IT SOX Compliance: What Finance and Tech Companies Need to Know
Imagine that you are a fintech founder in SoMa, and it’s three weeks before your company's IPO. The CFO has been running through checklists, investment bankers are looped in, and your finance team is proud of the work they have put in. Then your external auditors flag something unexpected. He noticed that your IT controls over financial systems have never been formally documented, tested, or validated. Your cloud infrastructure has access permissions that have not been reviewed in 18 months. Your financial systems log activity, but those logs are not being retained in a format auditors can accept as evidence.
As a consequence, remediation costs climb, and the IPO timeline slips. And suddenly, everyone in the room is asking why IT was not pulled into the compliance conversation from the beginning.
This scenario plays out more often than most companies realize.
What Is SOX Compliance
The Sarbanes-Oxley Act (SOX) was signed into law in 2002 following the Enron and WorldCom scandals that shook public confidence in US financial markets and erased an estimated $6 trillion in household wealth. It was designed to prevent corporate fraud and restore public trust in financial reporting. But it was written before the modern cloud stack existed, before CI/CD (continuous integration and continuous delivery) pipelines became standard, and before SaaS tools became the backbone of financial operations. Tech and finance companies today face compliance challenges that SOX's original architects could not have anticipated, and the IT department is at the center of all of them.
We work with finance and technology companies navigating exactly these kinds of challenges, and the pattern we see most often is that organizations treat SOX as a finance problem until an auditor tells them otherwise. This guide breaks down what IT SOX compliance actually requires, what controls your program cannot skip, and how leading organizations are modernizing their approach.
What IT SOX Compliance Actually Requires
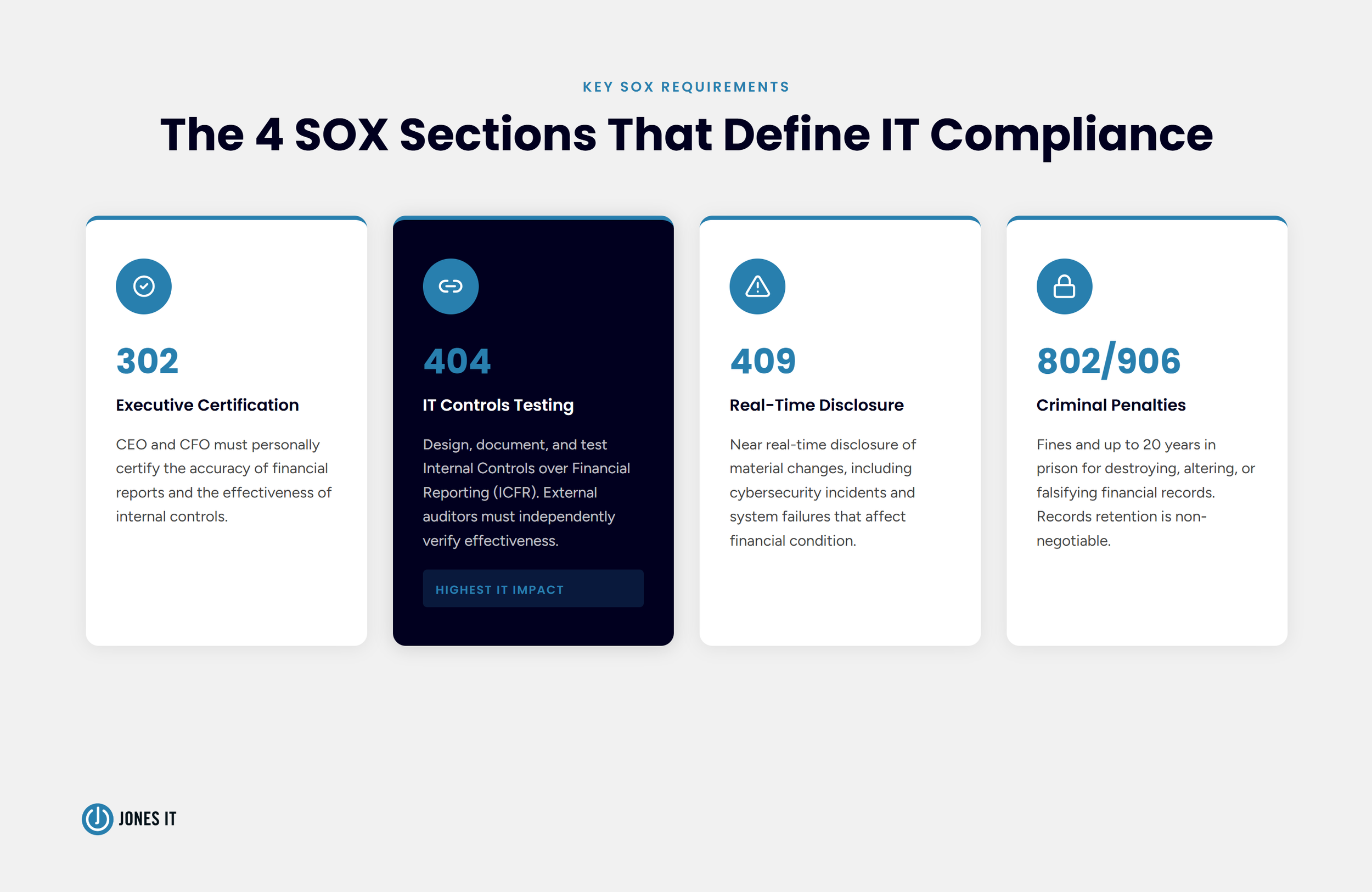
SOX contains 11 titles, but four sections govern the IT and financial control frameworks that organizations must implement. Understanding what each one demands of your IT environment is the starting point for any compliance program.
Section 302 requires the CEO and CFO to personally certify the accuracy of financial reports and the effectiveness of internal controls. That certification carries real legal weight, and it depends entirely on whether your IT systems are producing reliable, verifiable data.
Section 404 is where IT teams feel the most pressure. It mandates that organizations design, document, and test their Internal Controls over Financial Reporting (ICFR). Management must assess those controls, and external auditors must independently verify that they are fully effective. If your ERP system, data warehouse, billing platform, or revenue recognition tool touches financial data, Section 404 applies to it.
