SOX IT Controls Checklist: What Every Pre-IPO Company Needs
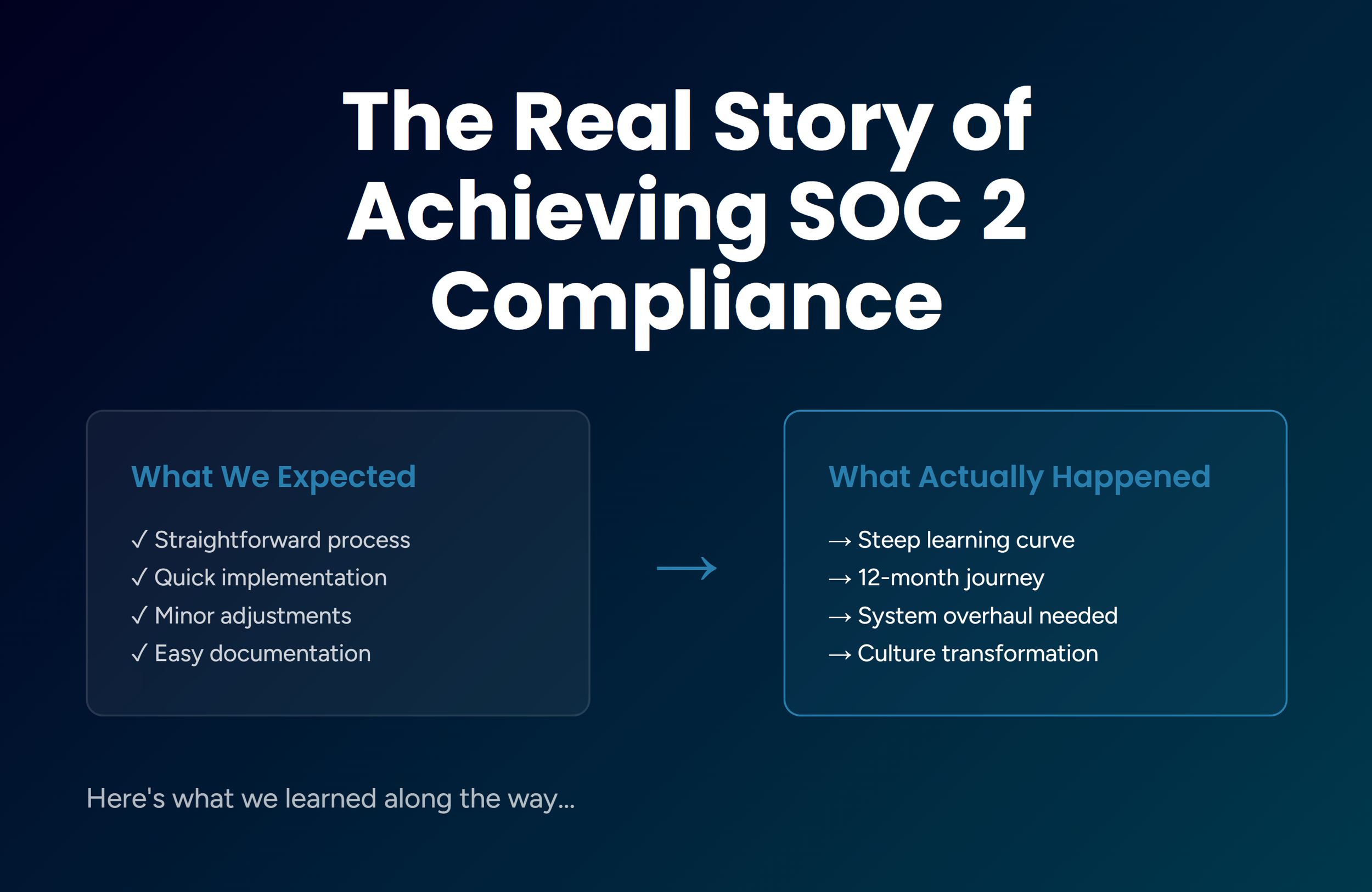
The email arrived on a Tuesday morning. A fintech company in SoMa had just closed its Series C and hired its first Big Four auditor. By Wednesday, the auditor's team was asking for documentation of IT general controls: access logs, change management records, and evidence of segregation of duties across financial systems. The IT director had three weeks to produce it all.
He had two of those three things. Sort of. The access logs existed but were scattered across five different systems with no centralized review process. Change management was informal. And segregation of duties? On a team of eight engineers who all had admin access to the ERP? That was going to be a conversation.
If your company is on the path to an IPO, a SPAC transaction, or a public company acquisition, this story is worth paying attention to. SOX compliance does not wait for you to feel ready. A SOX IT controls checklist is a structured set of IT General Controls that your team needs to implement and evidence before auditors arrive. Getting that checklist in order before they show up makes all the difference.
This post walks you through the core IT controls required for SOX compliance and gives you a concrete checklist for getting your systems audit-ready. We also cover the common pitfalls we see at growing Bay Area companies before they cross the SOX finish line.
