The SME Security Playbook for AI Deployment: From Vulnerability to Advantage
Part 2 of 2: Protecting AI Investments Through Strategic Security
What Most AI Guides Get Wrong About Cybersecurity
In Part 1 of this series, we covered how to deploy GenAI for maximum ROI, from Passive AI integration to Domain-Specific Language Models and AI Agents. But there's something most AI adoption guides quietly skip over, and it's probably the most important thing you need to hear.
Rapid AI deployment without proportional security investment doesn't reduce your risk. It multiplies it.
60% of business and technology leaders now rank cyber risk investment among their top three strategic priorities. For SMEs deploying AI, this isn't a distant concern. It's an immediate operational necessity. The equation is straightforward: AI capabilities multiplied by security vulnerabilities equals net business risk. Miss the security side, and the productivity gains you worked for can disappear in a single incident.
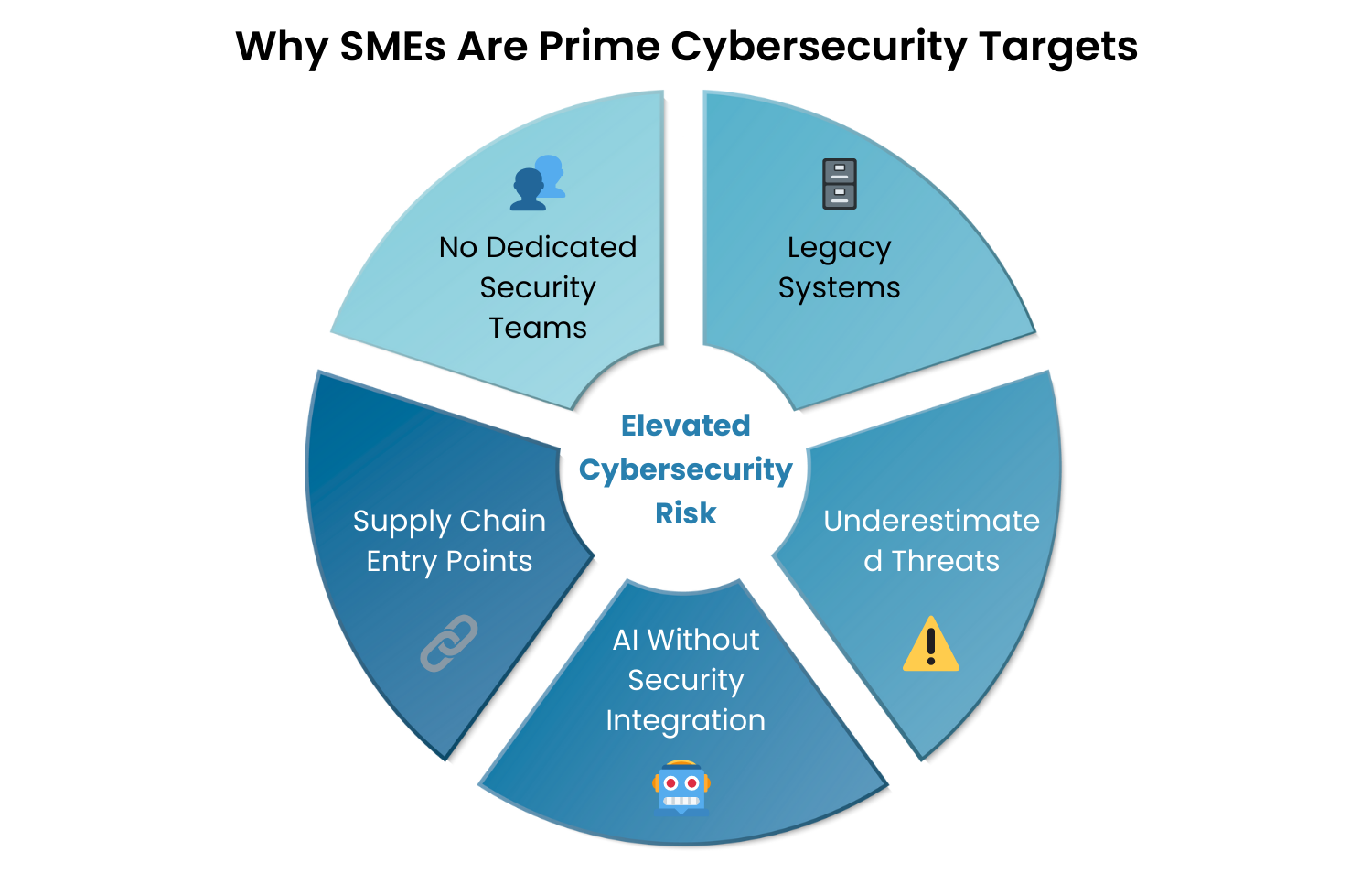
Why Attackers Love Targeting SMEs
It is commonly, and incorrectly, believed that cybercriminals focus their energy on large enterprises with the deepest pockets. It's a reassuring, but dangerously wrong story.