Section 409 requires near real-time disclosure of material changes to a company's financial condition, including cybersecurity incidents and system failures. A breach that exposes financial data is not just a security problem. It is a disclosure obligation with a tight clock.
Sections 802 and 906 establish criminal penalties for destroying, altering, or falsifying financial records. Fines are steep, and prison sentences can reach 20 years. These sections explain why audit trail integrity and records retention are non-negotiable.
Why Tech and Finance Companies Face Unique Compliance Challenges
SOX was designed to regulate the large public companies of the early 2000s: enterprises with relatively stable IT environments and centralized financial systems. Modern tech and finance companies operate in a fundamentally different way, and the gap between the regulation's original assumptions and today's infrastructure is where most compliance problems start.
Rapid Scaling and Cloud Complexity
A fast-growing SaaS company might deploy code multiple times per day using CI/CD pipelines, spin up new cloud environments on demand, and grant access to contractors who rotate in and out of projects on short cycles. Every one of those changes is a potential control gap. Tracking who has access to financial systems and documenting that those permissions follow the principle of least privilege becomes genuinely difficult when the environment changes faster than compliance teams can review it. Decentralized SaaS stacks make this harder still, because financial data now lives across a dozen tools instead of one.
Siloed Data and Manual Processes
Financial data flows through ERPs, billing platforms, revenue recognition tools, and data warehouses, and organizations often rely on spreadsheets to reconcile it across those systems. Spreadsheets create version control problems, introduce transcription errors, and produce gaps that auditors notice. The more manual the process, the more audit evidence is required to demonstrate that controls are working as designed, and the higher the risk that something does not hold up under scrutiny.
The Cost of Getting It Wrong
SOX compliance is resource-intensive even when organizations are doing it well. On average, companies spend over $1 million annually on compliance, dedicating up to 10,000 hours to control testing, audits, and remediation. That figure rises sharply when controls are poorly designed or when problems surface late in the audit cycle. For companies heading toward an IPO, a material weakness finding can delay or derail the process entirely, at precisely the moment when timing matters most.
