IT Infrastructure Checklist for Series A Startups
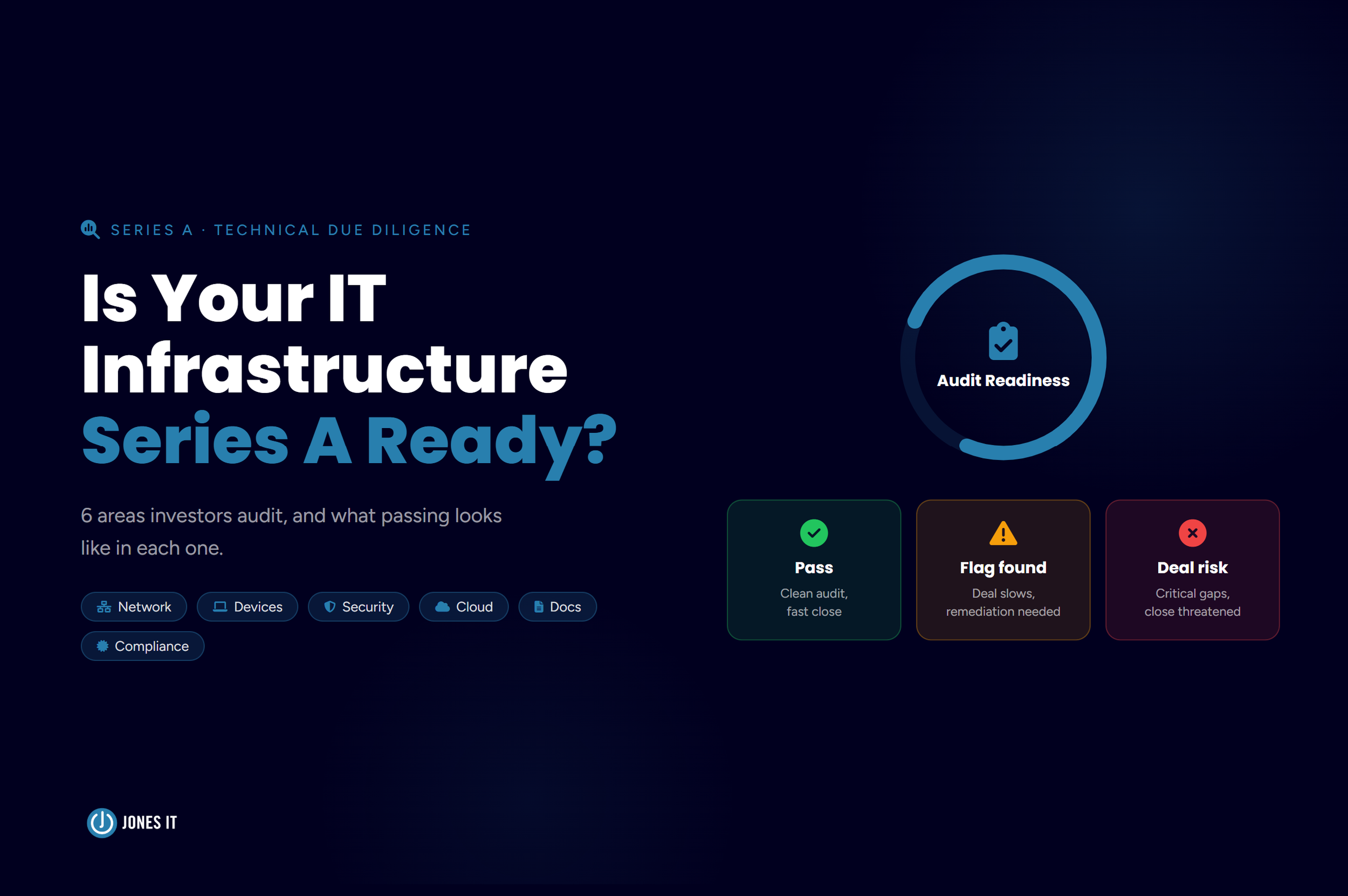
Series A IT infrastructure due diligence is the technical review investors conduct to verify that a startup’s systems, security controls, and documentation are scalable enough to support institutional capital.
Picture this: You are at a VC meeting. The product demo went well. Revenue metrics are solid. The founding team answered every question about the market, the roadmap, and the competitive moat. Then the technical auditor leans forward and asks: “Walk me through your endpoint management policy.”
For a lot of founders, that’s the moment the room goes quiet.
It’s not that they haven’t thought about IT infrastructure. They have, in the way you think about something when it mostly works, and nobody’s complaining. What they haven’t done is look at it through an investor’s lens. And that’s a different exercise entirely.
At Jones IT, we work with Bay Area startups at exactly this inflection point: post-seed, pre-raise, or in the middle of due diligence. We’ve seen what auditors flag, what founders overlook, and what the gap between the two tends to cost. This post walks through the IT infrastructure areas that actually get scrutinized during a Series A technical audit, and what “good” looks like in each one.
