SOC 2 Compliance Timeline: Month-by-Month Roadmap for Series A Startups
If you've just closed your Series A and someone in your last investor meeting mentioned SOC 2, you're probably doing two things right now: nodding like you've got it handled, and quietly panicking about where to start.
We’ve been in a similar situation. When we pursued SOC 2 Type 2 at Jones IT, we learned that the hardest part wasn't the audit itself, but understanding the actual sequence of events and how long each phase takes. Every resource we found gave vague timelines like "6 to 12 months." That's technically accurate, and almost entirely useless when you're trying to tell a prospect when you'll have your report.
This post is the guide we wish we'd had. A real, month-by-month breakdown of what SOC 2 compliance actually looks like, especially for a Series A startup, with honest estimates, common pitfalls, and the decisions you need to make before you even start.
SOC 2 Type 1 vs Type 2: The First Decision You Have to Make
Before you can plan a timeline, you need to settle one question: Type 1 or Type 2? We covered this in depth in our SOC 2 Type 1 vs Type 2 blog post. Here's the short version:
Type 1 validates that your security controls are properly designed at a single point in time. Type 2 validates that those controls actually worked consistently over a sustained period, which is typically 3 to 12 months. Most enterprise buyers require Type 2.
For a Series A startup actively selling into enterprise accounts, our recommendation is almost always to go straight for Type 2. Starting with Type 1 and then pursuing Type 2 means doing much of the same work twice, and it adds 6 to 12 months to your timeline. The only time Type 1 makes sense as a first step is if you have an immediate deal that requires a compliance signal in the next 60 days and the customer has explicitly confirmed they'll accept it.
Assuming you're going straight for Type 2, which is the right call for most of you reading this, here's what the journey looks like.
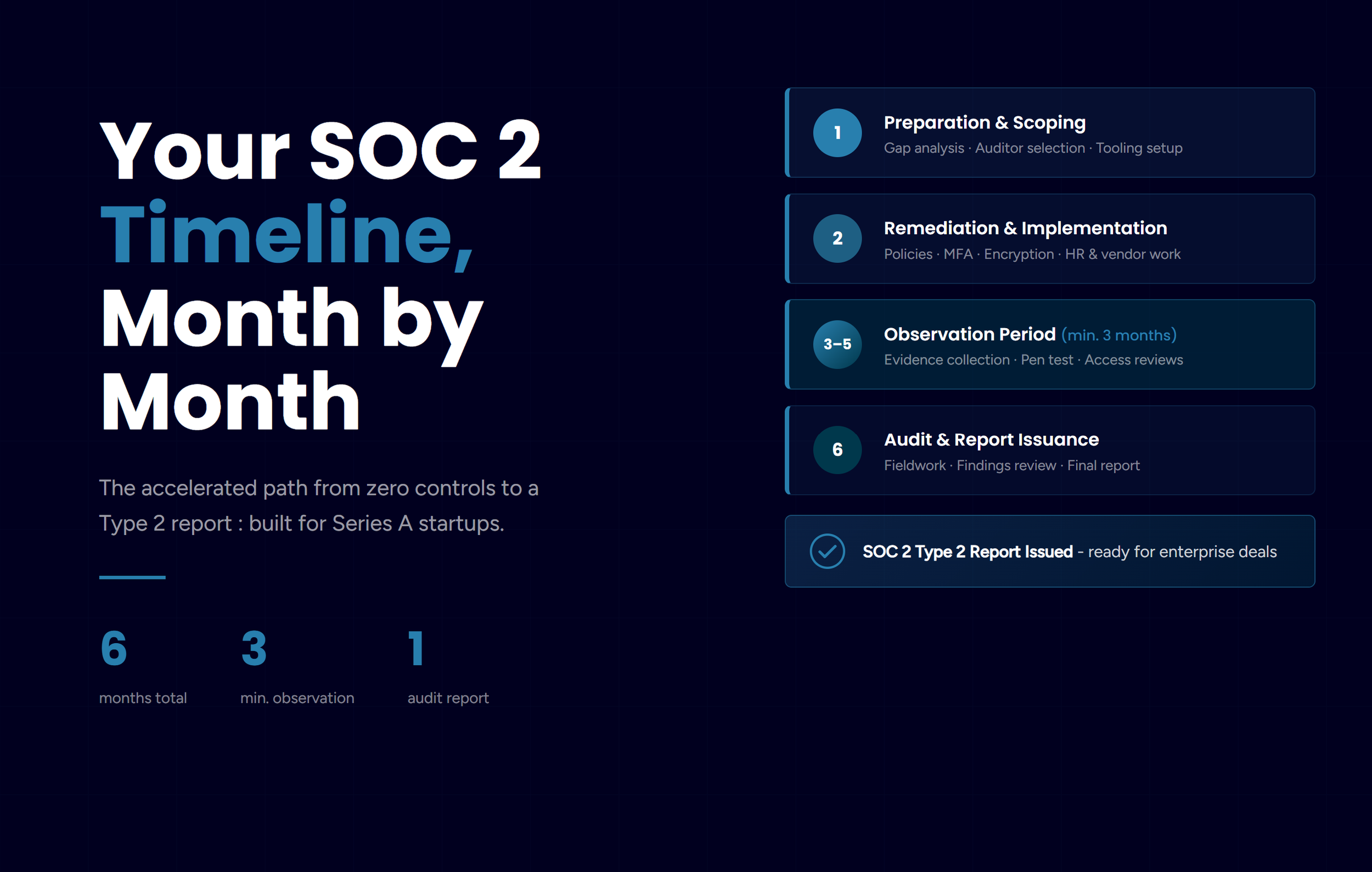
