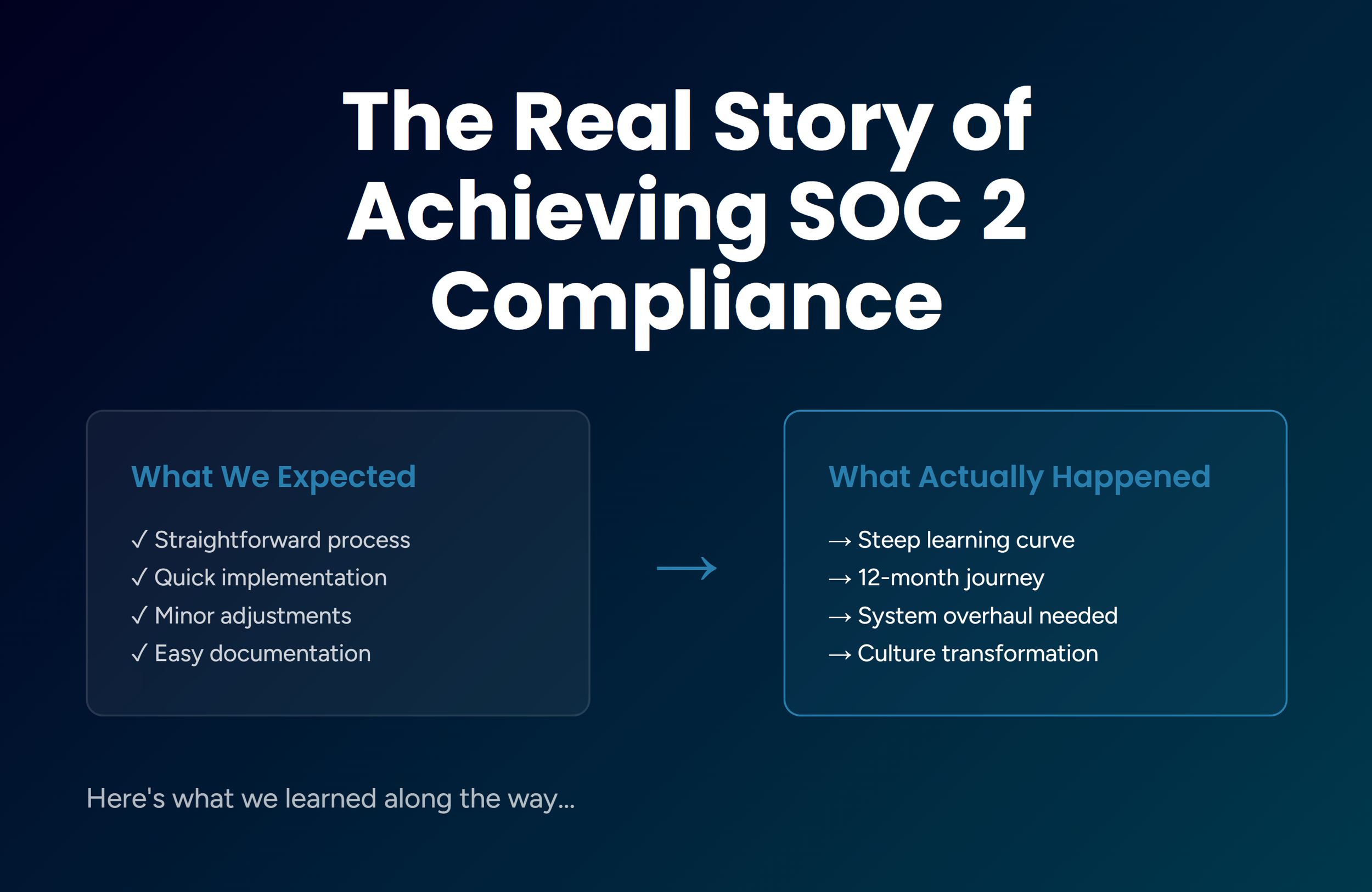
The good news? SOC 2 is completely achievable, even for early-stage companies. At Jones IT, we achieved our own SOC 2 Type 2 compliance after a 12-month journey and this guide shares what we learned and what you need to know.
What Is SOC 2?
SOC 2 (System and Organization Controls 2) is an auditing framework designed to ensure that service providers securely manage data to protect client privacy and interests. Developed by the American Institute of Certified Public Accountants (AICPA), SOC 2 is based on their Trust Services Criteria.
What makes SOC 2 different is that it's not prescriptive. Rather than telling you exactly which controls to implement, SOC 2 requires you to demonstrate that you have appropriate controls in place and that they're operating effectively. This flexibility is both a strength and a challenge.