Why Your IT Infrastructure Is Part of the Fundraising Story
Investors at the Series A stage are betting on scale. They’re not just evaluating your traction today, but asking whether your operations can support ten times the headcount, five times the customer base, and the scrutiny of enterprise buyers who will run their own security questionnaires before signing a contract.
Brittle infrastructure is a liability on two fronts. First, it signals that the company’s operational maturity hasn’t kept pace with its product maturity. Second, it creates real post-close costs. For instance, if the infrastructure needs a full rebuild after funding, that’s engineering time and capital that could have gone elsewhere.
Well-instrumented, documented, and secure systems tell a different story. They tell investors that the company’s IT infrastructure can scale without the wheels coming off, and that growth is just an execution problem, and does not require a complete rebuild.
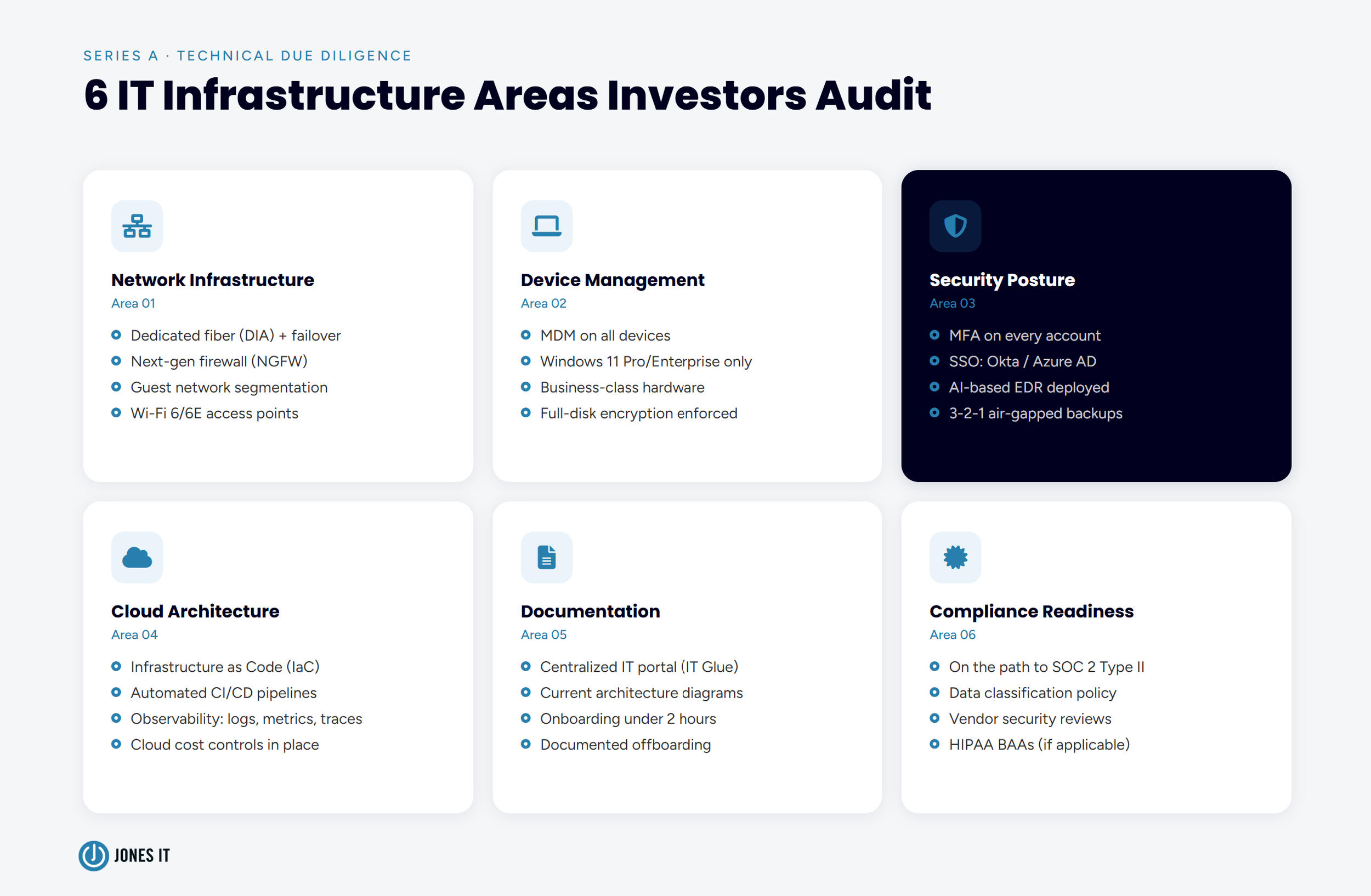
The sections below cover the six areas we see come up most often in technical due diligence for Series A startups.