The Accelerated SOC 2 Compliance Path: 6 Months Total
The standard timeline for SOC 2 Type 2 is 6 to 12 months. The accelerated path, made possible by modern compliance automation tools, compresses this to around 4 to 6 months. The observation period, the phase where you demonstrate continuous operation of controls, has a minimum of 3 months and can't be shortened regardless of how automated your tooling is.
Here's how the accelerated timeline breaks down.
Month 1: Preparation and Scoping
This is the phase most startups skip or rush, which causes the most pain later. Before you implement a single control or sign a contract with an auditor, you need to define exactly what you're getting audited on.
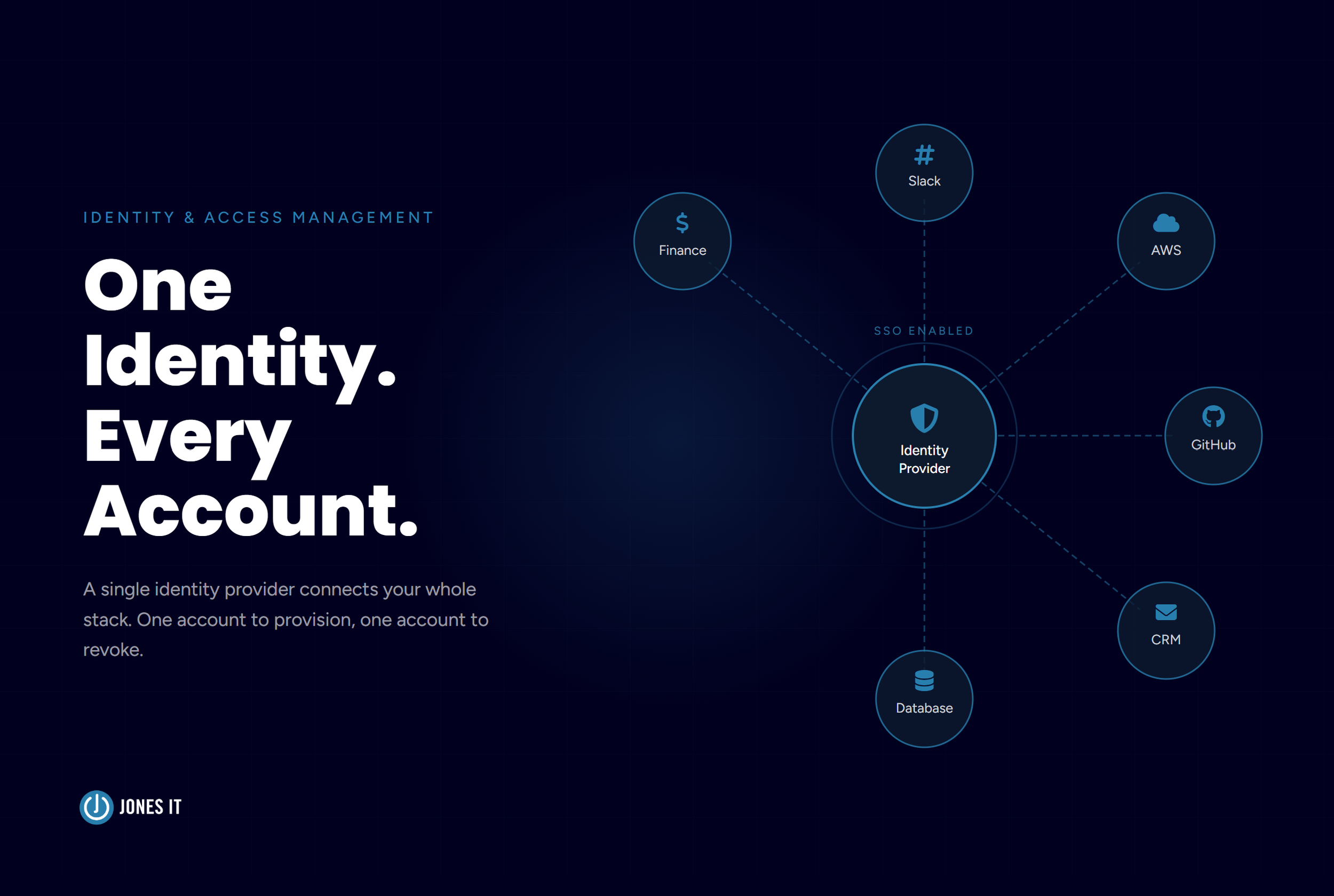
Defining your scope means identifying which systems, environments, and processes will be covered by the audit. At minimum, this includes your production environment (AWS, GCP, or Azure), your code repositories, and the key personnel who have access to sensitive systems. The goal is to draw a clear boundary: inside the scope gets audited, outside doesn't.
Running a gap analysis means comparing your current state against the SOC 2 controls you'll need to satisfy. You're looking for missing policies (do you have a formal Incident Response plan?), technical gaps (is MFA enforced everywhere?), and process holes (are you doing access reviews?). If you skip this step and go straight into implementation, you'll discover gaps during the audit, which is a very expensive place to find them.
Selecting your auditor needs to happen now, not in month 5. Good auditors who work with startups have full calendars. Get them engaged early so they can review your control design before you start the observation period. Their input during scoping can save you from implementing controls that won't satisfy their testing requirements.