The SOX Compliance IT Controls Your Program Cannot Skip
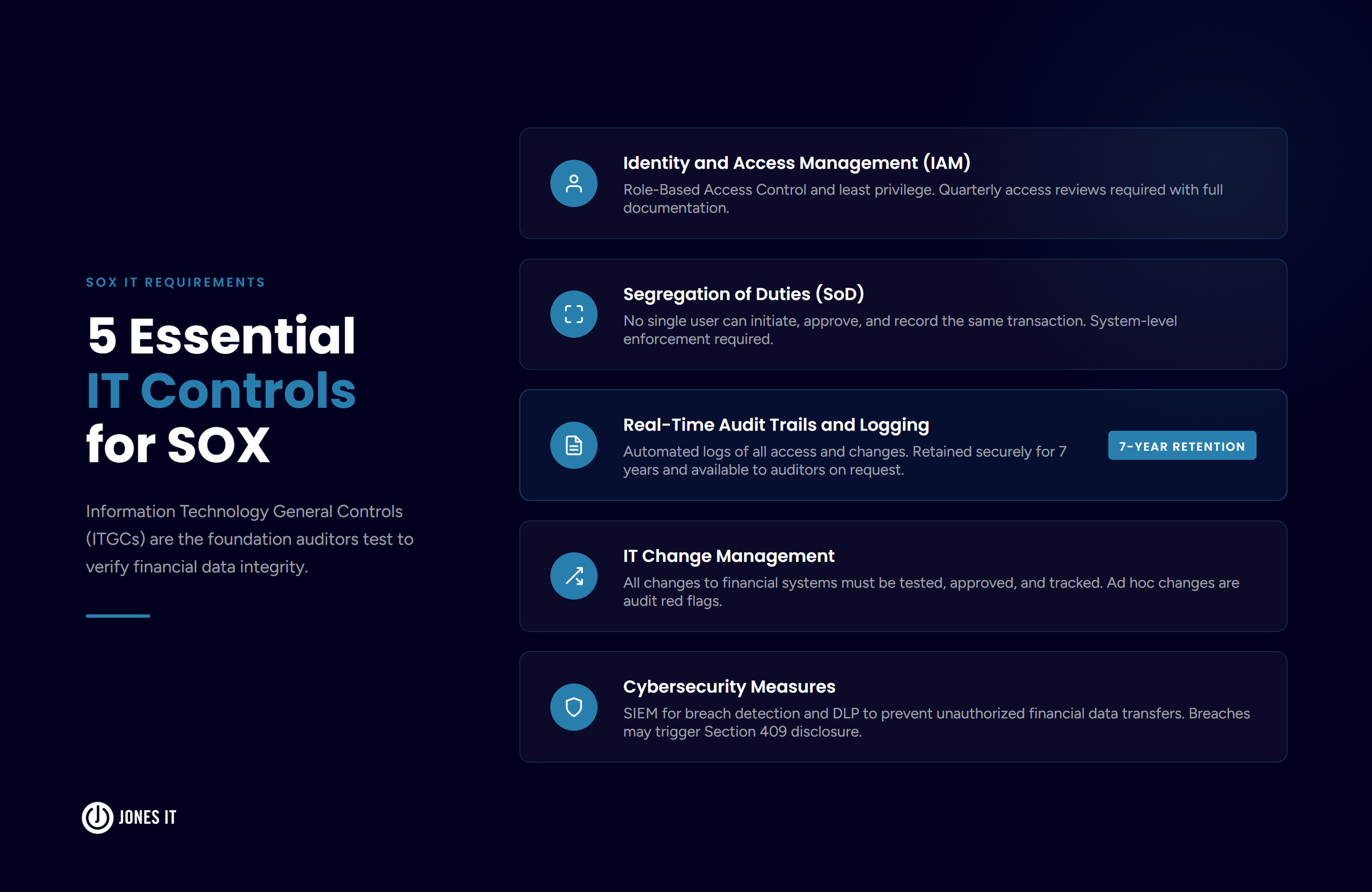
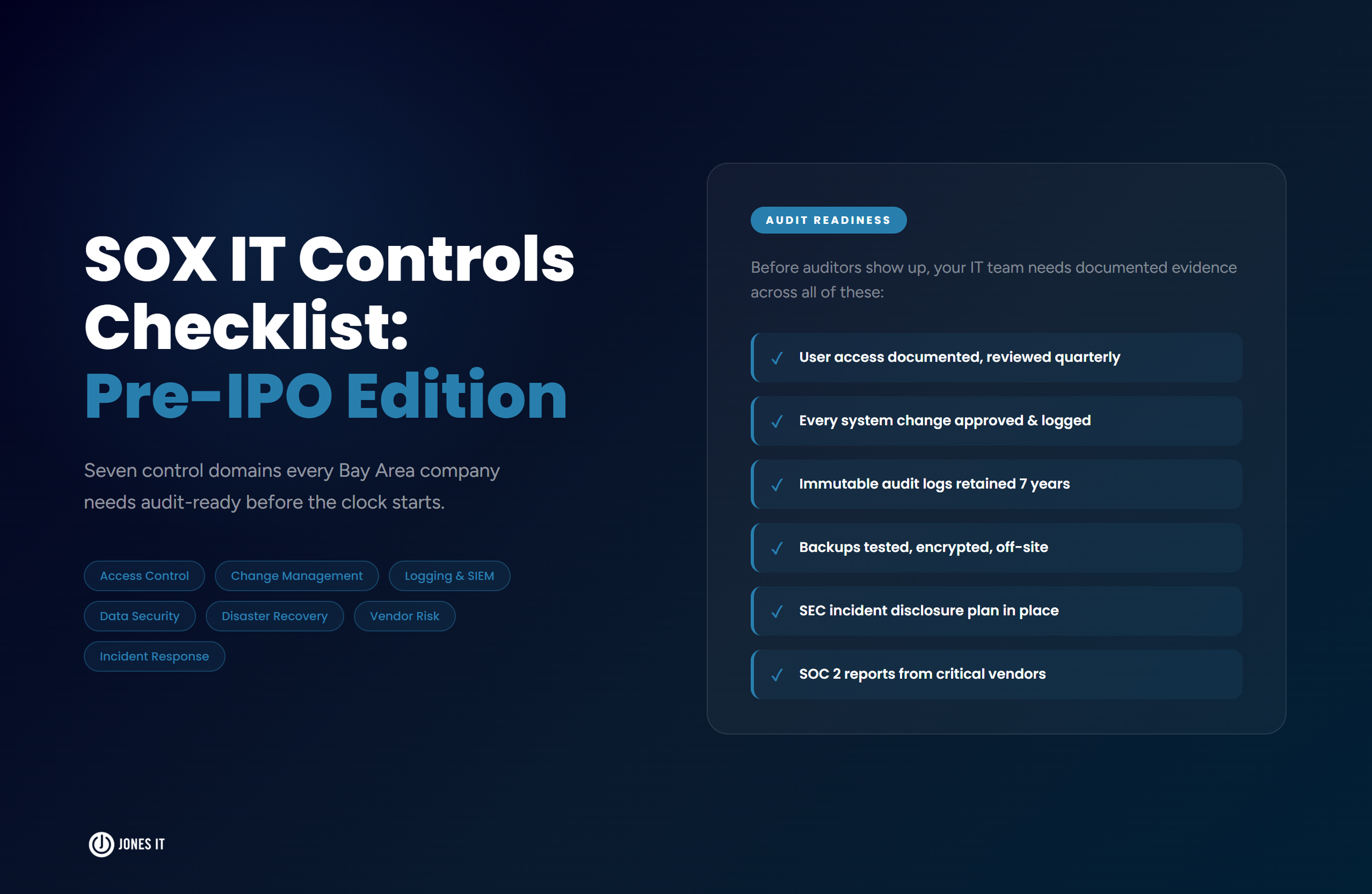
For IT teams supporting SOX compliance, the requirements translate into a specific set of Information Technology General Controls (ITGCs). These are the foundational controls that auditors test when they evaluate whether financial data can be trusted. Weak ITGCs undermine the reliability of every automated process built on top of them.
Identity and Access Management
Role-Based Access Control (RBAC) and the principle of least privilege (PoLP) are the starting points. Users should have access to only the systems and data they need to perform their specific job functions. Every access provisioning and deprovisioning action should be logged, reviewed quarterly, and documented in a way that gives auditors a clear picture of who had access to what and when. Access reviews that happen once a year are not sufficient; auditors expect ongoing evidence that access is being actively managed.