Network and Physical Infrastructure
At the seed stage, a consumer-grade router and a shared office Wi-Fi network are fine. At Series A, they’re a huge red flag. Auditors look for infrastructure that can handle high device density, support remote and hybrid work reliably, and segment sensitive systems from guest access.
Here’s the baseline expectation for a Series A startup:
A dedicated fiber optic connection (DIA) providing symmetric upload and download speeds, essential for cloud-native workflows and video-heavy collaboration.
A failover connection (a secondary line such as 5G or cable) so that a single ISP outage doesn’t take the company offline.
A next-generation firewall (NGFW) with deep packet inspection, not a consumer router doing basic traffic routing.
Guest network segmentation: visitors and IoT devices on a separate SSID, fully isolated from any network housing production systems or financial data.
Wi-Fi 6 or Wi-Fi 6E access points to handle high device density without the performance degradation that slows teams down in dense SoMa or Mission Bay offices.
If your office is still running on the router that came with your ISP subscription, that’s worth fixing before due diligence starts. It’s a small line item relative to your round, and it removes a visible flag.
Device Management and OS Compliance
Bring-your-own-device policies are practical at the seed stage when you’re moving fast, have a small team, and everyone trusts everyone. They become a problem when an auditor asks how you know which devices have access to your systems, whether those devices are encrypted, and what happens to access when someone leaves the company.
The answer “we rely on people to be responsible” is not a policy. It’s an assumption.
Here’s what Series A due diligence expects:
A Mobile Device Management (MDM) system, such as Iru (Kandji) or Jamf for Mac-heavy teams or Microsoft Intune for Windows environments, that centrally manages and monitors all company devices.
All workstations are running a current macOS version or Windows 11 Pro or Enterprise. “Home” editions of Windows are a specific audit red flag because they lack BitLocker encryption and cannot be enrolled in remote management systems.
Business-class hardware (MacBooks, Dell Latitude, Lenovo ThinkPad, or equivalent) with on-site warranty coverage. This keeps repairs from creating employee downtime and signals that the company treats its equipment as a managed asset, not an ad hoc collection.
Full-disk encryption is enforced on all devices, with the ability to remotely wipe a device if it’s lost or an employee departs.