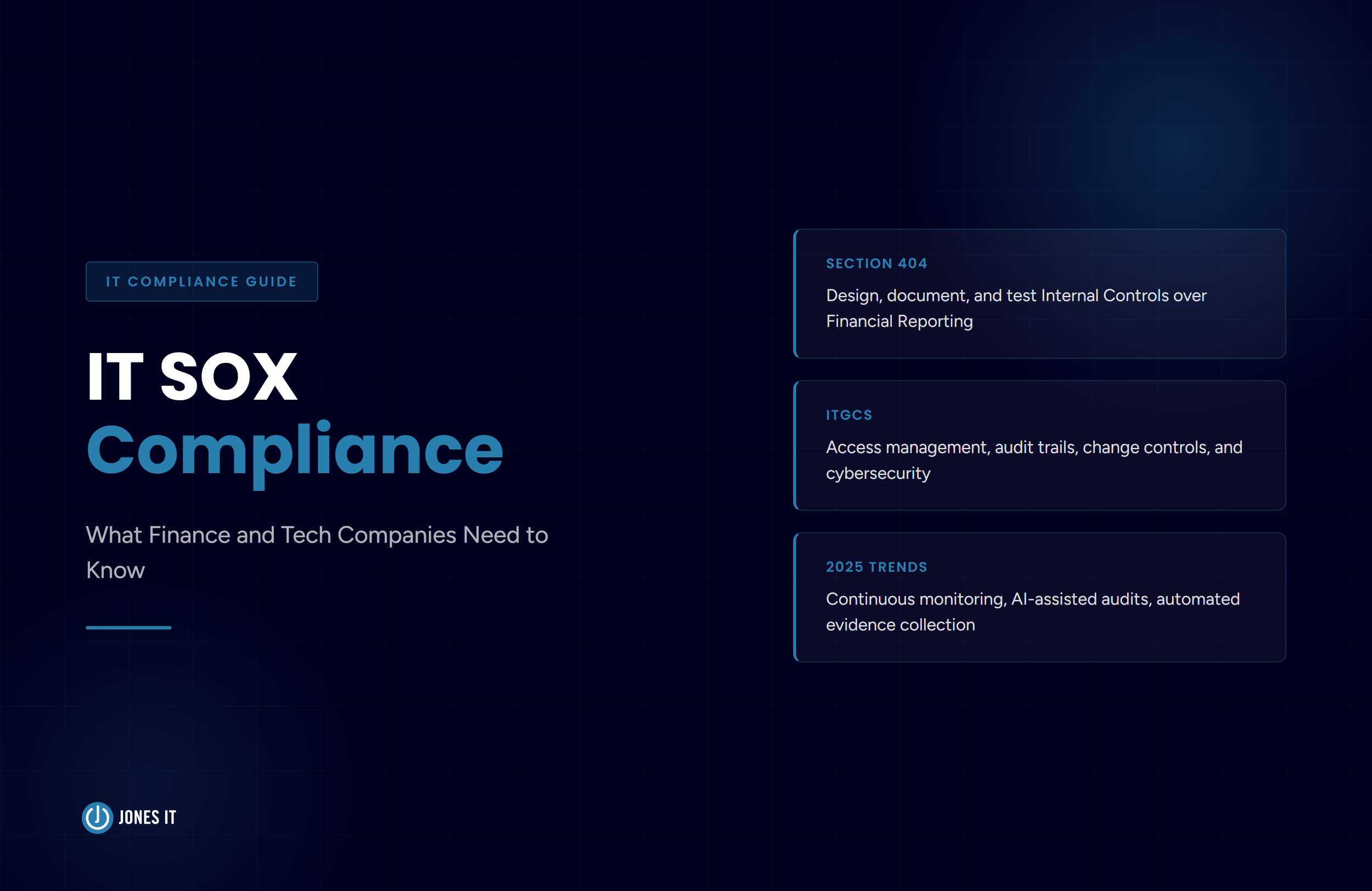
What Is SOX IT Compliance?