Segregation of Duties
No single individual should be able to initiate, approve, and record the same financial transaction. Segregation of Duties (SoD) is one of the foundational anti-fraud controls in accounting, and it applies just as clearly to software systems as it does to manual processes. If your engineering team can deploy code to production systems and also access financial data directly, you likely have a SoD gap that auditors will flag. Mapping out these conflicts early and building system-level controls to prevent them is far less painful than addressing them after an audit.
Real-Time Audit Trails and Logging
IT systems must automatically log who accessed a system, what changes were made, and when those changes occurred. Logs must be backed up securely, retained for seven years, and available to auditors on request. Gaps in logging, logs that can be modified by administrators, or systems that only retain activity for 90 days are findings that auditors will note as control deficiencies. The retention requirement alone catches many organizations off guard, particularly those using cloud services that default to short retention windows.
IT Change Management
Any modification to an IT system, application, or database that touches financial data must follow a documented change management process. Changes should be tested before deployment, approved by an authorized individual, and tracked with a clear audit trail. Ad hoc changes that bypass change management are red flags in any SOX audit, particularly in fast-moving development environments where speed and compliance requirements can come into direct tension.
Cybersecurity Measures
SOX compliance and data security overlap in important ways. Organizations are expected to use Security Information and Event Management (SIEM) tools to detect breaches and Data Loss Prevention (DLP) systems to prevent unauthorized transfers of sensitive financial data. A ransomware incident that disrupts financial systems is not only an IT problem. Under Section 409, it may trigger a disclosure obligation, and the SEC has been increasingly aggressive in its expectations around the speed and precision of those disclosures.
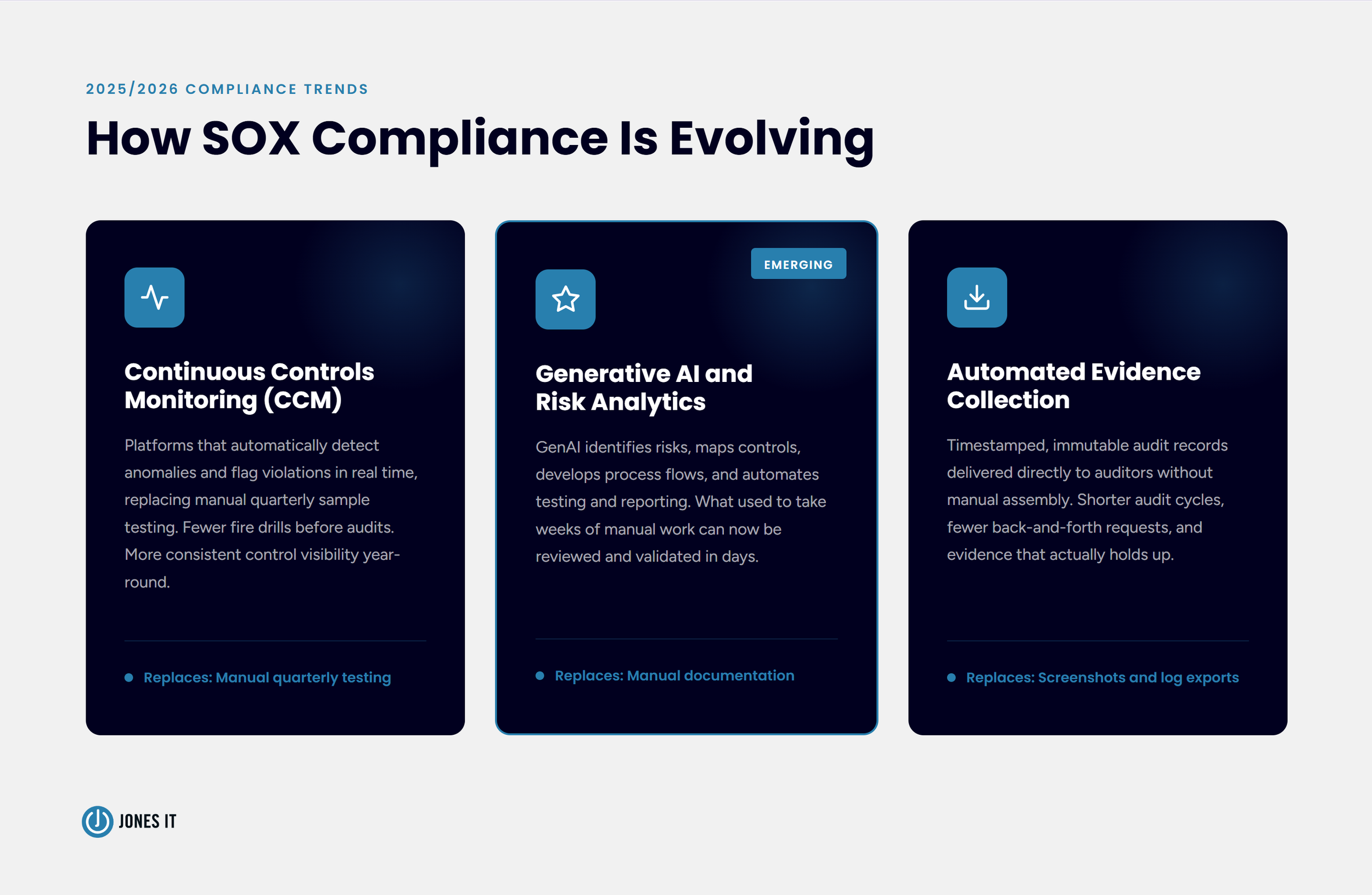
How SOX Compliance Is Evolving in 2025 and 2026