Choosing your compliance platform is the decision that determines how painful the next six months will be. Tools like Vanta and Drata integrate with your cloud infrastructure, identity systems, code repos, and security tools to continuously collect evidence automatically. Without automation, you're manually taking screenshots of log outputs every week and organizing them into spreadsheets, which consumes hundreds of hours and introduces significant error risk. Budget $5,000 to $30,000 per year for tooling, and treat it as mandatory rather than optional.
One more thing to decide in Month 1 is which Trust Services Criteria you'll pursue. Security (the Common Criteria) is mandatory. Availability is worth adding if you have uptime SLAs with customers. Confidentiality and Privacy are optional: add them only if your customers are actively asking for them. Every additional criterion adds cost and complexity, so start with Security and Availability and expand from there.
Month 2: Remediation and Implementation
With your gaps identified and your auditor selected, Month 2 is about closing every identified gap before you start the observation period. This is important: you cannot fix the past during the observation period. If a control wasn't operating in January, the auditor will see that in January's evidence. The time to get everything right is now.
Policy creation is usually the first bottleneck startups hit. SOC 2 requires formal, approved policies covering information security, access control, change management, vendor management, incident response, and a handful of others. If you don't have these written down, your compliance platform will provide templates; use them. The goal isn't literary perfection; it's demonstrable, approved documentation that your team actually follows.
Technical control implementation covers the concrete security work: enforcing MFA across all systems without exception, enabling audit logging on production infrastructure, encrypting databases at rest, implementing endpoint detection on all company devices, and ensuring automated backups are running and being tested. These aren't bureaucratic checkbox items, but fundamental security hygiene that your auditor will test rigorously.