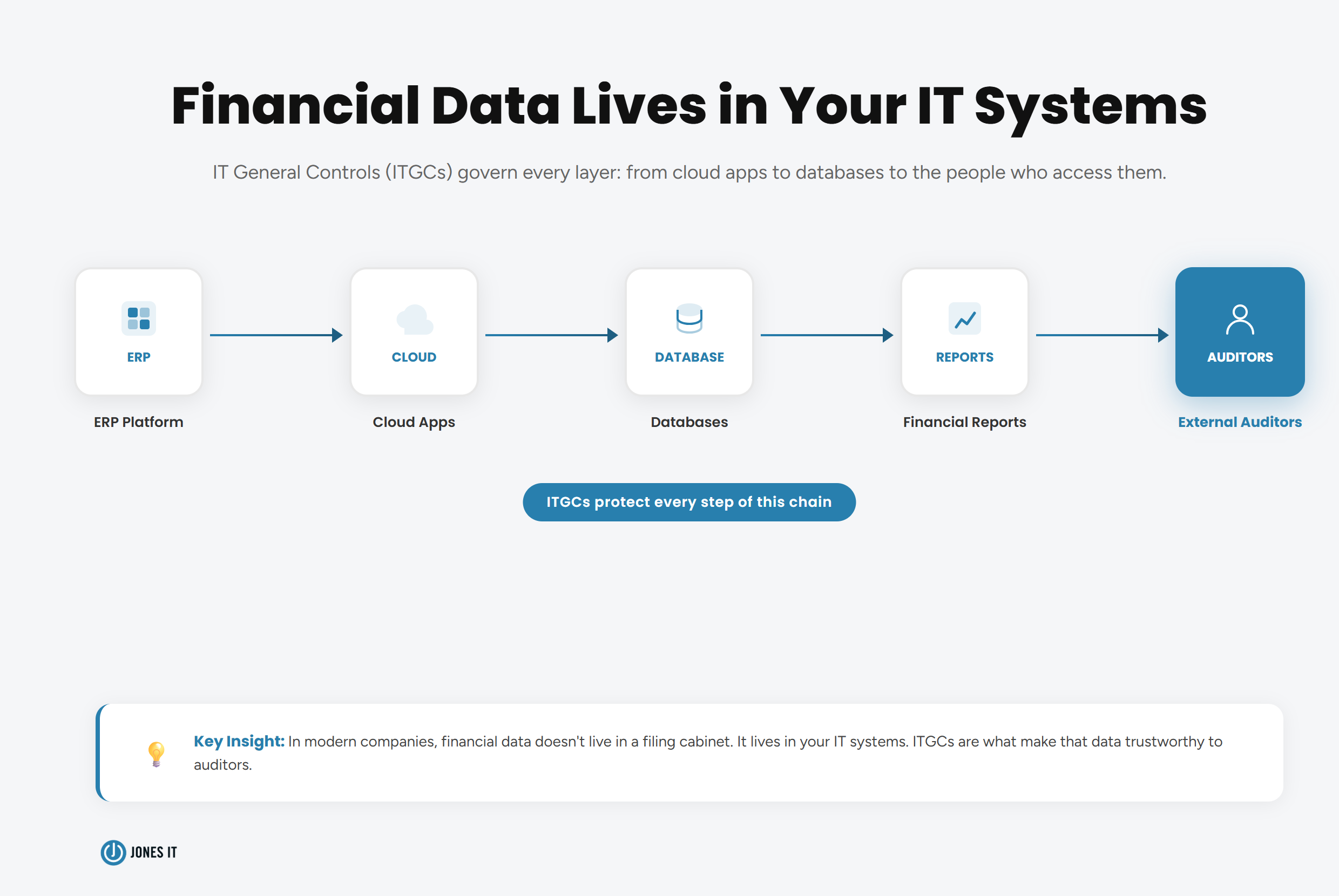
The Sarbanes-Oxley Act of 2002, commonly called SOX, was enacted to protect investors by improving the accuracy and transparency of corporate financial disclosures. SOX IT controls, also called IT General Controls (ITGCs), are the policies and procedures that govern the security and integrity of financial data in IT systems subject to the Sarbanes-Oxley Act.
For IT teams, the relevant provision is Section 404, which governs SOX Section 404 IT controls and requires companies to establish, test, and attest to the effectiveness of Internal Controls over Financial Reporting (ICFR).
In practice, the vast majority of those internal controls live inside your IT systems. Financial data flows through ERP platforms, databases, cloud applications, and reporting tools. Securing that data, controlling who can access and modify it, and documenting every change is the work of IT general controls (ITGCs).