SMEs are increasingly targeted precisely because they're easier. Most don't have dedicated security teams, relying instead on generalist IT staff who juggle security alongside everything else. Budget constraints mean older, unpatched systems stay in production longer than they should, creating known vulnerabilities that attackers can exploit with automated tools at scale. And because many SMEs serve as vendors or partners to larger companies, compromising a smaller supplier is often an attacker's most efficient path into a Fortune 500 network.
There's also a perception problem. Many SME leaders still picture cybercriminals as lone-wolf hackers. The reality is organized operations with nation-state backing and industrial-scale attack infrastructure. They're running businesses, and your business is a target.
Add AI deployment to this picture and the stakes rise further. New AI systems often get stood up quickly, sometimes bypassing the established security protocols that cover the rest of your environment. That creates unmonitored attack surfaces your traditional defenses don't cover.
Yoursecurity posture also matters beyond your own four walls. Customers and partners depend on your security as part of their own risk management. A breach at your company can become their problem too.
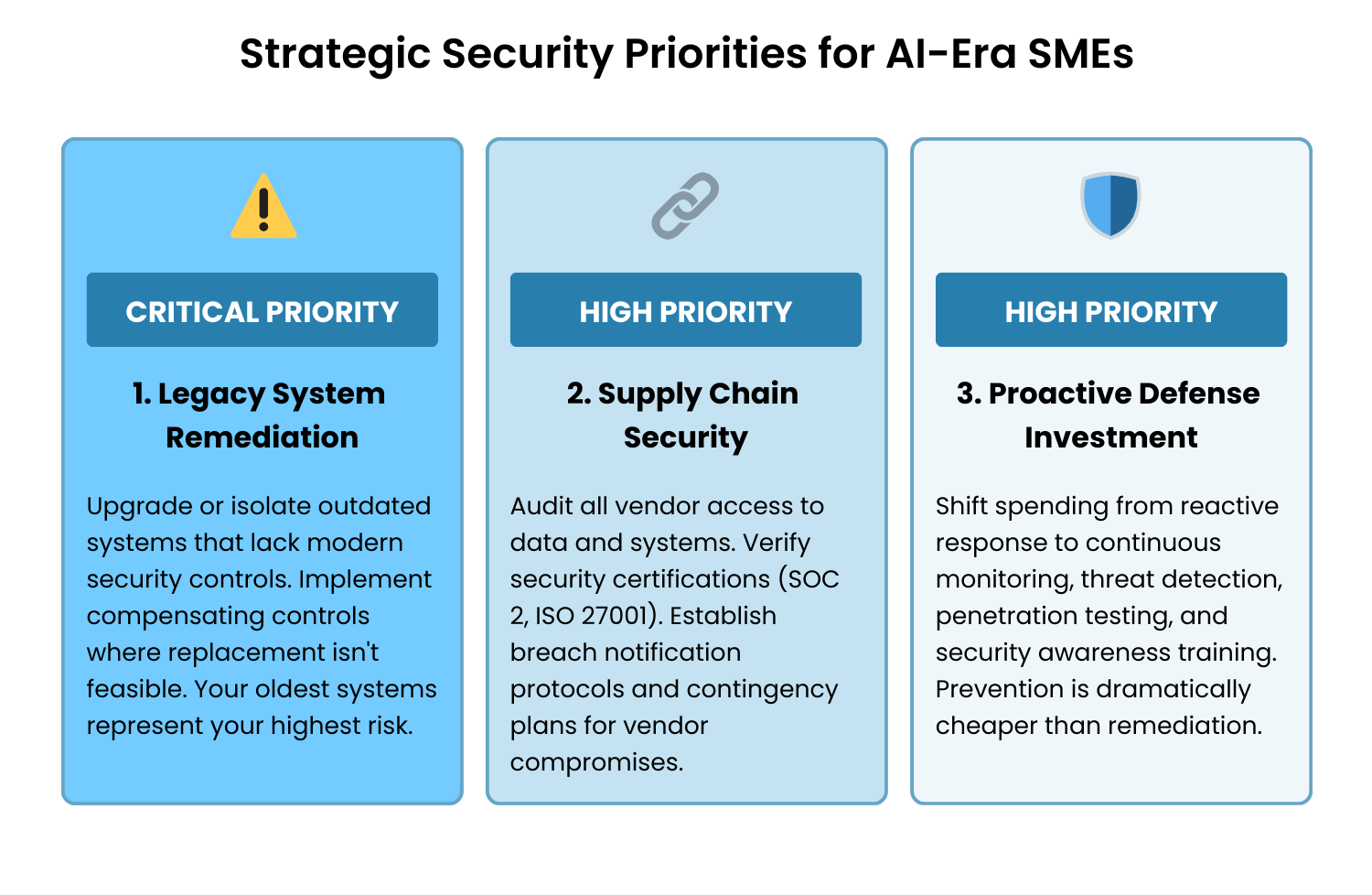
3 Cybersecurity Priorities Every SME Should Focus On
Effective cybersecurity for SMEs isn't about matching enterprise budgets. It's about putting your resources where they'll have the most impact. In our experience working with Bay Area businesses, there are three priorities that consistently make the biggest difference.
1. Fix Your Oldest Systems First