Device management is one of the areas where the gap between seed-stage habits and Series A expectations is most visible, and it’s fixable. If you’re not already running MDM, getting it in place two to three months before you expect due diligence is the right call.
Security Posture: The Zero-Trust Baseline for Series A
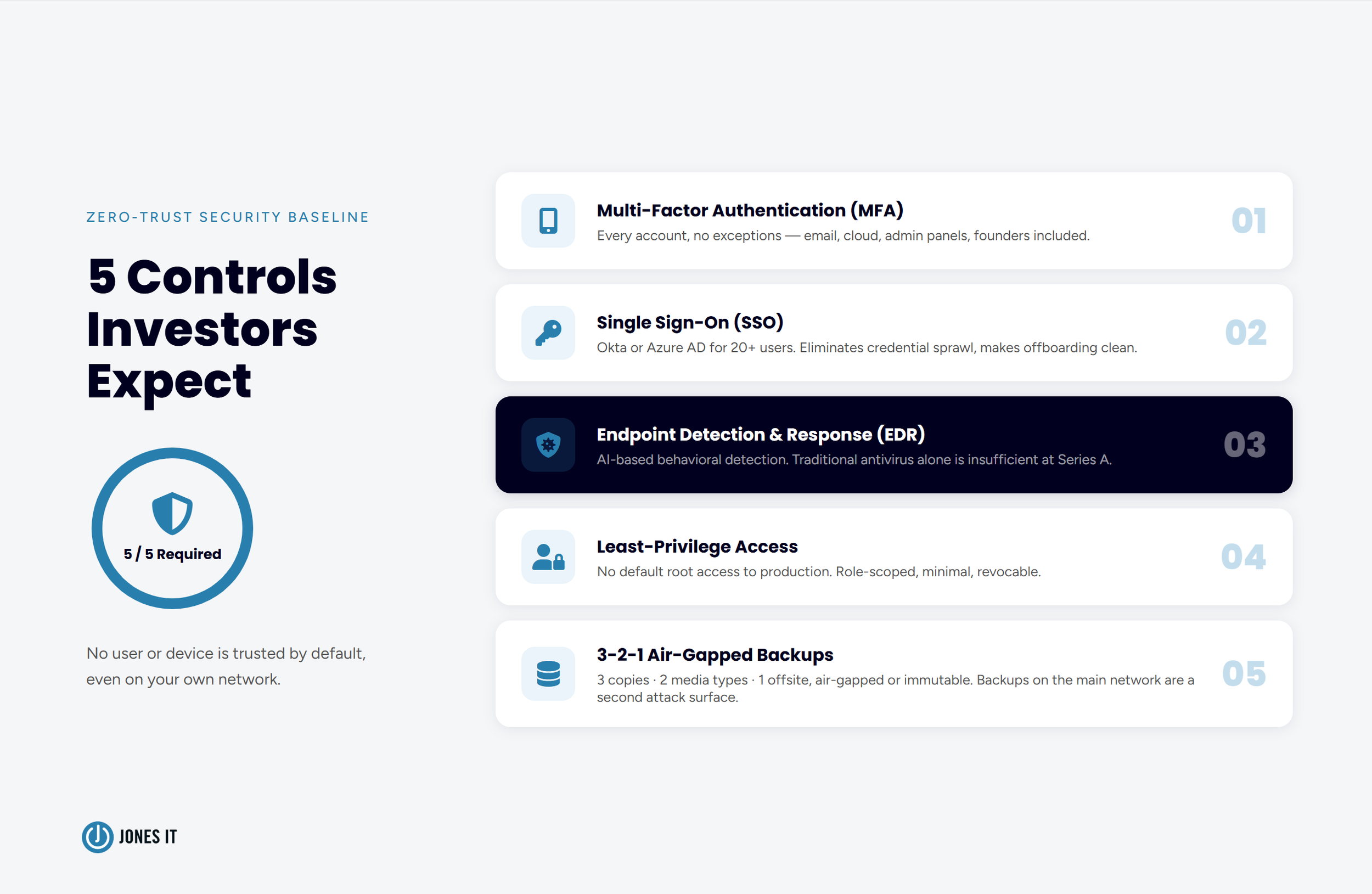
Security controls are what technical auditors spend the most time evaluating at Series A. Strong IT infrastructure security means more than antivirus; auditors look at whether your architecture reflects a zero-trust posture, meaning no user or device is trusted by default just because they’re on your network.
Here are the security controls investors expect at Series A:
Multi-factor authentication (MFA) is enforced on every account, without exception. If there are accounts (email, cloud services, admin panels) that can be accessed with a password alone, that’s a finding. There should be no exceptions, not even for founders or executives.
Single sign-on (SSO). For teams of 20 or more, Okta or Azure AD is the standard. SSO reduces credential sprawl and makes offboarding clean and complete.
Endpoint Detection and Response (EDR). Traditional antivirus software is inadequate. AI-based EDR tools detect behavioral anomalies (a PDF viewer attempting to modify registry keys, for example) that signature-based tools miss entirely.
Least-privilege access controls. No engineer should have root access to production by default. Access should be granted based on role, scoped to what’s needed, and revocable.
Backup architecture that survives ransomware. The 3-2-1 rule applies: three copies of data, on two different media, with one copy kept offsite and air-gapped or immutable. This matters because the most common backup failure mode is backups that are connected to the same network as the primary data. Ransomware can then encrypt both simultaneously.
One area that surprises founders is secret management. Auditors will check your Git history for hardcoded API keys, credentials, or tokens using tools like TruffleHog or GitLeaks. If those exist, even in commits from two years ago, they’re findings. Using a secrets manager like AWS SSM Parameter Store or Doppler for runtime injection, and scanning your repo history before due diligence starts, is worth the effort. The NIST Zero Trust Architecture framework (SP 800-207) provides the authoritative reference if your team needs to formalize the approach. Our cybersecurity and compliance services can help Bay Area startups put these controls in place before due diligence begins.