If you want a deeper walkthrough of how SOX IT compliance works from an implementation standpoint, we covered that in detail in our post How to Prepare IT Systems for SOX Compliance. This post focuses specifically on the checklist: the domains you need to cover and the controls that auditors will test.
The Seven Core IT Control Domains for SOX Compliance
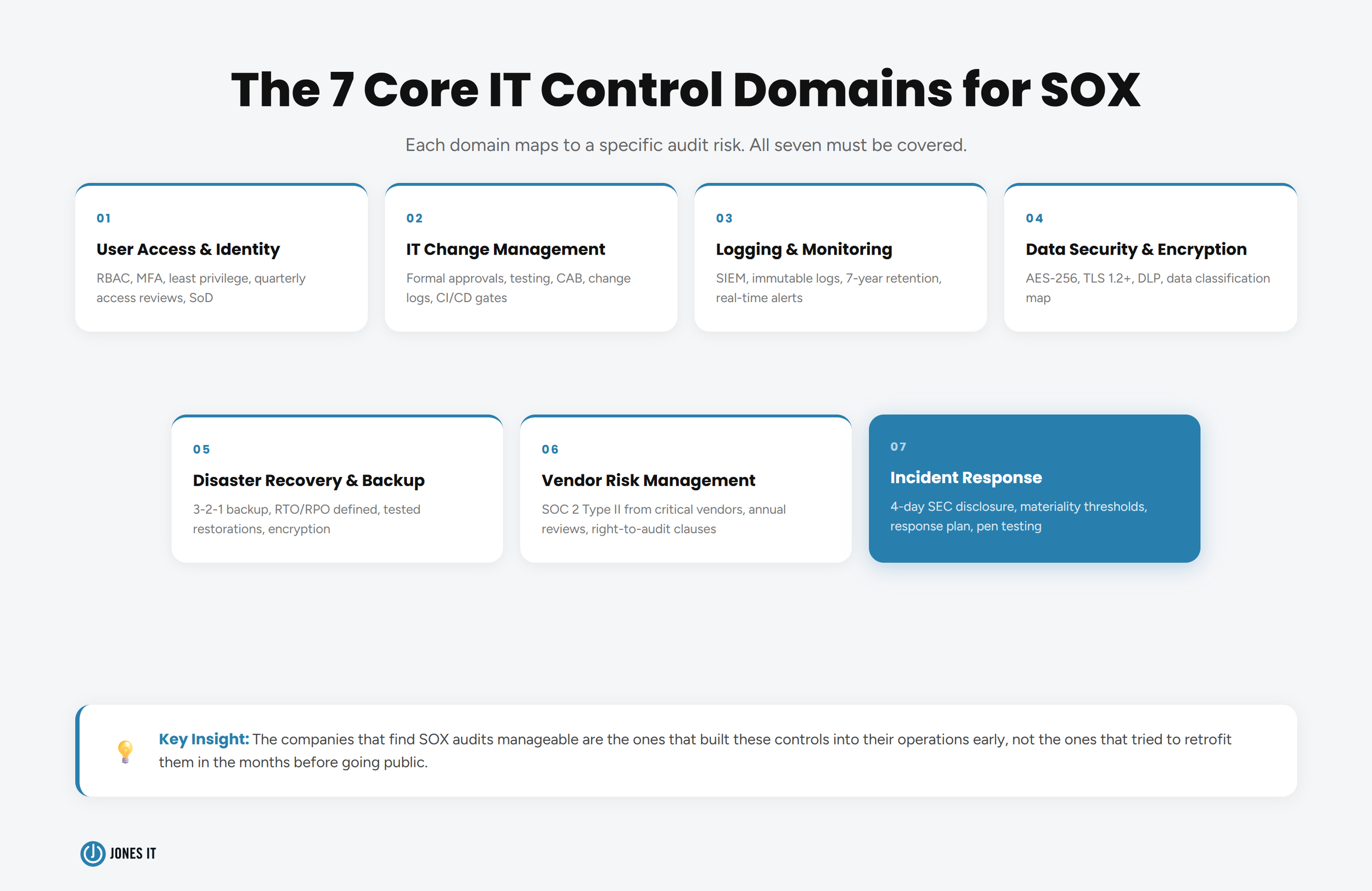
SOX auditors examine IT general controls across seven major areas, each mapping to a specific risk: unauthorized access, undetected tampering, data loss, vendor exposure, inadequate incident response, and non-compliance with SEC disclosure rules. Here is what you need to cover in each domain.
1. User Access Control and Identity Management
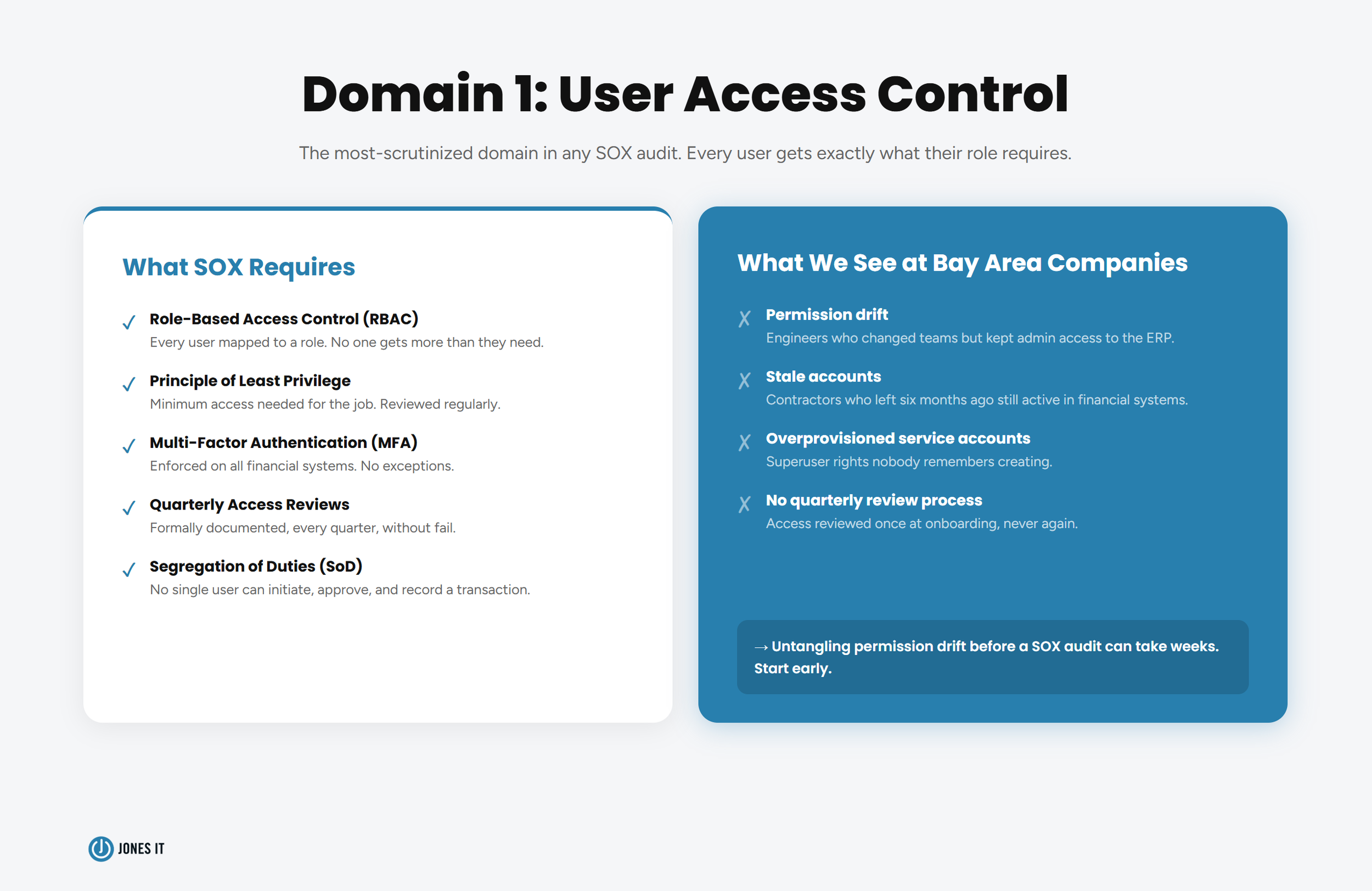
This is the domain auditors scrutinize most closely, and the one where fast-growing companies are most likely to have gaps. The core principle is least privilege: every user should have access only to the systems and data their role requires, and nothing more.