HR and vendor work often gets deprioritized and then causes last-minute scrambles. Background checks need to be completed for all employees with access to in-scope systems. Data Processing Agreements need to be signed with all sub-processors (any third-party vendor that touches customer data). And you need a process for reviewing the SOC 2 reports of your own critical vendors, because auditors will ask whether you've evaluated your supply chain.
By the end of Month 2, you should be able to confirm with your auditor that your controls are designed effectively. Don't start the observation period until you have that confirmation. Starting the clock before your controls are fully implemented means the auditor will find exceptions during testing, which results in a "qualified" opinion, which is the compliance equivalent of a failing grade.
Months 3-5: The Observation Period
This is the phase that defines SOC 2 Type 2. And it's the one that's hardest to explain to founders who've never been through it.
The observation period exists because any company can implement good controls for a week. SOC 2 Type 2 is designed to prove you can maintain those controls consistently over time. During this period, auditors aren't testing you directly, but they will later review everything that happened. Every access review, every security training, every backup, every incident response, every vendor review: all of it becomes evidence that either supports or undermines your report.
The cardinal rule of the observation period is don't make significant changes to your control environment. If you restructure your access management system in month 4, you create a break in evidence continuity that your auditor has to explain. Unless there's a critical security reason to change something, freeze your controls and operate them as designed.
Operational rhythms are everything during this phase. You need a weekly check of your compliance platform dashboard to verify all integrations are still connected and evidence is still being collected. You need quarterly access reviews, meaning you actually pull the list of who has access to what and certify that every account is still appropriate. New hires need to complete security awareness training immediately upon joining, not two weeks later. And you need to run, as well as document, at least one tabletop incident response exercise.
The penetration test needs to be scheduled and completed during this period. Most auditors require an external penetration test for the Security criteria. These tests take 2 to 4 weeks from engagement to report, and good pen test firms book up fast. You should already have engaged a pen test firm by the start of Month 3.
The most common mistake we see during the observation period is treating it like a waiting room. Teams implement their controls, start the clock, and then go back to regular work until someone realizes three months later that evidence collection stopped running because an integration broke, or that the quarterly access review never actually happened. The observation period requires active oversight, so you need to assign someone to own it and make compliance a standing agenda item in your weekly team meetings.
Month 6: The Audit and Report Issuance
If your first five months went well, Month 6 is genuinely anticlimactic. The auditor reviews your evidence, tests a sample of controls, and interviews key personnel (typically the CTO or Head of Engineering, and whoever owns your security program).
Fieldwork typically takes 2 to 4 weeks. During this time, your auditor will request specific evidence samples, like particular logs, access review records, training completion records, and so on. Responsiveness here matters. Slow responses to auditor requests extend the timeline. Assign one person to be the primary auditor contact and prioritize their requests.
Expect findings. Even well-prepared companies get findings. The question isn't whether auditors will find anything, but how significant the findings are and whether they rise to the level of affecting your opinion. Minor exceptions that were addressed before the audit ends are often documented but don't necessarily compromise the report. Work with your auditor openly. They're not adversaries, and their job is to produce an accurate report, not to penalize you.
Report issuance follows a draft review period where you can provide management responses to any findings. After you've reviewed the draft and confirmed it accurately reflects your environment, the auditor issues the final SOC 2 Type 2 report.
What This Costs: Planning SOC 2 Compliance Budget
Founders often underestimate the full cost of SOC 2 because they focus on the audit fee and ignore everything else. Here's a realistic budget breakdown for a Series A startup on the accelerated path:
The audit fee itself typically runs $10,000 to $20,000 with a startup-friendly CPA firm. Compliance automation tooling (Vanta, Drata, or similar) costs $12,000 to $40,000 per year, and this is money well spent as it replaces hundreds of hours of manual work. An external penetration test runs $5,000 to $15,000. And then there's internal labor: with automation, expect 100 to 200 hours of total team time across the project. Without it, that number is closer to 300 to 600 hours.
All in, budget $30,000 to $75,000 for the first year on the automated path. If you're planning a Series A raise, model this in. Sophisticated investors understand that SOC 2 is a cost of enterprise sales, and they've seen companies that tried to shortcut it.
The Three Most Expensive SOC 2 Timeline Mistakes We See
Starting the clock too early
Founders get eager and start the observation period before controls are fully implemented. This is one of the most costly mistakes you can make, because if controls weren't enforced on day one of your observation period, the auditor will find evidence of that, and it affects your report. Complete your remediation, confirm with your auditor that controls are designed effectively, and only then start the clock.