Why SOC 2 Matters for Startups
SOC 2 compliance serves three critical purposes for early-stage companies:
1. Winning Enterprise Deals
Enterprise buyers won't sign contracts without a SOC 2 report. After we acquired our SOC 2 Type 2 report, our sales cycles shortened by 30% because prospects skipped the extensive questionnaires and trusted our third party audits and attestations.
2. Demonstrating Operational Maturity
Series A investors want to see mature operational processes and proper governance. SOC 2 shows you can scale responsibly and develop a trusted product or service.
3. Building Competitive Advantage
In crowded markets, SOC 2 sets you apart. We've directly attributed 9.25% of our revenue growth to deals we won specifically because we maintain demonstrable proof of our security posture.
SOC 2 Type 1 vs Type 2: Which Do You Need?
This is one of the most common questions we hear, and the answer has significant implications.
SOC 2 Type 1: Point-in-Time Assessment
Type 1 verifies that your controls are properly designed and implemented at a specific point in time, like a snapshot.
Timeline: 2-4 months.
Evidence Required: Documentation of policies, procedures, and system configurations.
Best For: Companies needing to demonstrate basic compliance quickly.
SOC 2 Type 2: Operating Effectiveness Over Time
Type 2 verifies that your controls are actually operating effectively over a sustained observation period (minimum 3 months, typically 6-12 months).
Timeline: 9-12 months.
Evidence Required: Continuous evidence of control operation.
Best For: Companies selling to enterprise customers (most common requirement).
Our Recommendation
Go straight for Type 2 rather than doing Type 1 first. Here's why:
Most enterprise customers require Type 2 anyway.
Type 2 demonstrates real operational maturity, not just good intentions.
The incremental effort is manageable once you've built the foundational controls.
Type 1 might make sense if you need to close a specific deal urgently, but know you'll likely need Type 2 within 12-18 months. Additionally, most enterprise customers will be satisfied with a concrete timeline and letter of engagement showing you are actively working with an auditor.
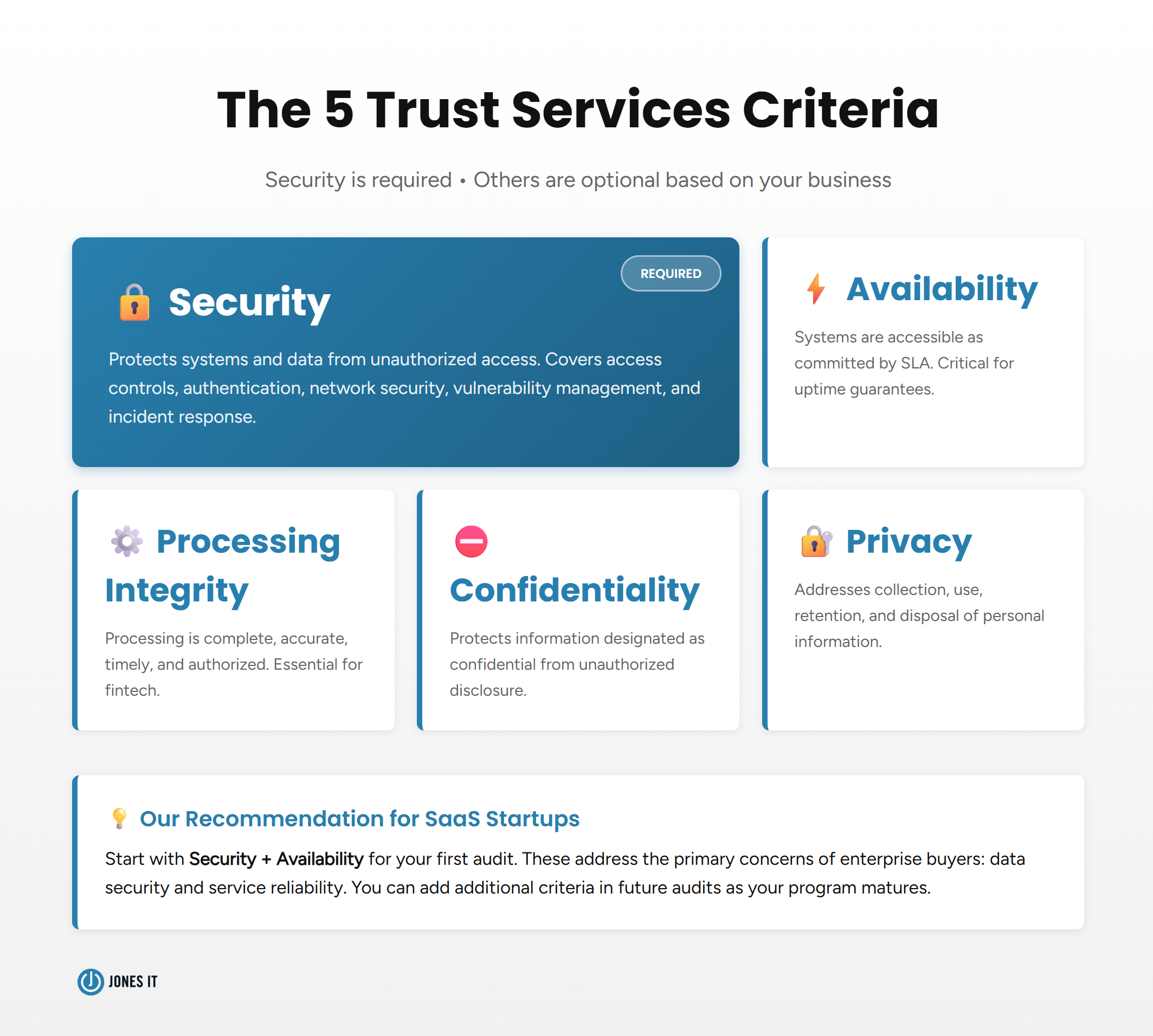