Your legacy applications are almost always your highest-risk systems. They run on outdated operating systems that no longer receive security patches. They use authentication methods that were considered acceptable a decade ago but are trivially bypassed today. They often lack any logging or monitoring capabilities, meaning you wouldn't know if something went wrong. And they frequently store data in formats that don't support modern encryption.
The fix depends on what you're dealing with. Some legacy applications are worth upgrading or replacing with modern, often cloud-based alternatives that have security built in. Others can be isolated from your network and AI integrations through segmentation, containing the blast radius if something goes wrong. For systems that genuinely can't be touched, compensating controls like additional monitoring, strict access restrictions, and encryption layers can reduce the risk.
Legacy remediation often feels expensive until you compare it to the cost of a breach: forensics, legal fees, regulatory fines, customer notifications, reputational damage, and lost revenue during downtime. Prevention is dramatically cheaper than response, every time.
2. Audit Your Vendor Ecosystem
AI implementations typically involve multiple vendors: cloud providers, AI platforms, data processors, integration partners, and managed service providers. Each one is a potential entry point for attackers.
Go through your vendor relationships and ask some hard questions. What data does each vendor actually access? Do they hold SOC 2, ISO 27001, or industry-specific certifications? How would you know if a vendor was compromised? And if a critical vendor suffered a breach tomorrow, do you have a plan?
Your contracts matter here too. Security requirements, breach notification timelines, liability provisions, and audit rights should all be in writing. When technical controls eventually fail somewhere in your supply chain, your legal agreements are your last line of defense.