The compliance landscape has shifted considerably in recent years, and the direction is clear: automation is replacing manual processes, and continuous monitoring is replacing point-in-time testing. Organizations that build their programs around these capabilities are finding audits less painful and remediation cycles shorter.
Continuous Controls Monitoring
Companies are moving away from the traditional model of manually sampling controls each quarter and hoping they hold up under audit scrutiny. Continuous Controls Monitoring (CCM) platforms automatically detect anomalies, track control metrics in real time, and flag violations as they occur. For IT teams, this shift means fewer emergency remediation efforts in the weeks before an audit and more consistent visibility into the actual state of controls throughout the year.
Generative AI in Compliance Programs
GenAI tools are now being used to identify risks, map controls to business processes, develop process flow documentation, and automate portions of control testing and reporting. The practical effect is a significant reduction in the time required for audit preparation and a lower risk of oversight. What used to take weeks of manual work to prepare can now be generated, reviewed, and validated in days.
Automated Evidence Collection
Auditors have historically relied on screenshots, manual log exports, and email chains to verify that controls were operating. That approach is increasingly inadequate for the pace at which modern systems change. The emerging standard is automated evidence collection: timestamped, immutable records that can be provided directly to auditors without manual assembly. Organizations that build this capability into their compliance programs early report meaningfully shorter audit cycles and fewer back-and-forth requests from their external auditors.
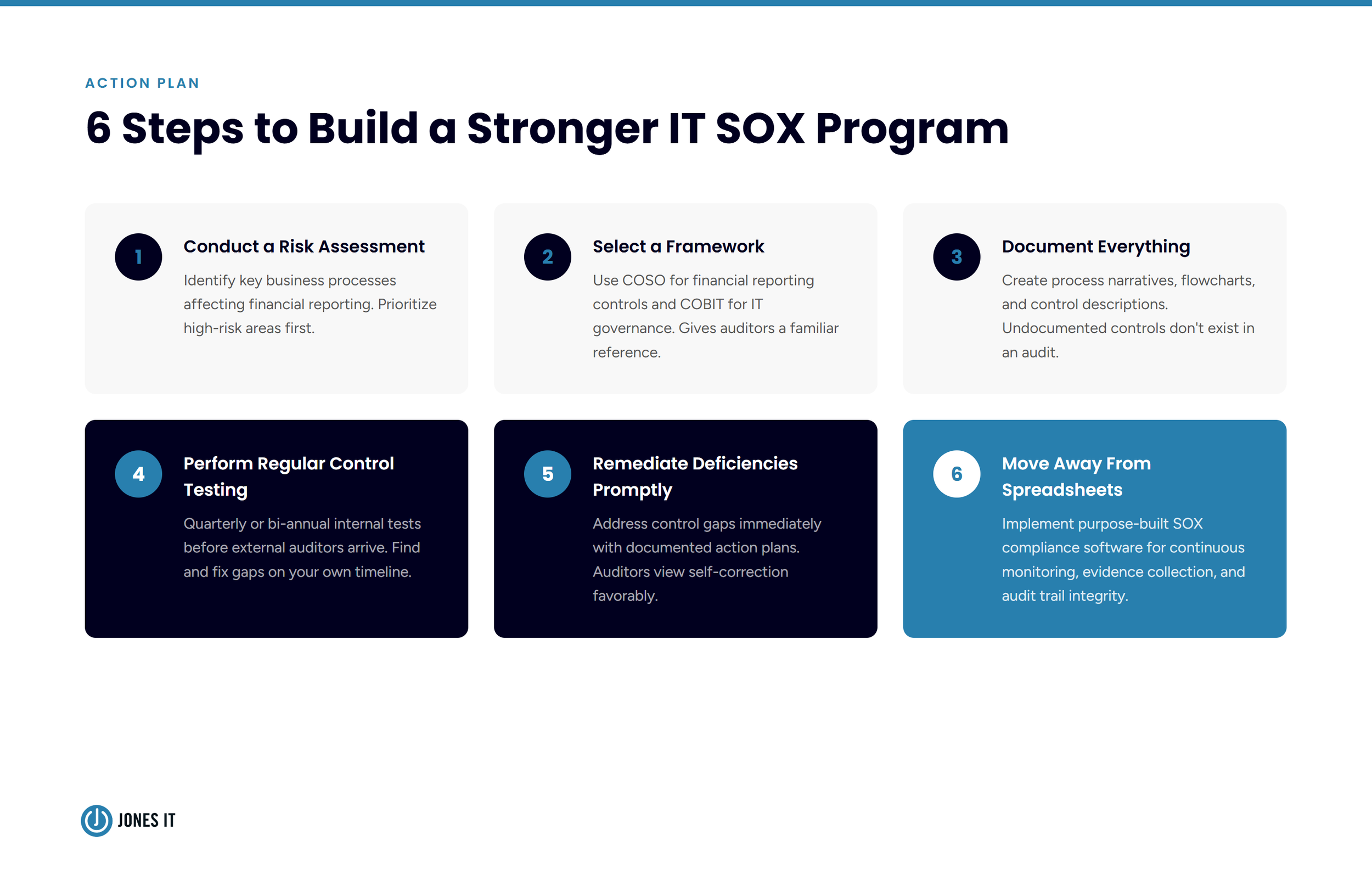
Practical Steps to Build a Stronger IT SOX Compliance Program
Whether you are building a SOX program from scratch or tightening up an existing one, the following steps will put your IT controls on solid ground before your next audit.
Conduct a risk assessment. Identify the key business processes that affect financial reporting and prioritize the areas with the highest potential for error or fraud. Not every system carries equal risk, and your IT controls program should reflect that.