The Five Trust Services Criteria
SOC 2 is built around five Trust Services Criteria. Security is required; the others are optional based on your business needs.
1. Security (Required)
Protects systems and data from unauthorized access. Covers access controls, authentication, network security, vulnerability management, and incident response.
2. Availability (Optional)
Ensures systems are accessible as committed by contract or SLA. This is critical if you're offering uptime guarantees.
3. Confidentiality (Optional)
Protects information designated as confidential. It is important if you handle proprietary business information or trade secrets.
4. Privacy (Optional)
Addresses collection, use, retention, and disposal of personal information. This is relevant if you process personal data and privacy is a key concern, especially for GDPR compliance.
5. Processing Integrity (Optional)
Ensures data processing is complete, accurate, timely, and authorized. It is essential for companies where processing errors could cause harm, such as fintech, payroll, healthcare data, etc.
Choosing Your Criteria
For most SaaS startups, we recommend Security + Availability for your first audit. These address the primary enterprise buyer concerns: data security and service reliability. You can add additional criteria in future audits as your program matures.
Who Needs SOC 2 Compliance?
You Definitely Need SOC 2 If:
You're selling to enterprise customers who ask for your report.
You store, process, or transmit sensitive customer data.
You're raising Series A+ funding and investors are asking about compliance.
You're losing deals because of vendor security assessments.
You're in regulated industries ( like fintech, healthcare) where compliance is table stakes.
Timing Matters:
Don't wait until a prospect asks to start pursuing compliance. The Type 2 observation period (6-12 months) means you'll lose deals while working on compliance. Start at least 12-18 months before you expect enterprise sales.
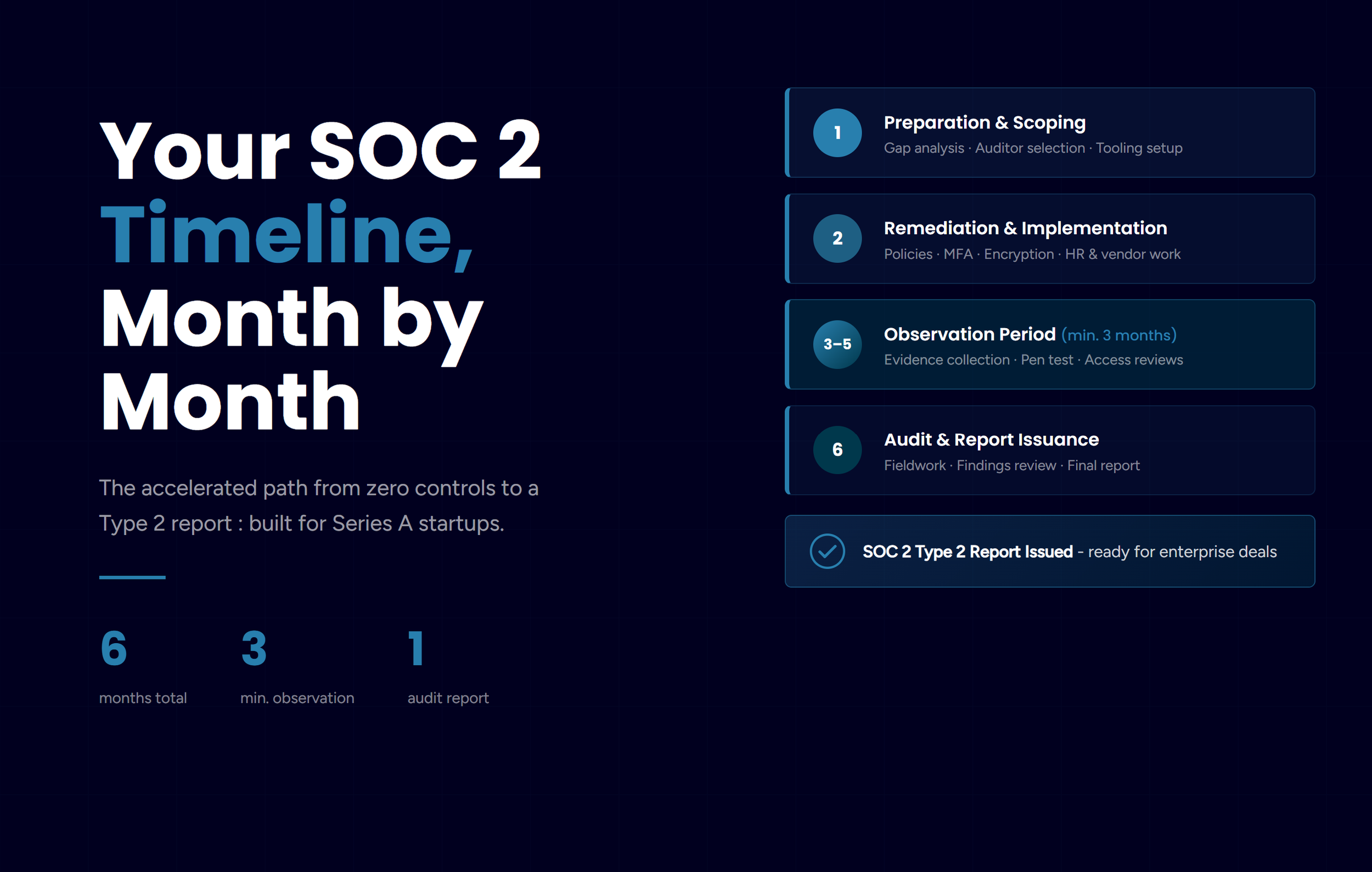
Timeline and Cost: What to Expect
How Long Does SOC 2 Take?
Typical SOC 2 Type 2 Timeline:
Months 1-2: Readiness assessment and gap analysis.
Months 3-6: Implementation of controls and tools.