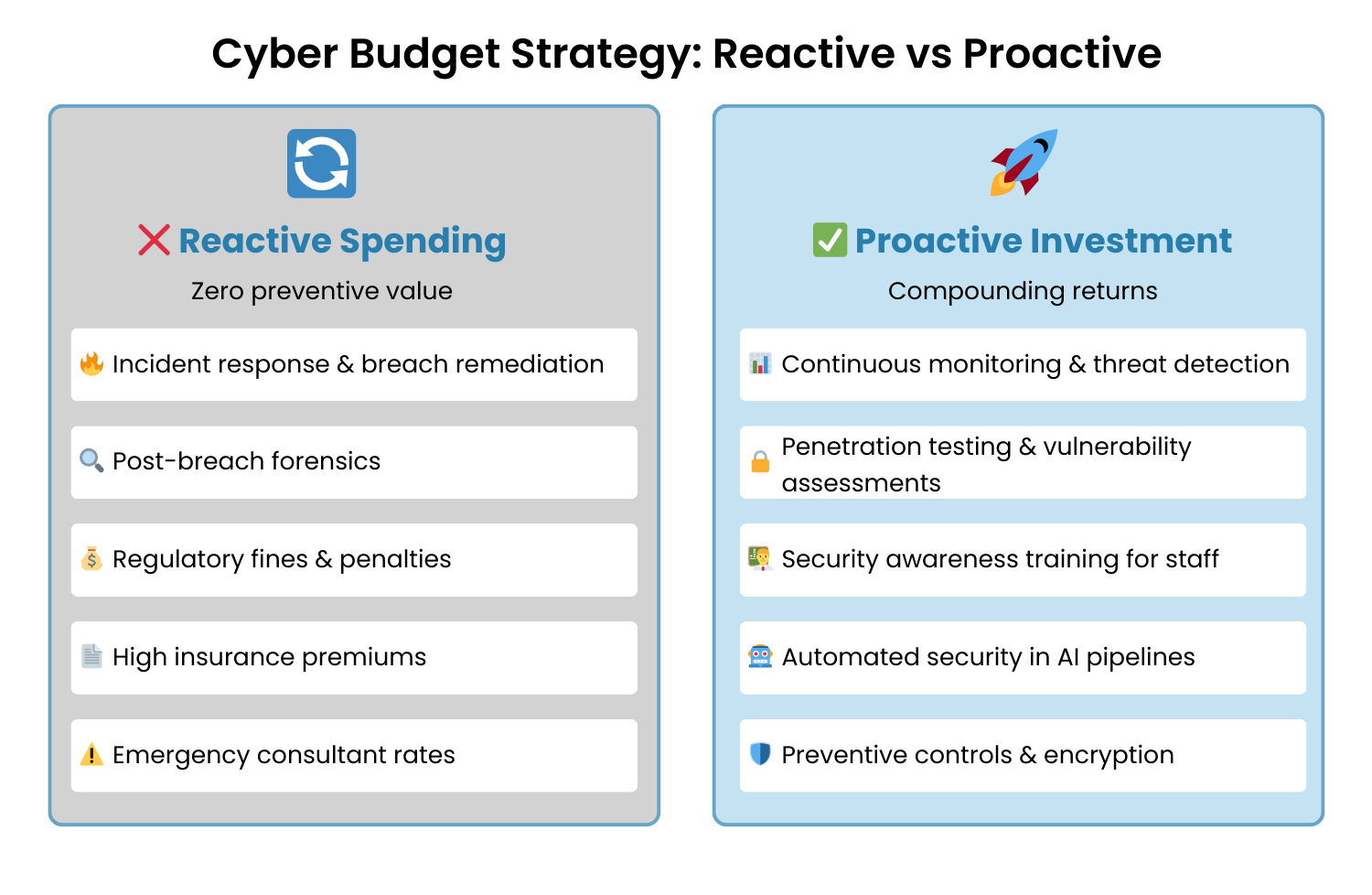
3. Stop Playing Defense After the Fact
While 78% of organizations plan to increase their cyber budgets in 2026, the question isn't how much you spend. It's where you spend it.
Reactive spending, on incident response, breach remediation, and regulatory fines, returns nothing. It's the cost of having already lost. Proactive spending, on monitoring, testing, and training, compounds in value over time.
Invest in continuous monitoring and threat detection that flags unusual activity before it becomes a breach. Run regular penetration testing and vulnerability assessments so you find your weaknesses before attackers do. Put real resources into security awareness training for all staff, because human error causes most breaches and your people are both your biggest vulnerability and your most effective first line of defense. And build security testing directly into your AI development pipelines so it's baked in from the start.
The mindset shift that makes this all click: cybersecurity is operational infrastructure, not a discretionary IT expense. You wouldn't skip building maintenance to save money. Security deserves the same logic.
How Managed Security Services Help SMEs Close the Gap
The single biggest barrier to good cybersecurity for SMEs isn't technology. It's expertise. The global cybersecurity talent shortage means you simply cannot compete with enterprise salaries for specialized security professionals. And one generalist IT person covering everything is not a security team.