Select an established framework. Use COSO for financial reporting controls and COBIT for IT governance. These frameworks give your program structure and give auditors a familiar reference point.
Document everything. Create clear process narratives, flowcharts, and control descriptions. Undocumented controls are not visible in an audit, even if they are functioning exactly as intended.
Perform regular control testing. Run internal tests quarterly or biannually before your external auditors arrive. Testing your own controls gives you time to remediate gaps rather than explain them.
Remediate deficiencies promptly. When you identify a control gap or material weakness, address it immediately with a documented action plan. Auditors look favorably on organizations that identify and correct their own issues.
Move away from spreadsheets. Purpose-built SOX compliance software provides continuous monitoring, structured evidence collection, and a clear audit trail that manual processes cannot match. The time savings typically justify the investment well before the first audit.
IT Is a SOX Stakeholder, Not a Support Function
The companies that handle SOX compliance well do not treat IT as a support function that gets looped in when finance needs something. Rather, they build IT into the compliance program from the start, define controls at the system level, and invest in automation before audit pressure forces their hand. The organizations that struggle are the ones that discover, during their first serious audit, that their IT infrastructure was never designed with ICFR in mind.
As technology environments businesses operate in grow more complex, SOX compliance requirements are not going to become simpler. The good news is that the tools and frameworks available to IT teams have never been better, and the path from a fragile, manual compliance program to a resilient, auditable one is well established.
If your organization is approaching an IPO, expanding into public markets, or working to tighten financial controls ahead of a coming audit, we can help you assess where your IT environment stands and what needs to change.
Reach out to our team to talk through your environment or talk about your IT governance, cybersecurity, and compliance strategy.