Months 7-9: Observation period (3 month minimum is a good starting point for year 1).
Months 10-11: Audit period preparation and execution.
Total: 10-12 months from start to report-in-hand.
Our journey took about 12 months. Could we have done it faster? Maybe by 2-3 months, but rushing creates unnecessary stress and likely leads to gaps.
What Does SOC 2 Actually Cost?
Here's the realistic budget breakdown:
Direct Costs:
Auditor Fees: $10,000-$20,000
Compliance Tools: $12,000-$40,000/year (Vanta, Drata, etc.)
Security Tools: $10,000-$100,000+ (IAM, EDR, MDM, SIEM, etc.)
Consulting (Optional, but recommended): $20,000-$100,000+
Indirect Costs:
Company Operation Time: Time spent on policies, documentation, evidence gathering, implementing security controls across departments
Opportunity Cost: Employee time spent on compliance tasks like security training and policy acknowledgements is time not spent building product
Total Investment Range:
Small Startup (10-50 employees): $75,000-$200,000
Mid-Size (50-200 employees): $150,000-$400,000
Is It Worth It?
For us, absolutely. Beyond compliance, we saw:
30% shorter sales cycles.
75% faster incident response SLA (2 hours → 1 hour).
9.25% revenue growth from compliance-enabled deals.
SOC 2 made us operationally stronger and more competitive.
Read our complete SOC 2 compliance journey including obstacles and lessons learned → The Real Story of Achieving SOC 2: Our 12-Month Journey. [Coming soon]
How To Get Started: Your SOC 2 Roadmap
Step 1: Conduct a Readiness Assessment
Before diving into implementation, understand your current state. A readiness assessment identifies gaps between where you are and what SOC 2 requires.
Recommendations:
Use a compliance automation platform (Vanta, Drata).
Work with an experienced MSP that specializes in security and compliance.
Output: Gap analysis showing what you have, what you need, and prioritized remediation plan.
Step 2: Implement Core Controls
Focus on foundational elements:
Identity and Access Management
Deploy centralized IAM (Okta, Entra, Google Workspace).
Implement MFA across all systems.
Establish RBAC and access workflows.
Endpoint Security
Deploy EDR on all devices (SentinelOne, CrowdStrike).