Managed Security Service Providers (MSSPs) are how most SMEs solve this problem. A single MSSP contract gives you access to security analysts, threat researchers, incident responders, and compliance specialists, all without the overhead of full-time salaries and benefits.
Beyond the talent access, MSSPs provide 24/7 monitoring and response coverage that no SME IT team can realistically sustain. They bring economies of scale on security tools and threat intelligence, aggregating data across multiple clients so you get enterprise-grade visibility. And because they can be operationally stood up within weeks rather than months, you can get protected quickly.
Choosing the right MSSP matters, though. Outsourcing your security operations doesn't mean outsourcing accountability. Your organization remains responsible for outcomes. Look for providers with genuine industry-specific experience and relevant certifications. Make sure you'll receive regular, understandable reports on your security posture, not technical jargon that obscures problems. Define clear SLAs around detection and response times in concrete hours and minutes. And find a provider who functions as an extension of your team rather than a distant vendor you hear from only when things go wrong.
Watch out for red flags: providers who can't explain their services in plain business terms, contracts that lock you in without performance guarantees, anyone who promises "complete protection," and services that don't include regular vulnerability assessments.
The Data Integrity Crisis Hiding in Plain Sight
Here's a number that tends to surprise people: only 6% of organizations have fully implemented essential data risk measures across their entire enterprise. Not advanced security technologies. Just the basics.
For SMEs deploying AI, this gap is existential. AI models require access to substantial data, and AI features often process or expose that data in new ways your existing controls weren't designed to handle. Without the fundamentals in place, AI deployment multiplies your exposure rather than your business value.
So what are those fundamentals?
Start with data classification. Not everything requires maximum security, but you need to know what does. Customer PII, financial records, payment data, intellectual property, trade secrets, strategic plans, and employee records all belong in a protected category. Create a simple classification scheme, something like Public, Internal, Confidential, and Restricted, and apply it consistently.
Map where your data actually lives. Where is sensitive data stored? Which systems process it? Who has access to it, including your AI systems and vendors? How does it travel across your environment through email, APIs, and file transfers? You can't protect what you haven't mapped.
Encrypt sensitive data at rest and in transit. Modern cloud platforms make this relatively straightforward through built-in features. There's no good reason not to have it in place.