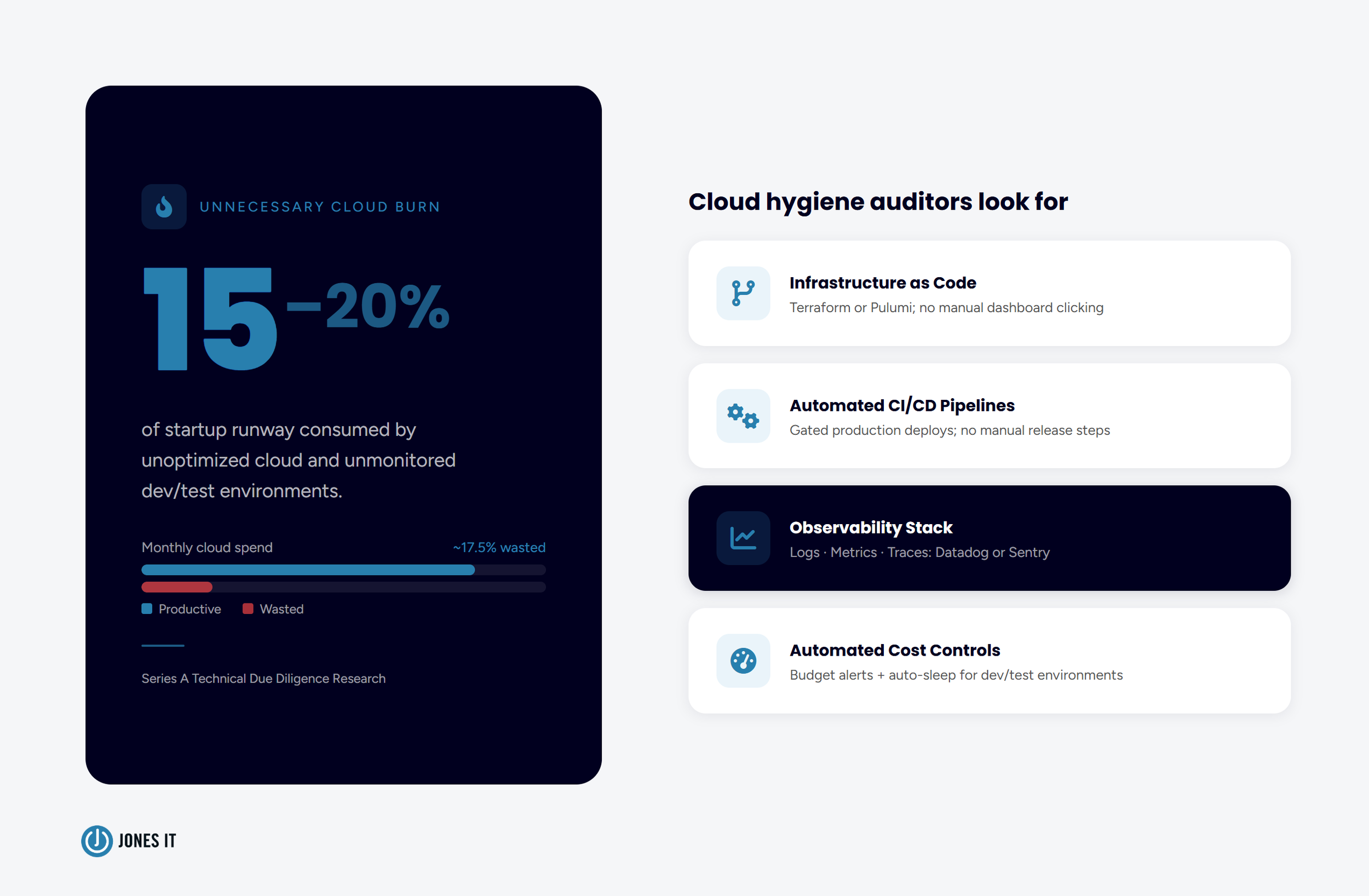
Cloud Architecture and Environment Hygiene
Most Series A startups are cloud-native, and auditors know it. The question isn’t whether you’re using cloud infrastructure; the question is whether you’re using it in a way that’s reproducible, observable, and controlled.
Here are the key signals investors look for:
Infrastructure as Code (IaC). Manual configuration through cloud dashboards leads to environment drift, where production no longer matches what your documentation says it should be. Terraform or Pulumi are the standard tools. If your environments can’t be reproduced from code, that’s a finding.
Automated CI/CD pipelines. GitHub Actions or GitLab CI with gated production deploys. Manual deployment processes are a risk because they rely on individual knowledge and introduce inconsistency.
Observability. Structured logs, latency and error metrics, and distributed tracing. Datadog and Sentry are common choices. Investors want to know you can see what’s happening in your system, not just whether it’s up or down.
Cloud cost controls. Unoptimized cloud services and unmonitored dev/test environments can account for 15 to 20 percent of unnecessary burn. Automated budgets and auto-sleep functions for non-production environments are table stakes.
For fintech or healthtech startups, a hybrid architecture may be required to keep regulated data on-premises. If that hybrid requirement applies to your startup, the documentation of the boundary between cloud and local systems needs to be clear and auditable.
Documentation and the “Bus Factor” Problem
The “bus factor” is the number of people on your team who, if they were suddenly unavailable, would take critical knowledge with them. For early-stage startups, that number is often one. Sometimes it’s the founder or the co-founder. Occasionally, it’s a contractor who left eighteen months ago.
Investors treat a high bus factor as a risk to IT infrastructure continuity. The fix is simple: documentation. However, not just documentation for its own sake, but the kind that means your systems can be understood, operated, and handed off without requiring a specific person to be in the room.
Here’s what good documentation looks like for a Series A audit:
A centralized IT documentation portal (IT Glue or Hudu are common choices) containing network maps, vendor contacts, account credentials (in a password manager, not a spreadsheet), and runbooks for common IT tasks.
Architecture diagrams that reflect your actual current state, not a diagram someone made in 2022 that hasn’t been updated since.
An onboarding process that doesn’t require tribal knowledge, one that brings a new engineer to be productive in under two hours, which is also a strong recruitment signal for senior engineering talent.