For SOX purposes, that means implementing Role-Based Access Control (RBAC) across all financial systems, enforcing Multi-Factor Authentication (MFA), and conducting access reviews at least quarterly. It also means addressing Segregation of Duties (SoD): no single individual should be able to initiate, approve, and deploy a transaction or change. At smaller companies where one person sometimes wears three hats, this requires careful design.
2. IT Change Management
Any modification to a system, database, or application that touches financial data needs to follow a documented change management process. An informal "let me push a quick fix" culture does not survive a SOX audit.
A compliant change management process includes formal change requests, testing in a non-production environment, approval from a Change Advisory Board (CAB) or equivalent, and post-implementation reviews. Every step needs documentation because, as far as your auditor is concerned, if it is not written down, it did not happen.
3. System Access Logging and Monitoring
SOX requires organizations to maintain immutable audit trails of all user activity and system processes that touch financial data. That means real-time logging, centralized log management, and a process for reviewing and acting on what those logs show.
Many companies use Security Information and Event Management (SIEM) tools to aggregate logs across systems, detect anomalies, and generate alerts for suspicious behavior. The keyword is immutable. Logs that can be altered after the fact offer no audit value, and auditors know it.
4. Data Security and Encryption
Sensitive financial data must be encrypted both at rest and in transit. The current standards are AES-256 for data at rest and TLS 1.2 or higher for data in transit. Beyond encryption, Data Loss Prevention (DLP) solutions should be in place to prevent unauthorized data transfers.
This domain also covers data classification. Your team needs to know which data is subject to SOX, where it lives, and who can access it. Without a clear data map, you cannot demonstrate that controls are comprehensive.
5. Disaster Recovery and Data Backup
SOX requires documented disaster recovery procedures with defined Recovery Time Objectives (RTOs) and Recovery Point Objectives (RPOs). Financial records must be backed up to an off-site, encrypted location to ensure business continuity in the event of an outage or cyberattack.
The backup policy alone is not sufficient. Auditors also require evidence that backups are tested regularly and that the recovery process actually works. A backup you have never restored is a backup you cannot count on.
6. Third-Party and Vendor Risk Management
Your SOX obligations do not stop at your own perimeter. If a third-party SaaS provider or cloud vendor handles financial data on your behalf, you are responsible for the controls governing that data.
For critical vendors, the standard is a SOC 2 Type 2 report, which is an independent audit of their security controls over a defined period. Vendor risk management needs to be an ongoing process, not a checkbox at onboarding. Request SOC 2 reports annually, review them, and document any exceptions or gaps.