Control and monitor access. Role-based access controls ensure people can only reach the data they genuinely need for their role. Pair that with monitoring for unusual access patterns: failed login attempts, access outside normal hours, bulk data downloads, or access to systems outside a user's normal scope. These are your early warning signals.
Clean up your data regularly. The less data you hold, the smaller your attack surface. Define retention periods based on legal requirements, operational needs, and customer privacy expectations. Then automate deletion so policies are actually followed, not just documented.
Combine data loss prevention (DLP) controls and access management with these fundamentals, and you have a data security program that's genuinely fit for AI deployment.
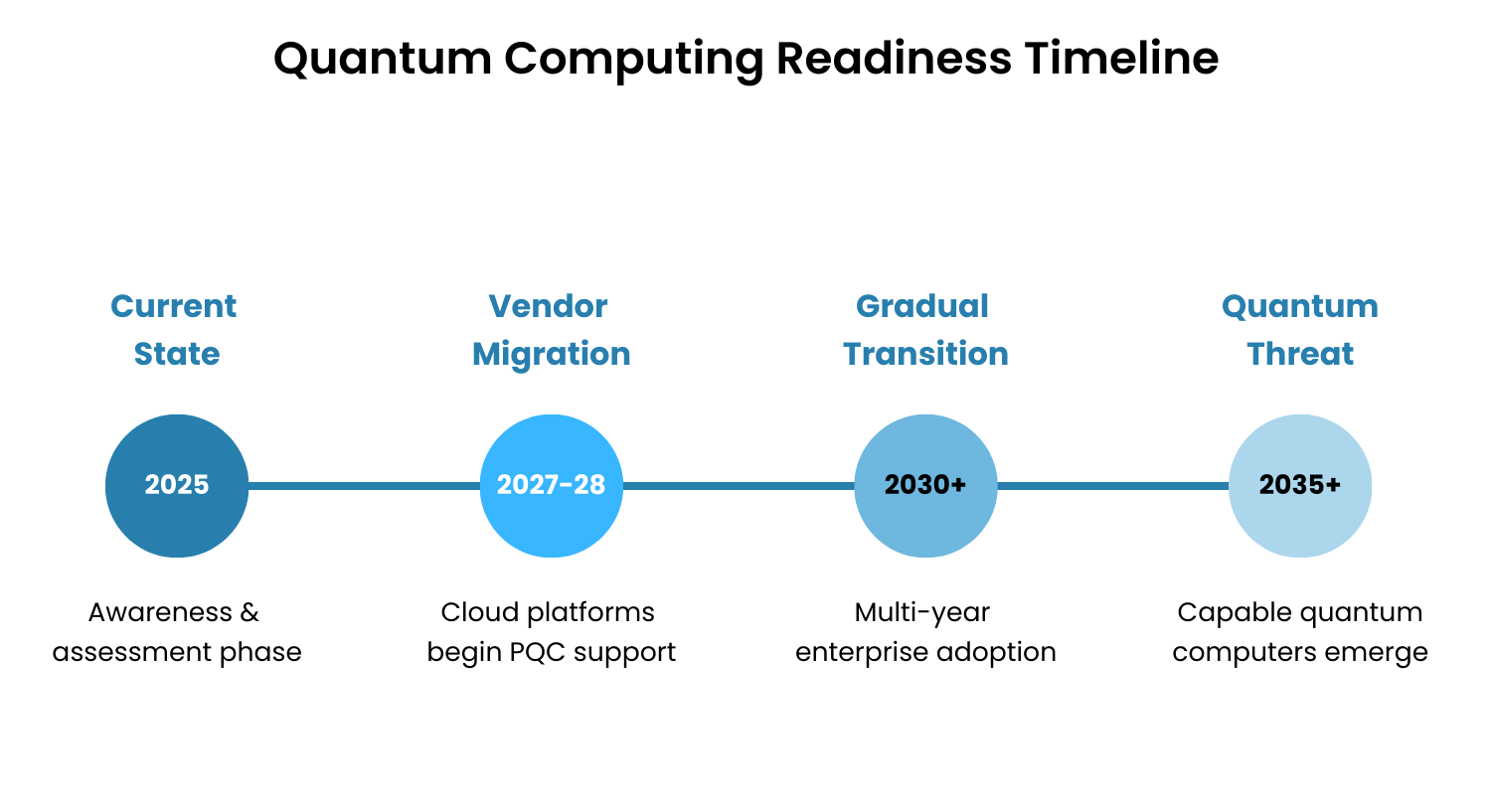
A Note on Quantum Computing: What You Actually Need to Worry About
Quantum computing will eventually break the cryptographic algorithms protecting most digital communications and data. That's a real threat. But the timeline matters: quantum computers capable of breaking current encryption likely won't exist for another decade.
The wrinkle is something called "harvest now, decrypt later" attacks. Adversaries are already collecting encrypted data today with the intention of decrypting it once quantum capability matures. For organizations with data that must stay confidential for a decade or more, this creates strategic implications right now.
Post-Quantum Cryptography (PQC) standards are being developed in response. NIST has published initial algorithms, and migration is beginning across the industry.
For most SMEs, the practical approach is straightforward. Identify what data must remain confidential for ten or more years, and assess whether its eventual exposure would cause serious business harm. Track when your software and cloud providers plan to support PQC standards, and align your migration with theirs rather than running a separate internal project. And unless you're handling state secrets or highly sensitive long-term intellectual property, keep your focus where the near-term risk actually is: traditional cybersecurity threats that are happening today.
Data Sovereignty: The Regulation Coming Your Way
An emerging complication worth getting ahead of: 65% of governments worldwide are expected to introduce requirements by 2028 mandating that certain data and systems remain within national borders or use domestically-controlled infrastructure.
For SMEs operating internationally, this affects vendor selection, infrastructure costs, and regulatory risk in ways that aren't always obvious until you're already non-compliant. Some cloud and AI vendors simply don't support all regions, which limits your options. Multi-region deployments to satisfy sovereignty requirements increase operational complexity. And domestic vendors may gain regulatory advantages over international competitors in some markets.