A documented offboarding process, including what happens to access, devices, and accounts when someone leaves.
Documentation is the area where we most often see founders underestimate the effort required. It’s not glamorous work. But an auditor who asks to see your network documentation and gets a blank stare is certainly going to write something unfavorable in their report.
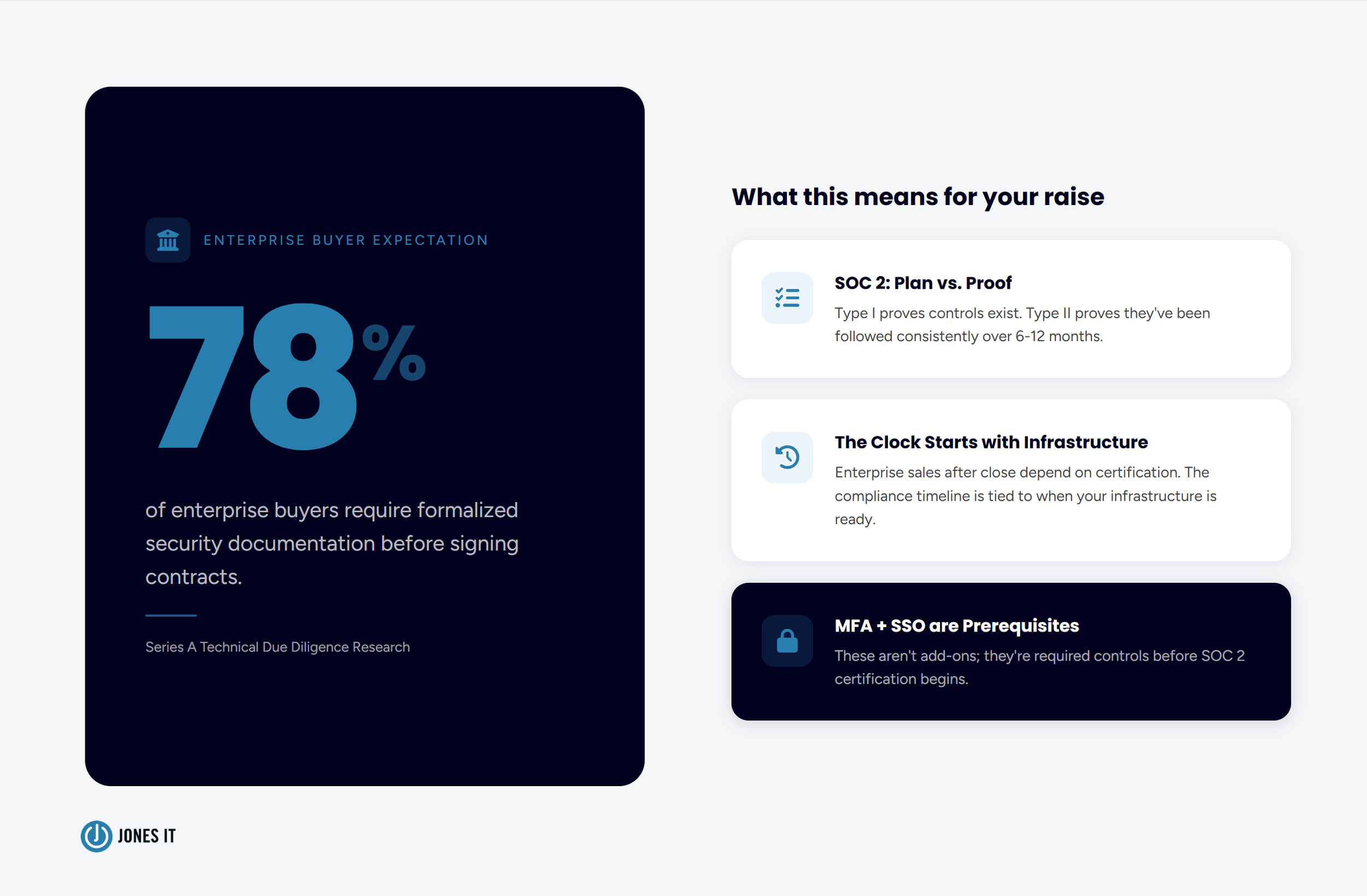
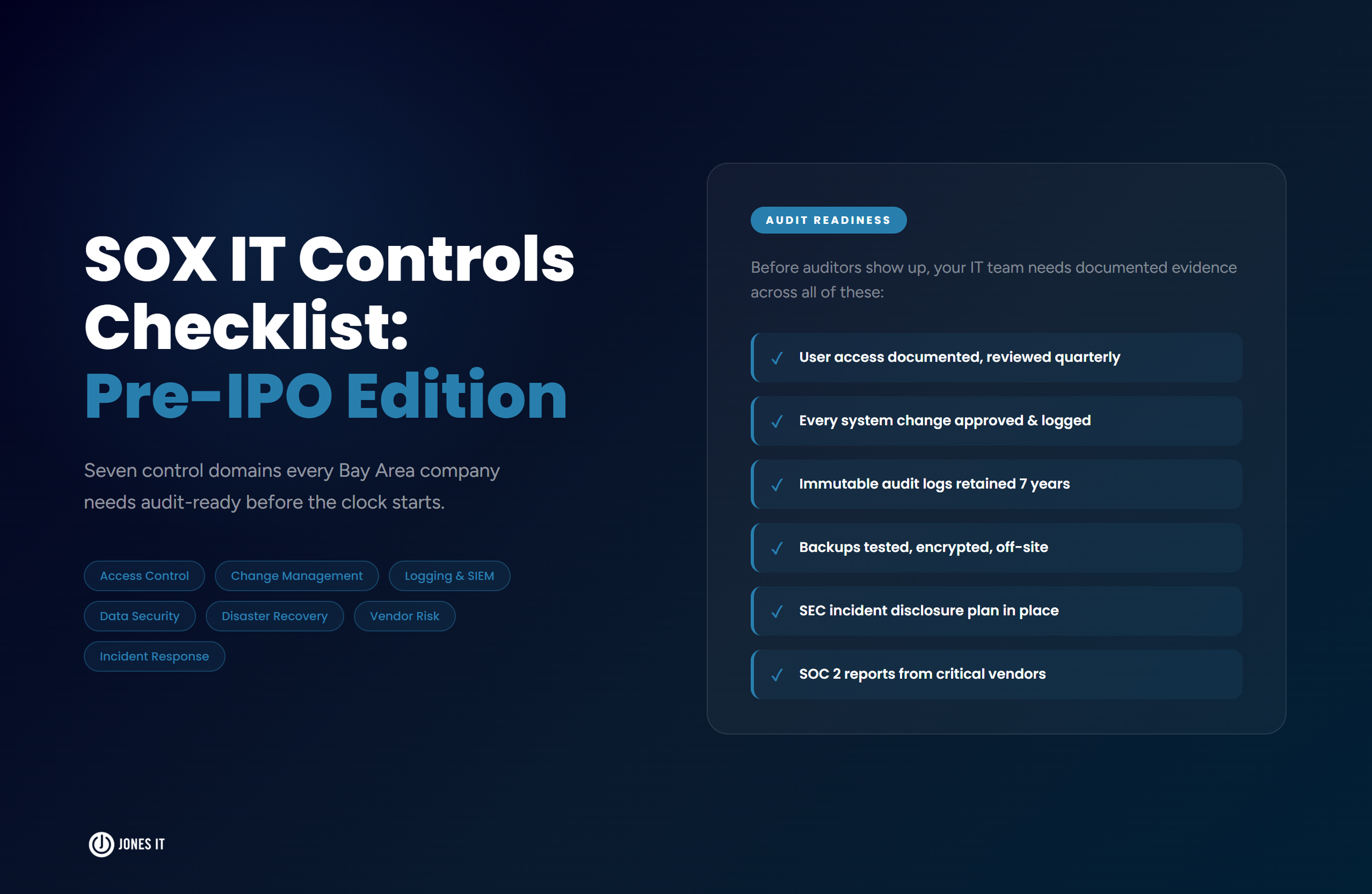
Compliance Readiness: SOC 2, HIPAA, and What Comes Before Certification
You don’t need SOC 2 Type II certification to close a Series A. But you probably need to be credibly on the path to it, and that path has to start with the infrastructure being in the right shape.
SOC 2 Type I proves you have the right controls in place at a point in time. SOC 2 Type II proves you’ve been operating those controls consistently over a period of six to twelve months. Enterprise buyers increasingly require Type II before signing contracts, and 78 percent of enterprise buyers now require formalized security documentation as part of vendor evaluation. If you’re targeting enterprise sales after the close, the timeline to certification matters. See our SOC 2 compliance timeline for Series A startups for a month-by-month breakdown of what that looks like in practice.
Here’s what compliance readiness means before certification:
MFA, SSO, and access controls are already in place, as these are SOC 2 prerequisites, not add-ons.
A data classification policy that identifies what data you hold, where it lives, and who has access to it.
Vendor security reviews for any third-party tools that touch customer data.
For healthtech or biotech startups: HIPAA-compliant data handling, business associate agreements (BAAs) in place with relevant vendors, and audit logs that demonstrate access controls are being enforced.
If you’re not sure whether your current setup meets the technical prerequisites for SOC 2, our Compliance Kickstarter Program is designed to assess your current state and build a roadmap. Getting that assessment done before due diligence starts, rather than during it, is worth the lead time.