Letting evidence collection lapse
Your compliance platform integrations can break: an API credential expires, an integration update fails, or a monitoring agent stops running. If nobody checks the dashboard and three months of evidence go uncollected, you may need to restart your observation period. Weekly dashboard reviews are not optional.
Scope creep
Every additional Trust Services Criteria you add: Processing Integrity, Privacy, or Confidentiality, adds substantial cost and complexity to the audit. Add criteria because your customers are asking for them, not because they seem like a good idea. You can always add criteria in your next annual audit cycle once you've validated the requirement.
After the SOC 2 Report: What Happens Next
A lot of founders treat the SOC 2 report as a finish line. It isn't. It's the beginning of an annual compliance cycle.
Your Type 2 report covers a specific period, say, March through August. When you're handing that report to a prospect in December, they may ask about the 4-month gap between your report period and today. Enterprise security teams often require a bridge letter: a written attestation from management confirming that controls continue to operate effectively after the report period.
More importantly, the observation period for your next annual audit begins the day after your current observation period ends. If you stop doing quarterly access reviews the week your report is issued, you'll have gaps in evidence when your renewal audit comes around 12 months later.
Therefore, plan for SOC 2 to be an ongoing operational function, not a one-time project. The compliance automation tools you bought to get through the first audit will continue earning their cost in the renewal cycle.
Quick-Reference SOC 2 Compliance Timeline
For a startup starting from scratch today, here’s a quick summary:
Month 1: Scoping, gap analysis, auditor selection, compliance platform implementation.
Month 2: Policy creation, technical control implementation, HR and vendor work, readiness confirmation with the auditor.
Months 3-5: Observation period with continuous evidence collection, penetration test, and operational rituals.
Month 6: Auditor fieldwork, evidence review, report issuance.
Total: approximately 6 months to your first SOC 2 Type 2 report on the accelerated path.
How Jones IT Can Help In Your SOC 2 Compliance Journey
We went through the SOC 2 Type 2 compliance journey ourselves and built our own compliance program from scratch. We're SOC 2 Type 2 compliant, and we've helped dozens of startups navigate the same path, many of them on tight timelines driven by in-flight enterprise deals.
Whether you're starting your readiness assessment, selecting an auditor, or trying to figure out whether your existing controls will hold up to scrutiny, we can help you move faster and avoid the mistakes that derail compliance programs.
Schedule a consultation with our team to talk through your specific situation. We'll help you understand exactly where you are, what needs to happen, and how to get your report done on a timeline that serves your business.
Frequently Asked Questions About SOC 2 Roadmap
Q: Can we really complete SOC 2 Type 2 in 6 months?
A: Yes, with automation and proper preparation. The minimum observation period is 3 months, so the theoretical floor is around 4 to 5 months (plus audit time). Most startups on the accelerated path land at 5 to 6 months total. The 12-month timeline you'll sometimes see is for companies with significant remediation work or manual evidence collection processes.
Q: What's the minimum observation period?
A: Three months is the minimum most auditors will accept. Six months is more common and provides stronger assurance for sophisticated buyers. Twelve months produces the most thorough report but delays your timeline significantly. For early-stage companies on tight timelines, three to six months is the standard choice.
Q: Do we need to do SOC 2 Type 1 first?
A: No. Type 1 is not a prerequisite for Type 2. You can go straight to Type 2, and for most Series A companies, that's the right choice. Type 1 only makes sense if you have an immediate need for a compliance signal and a customer who has explicitly confirmed they'll accept it.
Q: How do we keep compliant after the first audit?
A: The renewal audit observation period begins immediately after your first one ends. Maintain your quarterly access reviews, keep your compliance platform running and connected, train new hires on security immediately upon onboarding, and treat compliance as an ongoing operational function rather than a project with an end date. Companies that let compliance lapse between audits spend significantly more time and money on renewals than those that maintain continuous hygiene.
Jones IT is a San Francisco-based Managed IT Services provider with over two decades of experience helping startups and scale-ups build secure, compliant, and efficient technology operations. We are SOC 2 Type 2 compliant and help clients navigate their own compliance journeys.