When evaluating AI and cloud vendors, ask them directly: in which countries do you maintain data centers? How do you ensure data doesn't leave specified jurisdictions? What compliance certifications do you hold for different regions? And how are you planning to adapt as sovereignty requirements tighten?
Vendors who've invested early in distributed, compliant architectures will be lower-risk partners as this landscape evolves.
Security as Competitive Advantage
Here's a reframe worth sitting with: security isn't a cost center. It's a competitive differentiator.
In markets where AI adoption is accelerating, customers and enterprise partners increasingly evaluate vendors based on security posture. Organizations that can demonstrate robust data protection, clear compliance frameworks, proactive threat management, and transparent incident response procedures win business away from competitors who can't.
When large organizations are evaluating you as a vendor, they conduct security assessments. Strong security shortens those sales cycles. In regulated industries like healthcare, finance, and government contracting, security capabilities aren't a differentiator, they're a prerequisite. And when multiple vendors offer comparable capabilities, security posture becomes the tiebreaker.
Done right, your security investment pays for itself in business won and business protected.
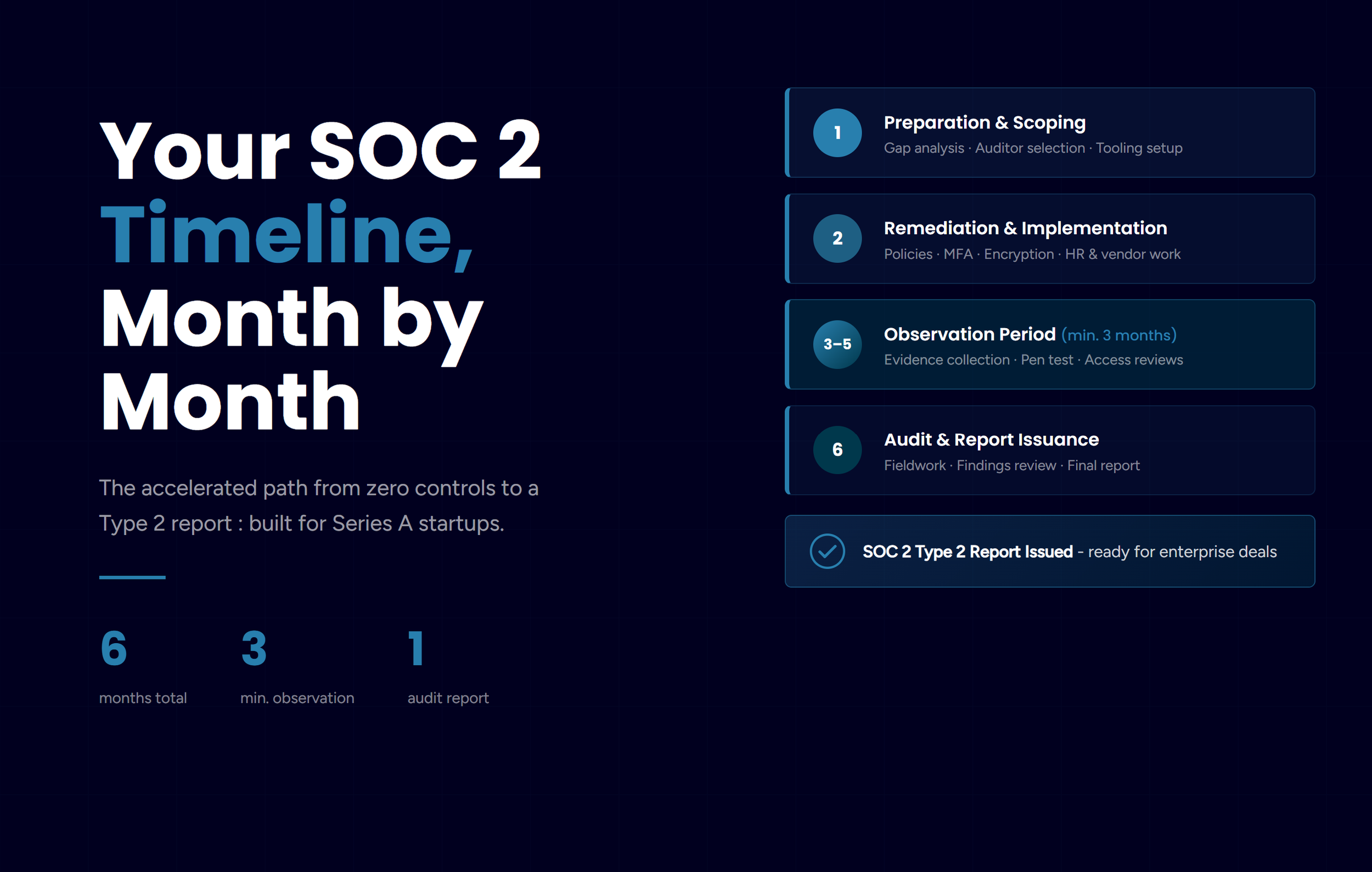
Your SME AI Security Roadmap
Based on everything covered, here's your security roadmap aligned with AI deployment:
Immediate (Weeks 1-4)
Conduct a security audit: Identify legacy systems and unpatched vulnerabilities,
Map data flows: Document where sensitive data lives and who can access it,
Evaluate MSSP options: Get quotes and capabilities from 3-5 providers, and
Implement basic encryption: Enable encryption on cloud storage and communications.