7. Incident Response
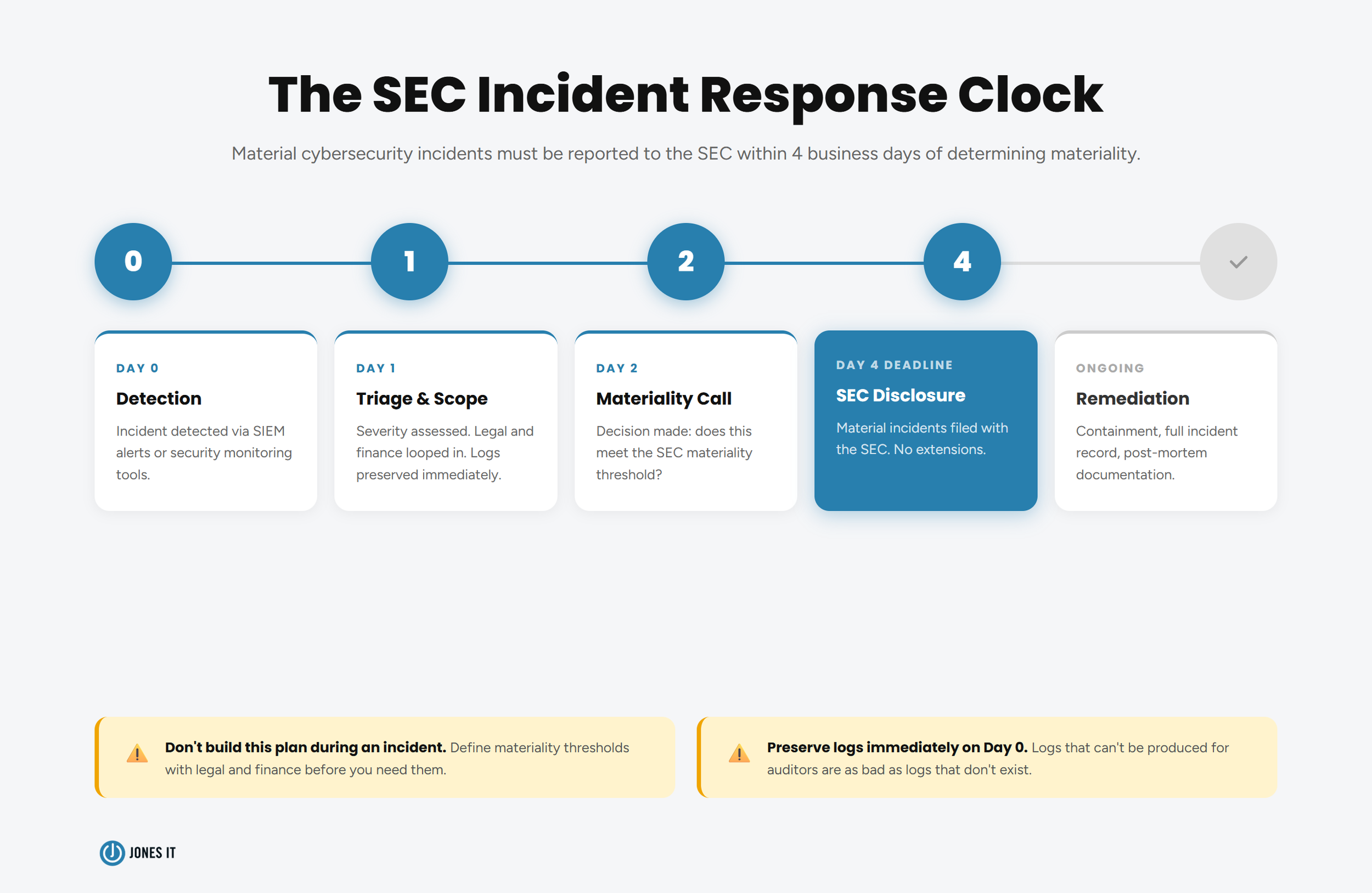
Under rules adopted by the SEC in 2023, public companies must report material cybersecurity incidents within four business days of determining that an incident is material. These SOX incident response requirements demand rapid detection, escalation, and communication capabilities that many IT teams are not currently set up to deliver.
Your incident response plan must define what constitutes a material incident, who makes that determination, how quickly, and what the communication chain looks like. For pre-IPO Bay Area companies, building this process before you need it is significantly less painful than building it during one.
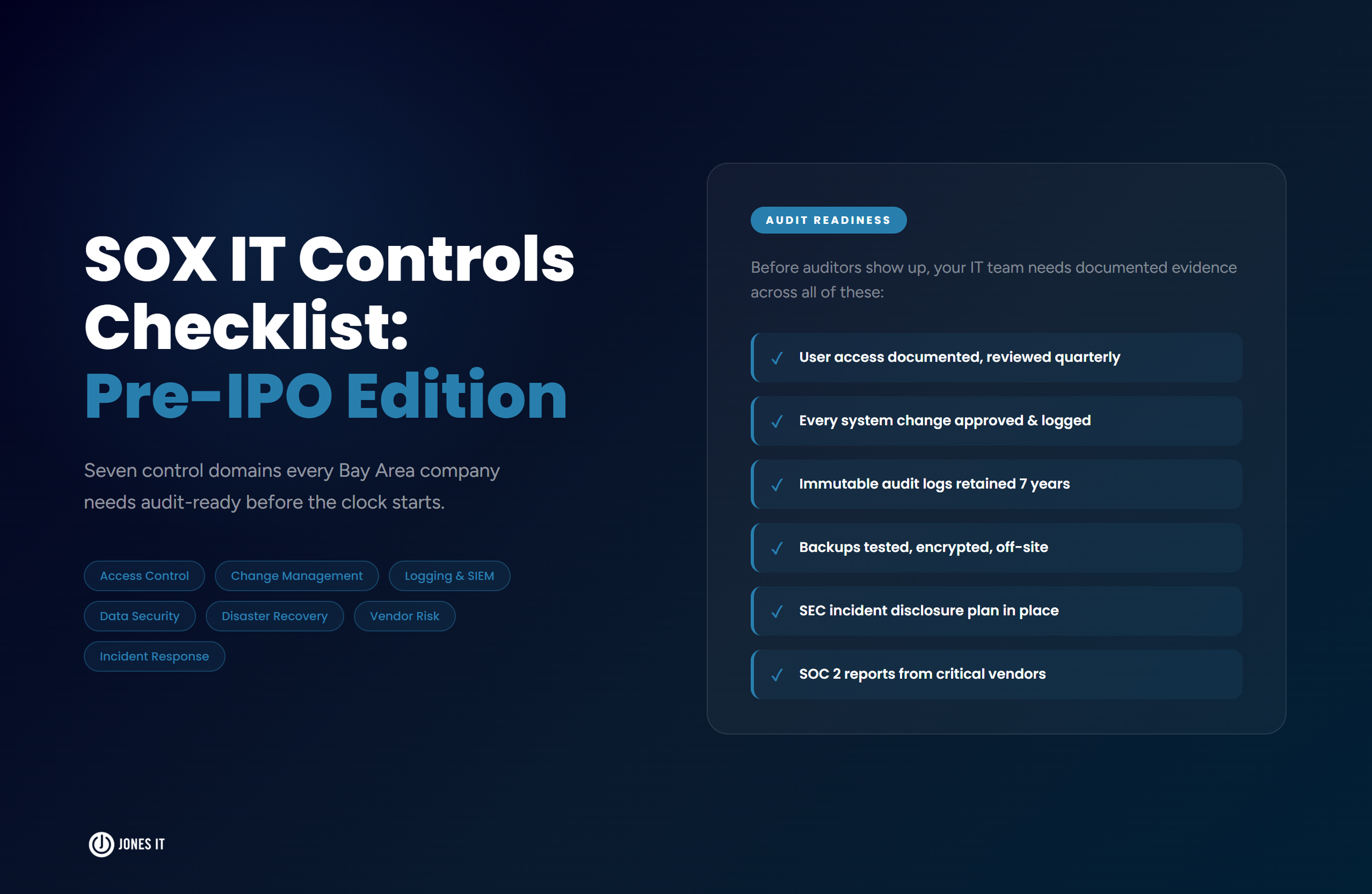
The SOX IT Controls Checklist
The following checklist covers the operational steps your IT team needs to take to prepare for a SOX audit. We have organized it by control domain, though in practice, these steps overlap and reinforce each other.
User Access and Identity
Implement RBAC across all financial systems. Map every role to the minimum permissions required, and document the mapping.
Enforce MFA for all users with access to financial applications, ERP systems, and supporting infrastructure.
Conduct quarterly access reviews. Confirm that access rights still match current roles. Revoke access promptly when employees change roles or leave.
Document and enforce SoD policies. No single user should be able to initiate, authorize, and post a transaction.
Establish a formal offboarding process that includes immediate access revocation across all systems.
Change Management
Create a formal change management policy. Define what constitutes a change, the required approval workflow, and the documentation standards.
Require all changes to be tested in a non-production environment before deployment to production.
Maintain a change log with timestamps, approver names, and post-implementation review outcomes.
Establish an emergency change process for critical fixes, with the same documentation requirements applied after the fact.
Logging and Monitoring
Centralize logs from all financial systems, databases, and supporting infrastructure into a SIEM or equivalent platform.
Configure alerts for suspicious activity: privilege escalation, access outside business hours, bulk data exports, and failed login attempts.