Implement MDM for company devices (Iru, Intune).
Enforce full-disk encryption.
Documentation
Information Security Policy.
Access Control Policy.
Change Management Policy.
Vendor Risk Management Policy.
Reality Check: This is the heavy lifting phase. We spent weeks mapping roles and permissions, but it paid off afterward as access management time dropped 70%.
Step 3: Begin Your Observation Period
Once controls are in place, you enter the observation period where you prove controls operate effectively over time.
Critical Success Factors:
Automate evidence collection - Manual collection will crush you.
Build sustainable habits - Weekly reviews, monthly audits, quarterly policy reviews.
Make compliance operational - Build it into your rhythm, not a separate project.
Our observation period taught us more about operational discipline than any business book could.
Step 4: Complete Your Audit
As you approach the end of your observation period:
Select Your Auditor (do this early):
Look for experience in your industry and company size.
Check AICPA membership.
Assess peer review status.
Get references from your peers.
Audit Process:
System description and control documentation review.
Evidence testing from throughout the observation period.
Personnel interviews.
System configuration examination.
Findings issuance (if any).
Draft report review.
Final SOC 2 report.
Timeline: 2-4 weeks of active fieldwork.
Step 5: Maintain Compliance
SOC 2 Type 2 reports are valid for 12 months. You need to plan for annual audits to maintain certification.
Ongoing Requirements:
Continue operating all controls as documented.
Collect evidence continuously.
Update policies as business evolves.
Conduct quarterly internal audits.
Train new employees.
Common Obstacles and How to Overcome Them
Based on our experience, here are the common SOC 2 challenges that trip up most startups:
1. Lack of Compliance Expertise
The Problem: Security expertise ≠ compliance expertise.
The Solution: Partner with specialists, use compliance platforms, or work with an experienced MSP, like Jones IT.
2. Complex IT Environment
The Problem: Years of organic growth creates disconnected systems.
The Solution: Audit and consolidate before pursuing compliance, not during.
3. Undocumented Processes
The Problem: Strong practices but poor documentation.
The Solution: Start documenting now if planning SOC 2 in 12-18 months.
4. Sustaining Consistency
The Problem: Maintaining controls for months requires discipline.
The Solution: Aggressive automation + cultural change + operational rhythms.
Read the complete story of obstacles we overcame → download the full case study:
Essential Tools for SOC 2
GRC (Compliance Automation): Drata, Vanta - Essential, we don’t recommend starting your journey without one of these tools to start.
IAM: Okta, Entra, or Google Workspace.
EDR: SentinelOne or CrowdStrike
SIEM: Datadog, Splunk, or LogRhythm.
MDM: Iru, Intune.
Total Tool Investment: $30,000-$100,000/year depending on size.
Frequently Asked Questions About SOC 2 Compliance
How much does SOC 2 cost?
$75K-$200K for small startups (10-50 employees) including auditor, tools, and internal time. The biggest cost is often internal effort.
How long does SOC 2 take?
SOC 2 Type 2 typically takes 9-12 months. Type 1 can be done in 3-6 months but most enterprise customers require Type 2.
Can I do SOC 2 without a compliance tool?
Technically yes, but we strongly recommend against it. Manual evidence collection is incredibly time-consuming and error-prone.
Should I get Type 1 or Type 2?
Unless you have a specific short-term need for Type 1, go straight for Type 2. Most sophisticated buyers require it anyway.
Can my MSP help with SOC 2?
Yes, if they have compliance expertise. At Jones IT, we help clients with everything from readiness assessment to ongoing maintenance. Not all MSPs have this capability, so ask about their specific SOC 2 experience. See our Trust Center for evidence of our expertise.
Next Steps
If You're 12+ Months Away:
Start building foundation now (IAM, endpoint security, documentation).
Conduct informal gap analysis.
Plan your budget.
If You Need SOC 2 in 6-12 Months:
Start immediately with formal readiness assessment.
Begin remediation and tool deployment.
Select auditor and compliance platform.
Consider expert help to accelerate.
If You Need SOC 2 in 0-6 Months:
Be realistic; Type 2 likely isn't achievable
Consider Type 1 as a bridge.
Get expert help (consultant or experienced MSP).
Focus on critical path items.
How Jones IT Can Help
We've been through the SOC 2 journey ourselves and now help startups navigate the same path. Our services include:
Readiness Assessment: Gap analysis and remediation roadmap.
Implementation Support: Tool deployment, configuration, policy development.
Ongoing Maintenance: Continuous monitoring and evidence organization.
Fractional Compliance: Part-time expertise without full-time hire.
We don't just tell you what to do; we do it with you.