Near-term (Months 2-3)
Select and onboard MSSP: Establish 24/7 monitoring and response,
Remediate critical vulnerabilities: Fix the highest-risk legacy system issues,
Implement access controls: Deploy role-based access and multi-factor authentication, and
Audit vendor security: Review contracts and security postures of critical vendors.
Medium-term (Months 4-6)
Develop a data classification scheme: Categorize all organizational data,
Implement DLP controls: Prevent unauthorized data exfiltration,
Conduct penetration testing: Identify weaknesses before attackers do, and
Train staff on security awareness: Build a human firewall against social engineering.
Ongoing
Monitor and review: Regular security posture assessments,
Update and patch: Systematic vulnerability management,
Test incident response: Quarterly tabletop exercises, and
Track emerging threats: Stay informed on quantum, AI security, and geopolitical developments.
Integration With AI Deployment
Security and AI deployment aren't parallel workstreams. They're integrated components of operational capability.
When you're rolling out Passive AI in existing tools, verify that the AI features maintain your existing security controls. AI capabilities shouldn't bypass your authentication, logging, or data protection. When adopting Domain-Specific Models, understand where your data goes for training or inference and make sure vendors can't use your data to train models for competitors. When implementing AI Agents, be especially careful: autonomous agents act on your behalf with potentially wide-ranging permissions, and they need strict scopes and careful monitoring from day one. And when using Synthetic Data, verify that it truly anonymizes sensitive information and can't be reverse-engineered to reveal source data.
The factory floor analogy from Part 1 applies perfectly here. Security is the reinforced foundation and the locked gates. Even the best new machinery won't protect you if the foundation is weak or the gates are left open.
The Complete Picture
The organizations that will thrive in the AI era aren't necessarily those with the most sophisticated AI or the largest security budgets. They're the ones who treat AI capability and security investment as a single integrated strategy rather than two separate conversations.
Security enables AI adoption by creating the trust foundation that customers, partners, and employees need to embrace AI-powered operations. AI adoption demands security investment because new capabilities create new attack surfaces. Together, they create a competitive advantage that compounds over time.
Miss either side, and the equation fails.
Series Wrap-Up
Across both parts of this series, here's what we've covered.
Part 1 covered why "wait and see" means competitive obsolescence, ROI-focused deployment starting with Passive AI, the key capabilities of DSLMs, AI Agents, and Synthetic Data, and how to optimize resources through public support programs and strategic partnerships.
Part 2 covered why SMEs are increasingly targeted, the three security priorities that matter most, how MSSPs solve the skills gap, data integrity fundamentals, and emerging threats including quantum computing and data sovereignty.
The unified message: the window for strategic AI adoption with integrated security is open right now. Organizations that execute on both capability and protection will build advantages that compound. Those waiting for perfect conditions will find the market has moved on without them.
At Jones IT, we've helped hundreds of Bay Area businesses secure their infrastructure and data as they implement new technologies. Reach out if you'd like to talk through your specific situation.