Ensure logs are immutable. Logs that can be altered or deleted do not satisfy SOX requirements.
Assign responsibility for log review. Someone needs to own this process and document that it happens.
Data Security
Encrypt all financial data at rest (AES-256) and in transit (TLS 1.2+).
Deploy DLP controls to detect and prevent unauthorized transfers of financial data.
Maintain a current data map. Know where all SOX-relevant data lives, who can access it, and what controls govern it.
Disaster Recovery
Document RTOs and RPOs for all systems that support financial reporting.
Back up financial records to an off-site, encrypted location. Automate the backup process and monitor for failures.
Test your recovery process at least annually. Document the test, the outcome, and any remediation steps taken.
Vendor Management
Inventory all third-party vendors that have access to or process financial data.
Request SOC 2 Type II reports annually from critical vendors. Review them and document any exceptions.
Include SOX-related requirements in vendor contracts and right-to-audit clauses where appropriate.
Incident Response
Maintain a documented incident response plan that defines detection, escalation, and communication processes.
Define materiality thresholds with input from legal and finance so that the IT team knows when and how to escalate.
Log all security incidents, track their resolution, and maintain records for auditor review.
Conduct periodic penetration tests and vulnerability assessments to verify that monitoring controls are functioning.
Where Pre-IPO Companies Most Often Fall Short
We work with a lot of Bay Area fintech and SaaS companies that are building out their SOX readiness programs for the first time. A few gaps come up repeatedly.
The spreadsheet problem
Many companies document IT controls in spreadsheets. Consequently, version control is inconsistent, the data is isolated in individual inboxes, and there is no reliable way to demonstrate to an auditor that the process was actually followed. Moving to a Governance, Risk, and Compliance (GRC) platform is not a small investment, but is notably more efficient than the alternative, which is spending significantly more time and money on manual audit preparation every year.