How Jones IT Helps Bay Area Startups Pass Technical Audits
The checklist above is not exhaustive, and the relative weight of each area depends on your specific sector, your customer profile, and who’s conducting the audit. A fintech startup selling to regulated financial institutions faces a different scrutiny level than a SaaS company selling to SMBs. What’s consistent across both is that infrastructure gaps discovered during due diligence slow deals down and sometimes kill them.
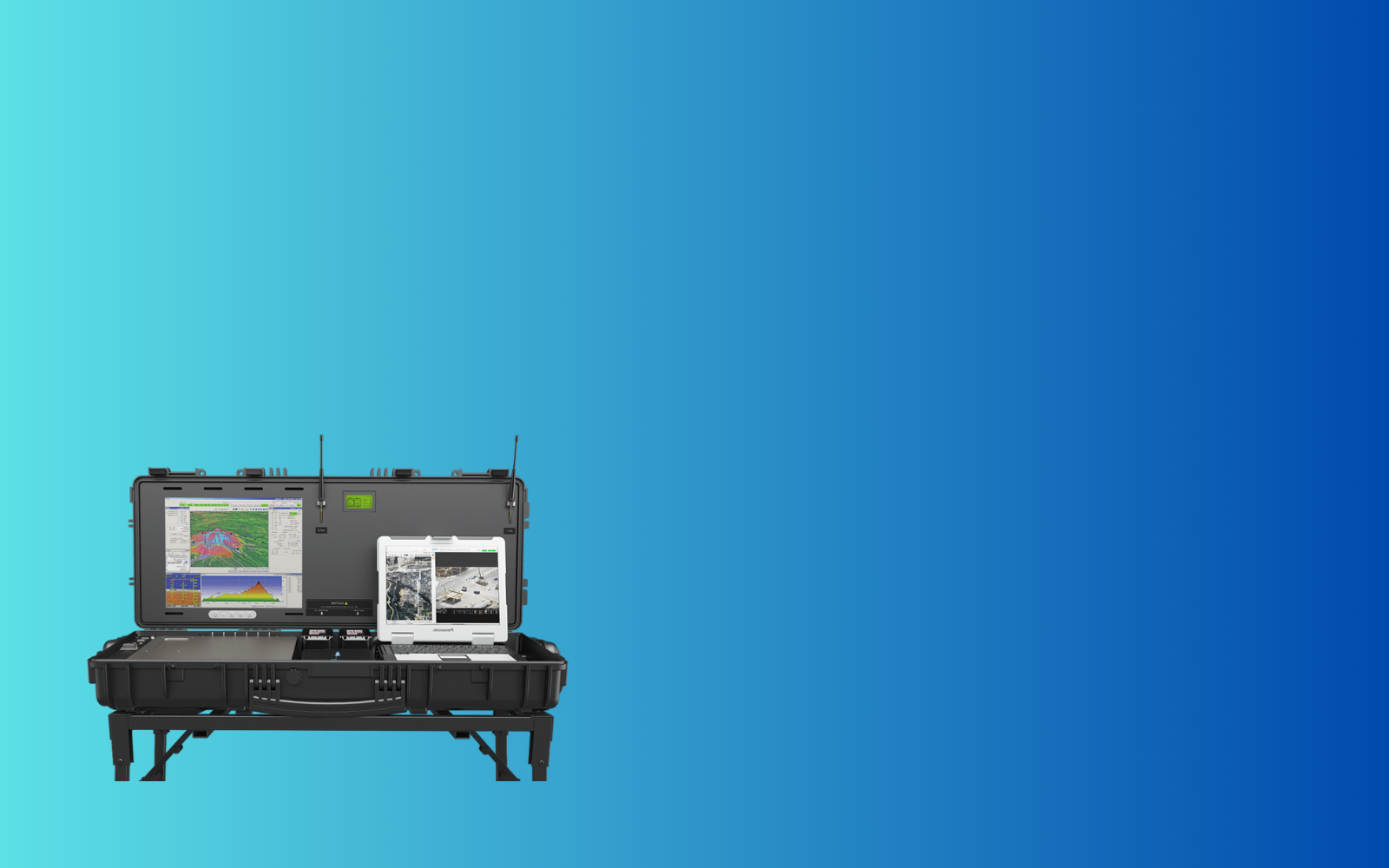
We work with Bay Area startups at the pre-raise stage to close those gaps. That means network assessments, MDM deployment, security hardening, documentation builds, and compliance readiness work, done in the months before investors start asking questions rather than after.
For startups that are already scaling and need ongoing support, our guide to scaling IT after Series A funding covers what comes after the close: the hiring ramp, the infrastructure build-out, and the support model decisions that determine how smoothly the next 18 months go.
If you’re a founder or COO trying to understand where you stand before a raise, reach out to us. We’ll give you an honest read on your current infrastructure and a clear picture of what needs to change, and what doesn’t.