Access creep
In a fast-moving company, access gets granted quickly and revoked slowly. By the time a SOX audit arrives, it is common to find former employees in systems, engineers with admin access they no longer need, and roles that no longer reflect actual job functions. Quarterly access reviews are not optional under SOX. Building them into your calendar now is far better than cleaning up years of accumulated access in the weeks before an audit.
Informal change management
Startup culture moves fast. That is one of its advantages. But "move fast" and "change management documentation" do not coexist naturally. The discipline of documenting changes, testing them properly, and getting formal approvals has to be built deliberately. We have seen companies scramble to reconstruct six months of change history from Slack messages and Git commits. It is possible, but not something you want to do the week before your auditors arrive.
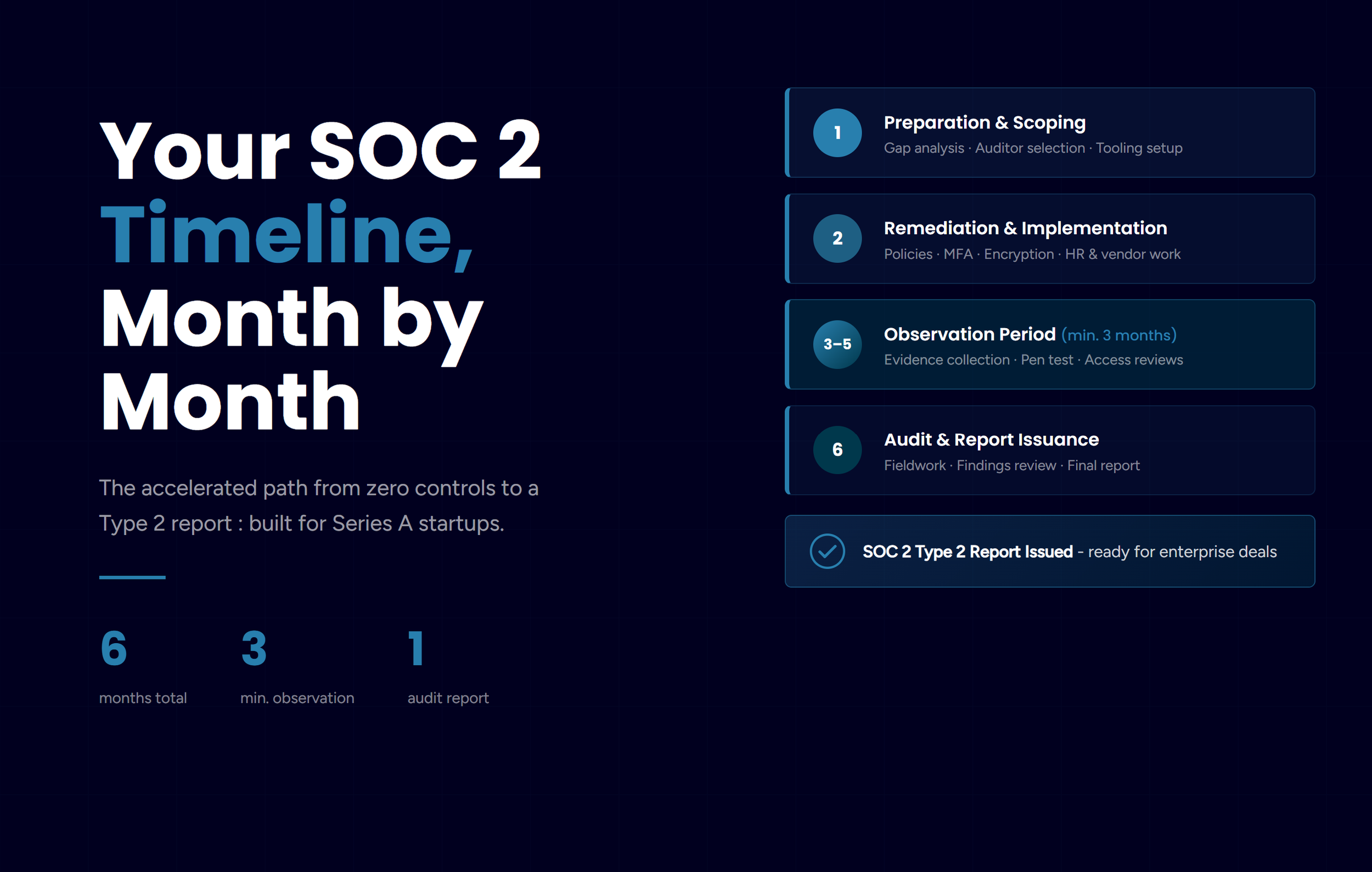
Getting SOX-Ready Before the Auditors Arrive
SOX IT compliance is not a one-time project. It is an ongoing program that requires consistent execution, regular review, and a team that understands what auditors are looking for. The good news is that building strong IT general controls makes your systems more secure, more reliable, and easier to manage, regardless of whether you are ever audited.
The companies that find SOX audits manageable are the ones that built these controls into their operations early, not the ones that tried to retrofit them in the months before going public.
If you are a pre-IPO company working through your SOX IT readiness, we can help. Our Compliance Kickstarter Program is designed specifically for companies that need to build out IT general controls quickly and systematically. Reach out to us to talk through where you are and what it would take to get audit-ready.